Chegg sued by FTC after suffering four data breaches within 3 yearsThe U.S. Federal Trade Commission (FTC) has sued education technology company Chegg after it exposed the sensitive information...
Author: admin
Single chip transfers the entire internet’s traffic in a second
Single chip transfers the entire internet’s traffic in a secondEXECUTIVE SUMMARY: A single chip has managed a transfer of over a petabit-per-second, according to new research...
NSA shares supply chain security tips for software suppliers
NSA shares supply chain security tips for software suppliersNSA, CISA, and the Office of the Director of National Intelligence (ODNI) have shared a new set of...
The art of cyber threat intelligence: How to identify & fight potential attackers
The art of cyber threat intelligence: How to identify & fight potential attackersDave is an experienced security engineer and business professional, leading Guardian Digital in providing...
Mozilla Firefox fixes freezes caused by new Windows 11 feature
Mozilla Firefox fixes freezes caused by new Windows 11 featureMozilla has fixed a known issue causing the Firefox web browser to freeze when copying text on...
How to become a revenue-generating CIO
How to become a revenue-generating CIOEXECUTIVE SUMMARY: Businesses are increasingly looking to IT leaders as C-suite entrepreneurs who can structure innovative efforts and scale emerging ideas....
States Spent Millions On Deloitte’s ‘Anti-Fraud’ Covid Unemployment Systems. They Suffered Billions In Fraud.
States Spent Millions On Deloitte’s ‘Anti-Fraud’ Covid Unemployment Systems. They Suffered Billions In Fraud.Contenido de la entradaLeer másProofpoint News Feed
Addressing the cyber security talent shortage: APAC and beyond
Addressing the cyber security talent shortage: APAC and beyondEXECUTIVE SUMMARY: Globally, in the last year, the cyber security workforce has seen the greatest growth in the...
Click or treat? Scary good security tips for a happy Halloween!
Click or treat? Scary good security tips for a happy Halloween!EXECUTIVE SUMMARY: Halloween is a widely celebrated holiday in the U.S. Ninety-three percent of Americans intend...
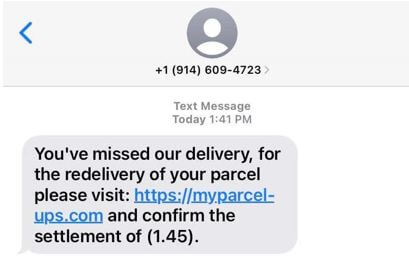
SMiShing: Short, sweet and evil
SMiShing: Short, sweet and evilBy Miguel Angulo, Channel Engineer and Evangelist, Check Point Software. Have you ever received a text message from someone you don’t know,...
Ransomware: ‘Amateur’ Tactics Lead Fewer Victims to Pay
Ransomware: 'Amateur' Tactics Lead Fewer Victims to PayCriminals Shooting Themselves in the Foot With Faulty Decryptors, Re-ExtortionMany ransomware-wielding attackers - including big-name groups - have been...
North Korea Disguising Android Malware as Legitimate Apps
North Korea Disguising Android Malware as Legitimate AppsApps Masquerade as Google Security Plug-In and Document ViewerNorth Korean state hacking group Kimsuky is developing Android malware targeted...
Honeywell’s James DeLuccia on Product Security vs IT Defense
Honeywell's James DeLuccia on Product Security vs IT DefenseConsistency Is the Objective in IT Security, But Product Security Must Be FlexibleOrganizations expect the IT security landscape...
Second Health Entity Reports Breach Tied to Meta Pixel Use
Second Health Entity Reports Breach Tied to Meta Pixel UseNorth Carolina Organization Also Facing Pending Privacy Lawsuit Related to PixelA second healthcare entity is self-reporting its...
Cyberattack Hits German Copper Manufacturing Giant
Cyberattack Hits German Copper Manufacturing GiantAurubis Shuts Down IT Systems at Various Productions LocationsOne of the world's largest copper smelters disclosed it underwent a cyberattack, stating...
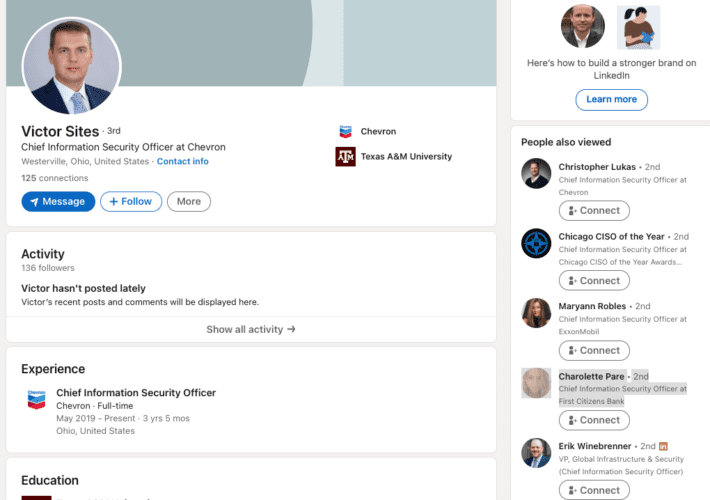
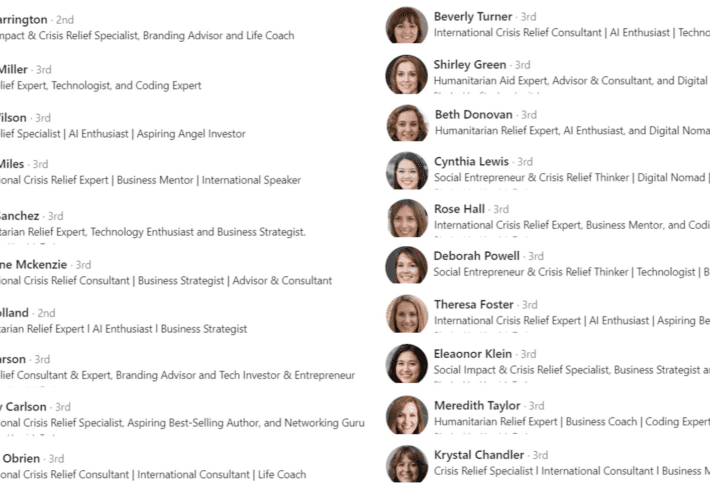
Fake CISO Profiles on LinkedIn Target Fortune 500s
Fake CISO Profiles on LinkedIn Target Fortune 500sSomeone has recently created a large number of fake LinkedIn profiles for Chief Information Security Officer (CISO) roles at...
Microsoft: Two New 0-Day Flaws in Exchange Server
Microsoft: Two New 0-Day Flaws in Exchange ServerMicrosoft Corp. is investigating reports that attackers are exploiting two previously unknown vulnerabilities in Exchange Server, a technology many...
Glut of Fake LinkedIn Profiles Pits HR Against the Bots
Glut of Fake LinkedIn Profiles Pits HR Against the BotsA recent proliferation of phony executive profiles on LinkedIn is creating something of an identity crisis for...
Report: Big U.S. Banks Are Stiffing Account Takeover Victims
Report: Big U.S. Banks Are Stiffing Account Takeover VictimsWhen U.S. consumers have their online bank accounts hijacked and plundered by hackers, U.S. financial institutions are legally...
Microsoft Patch Tuesday, October 2022 Edition
Microsoft Patch Tuesday, October 2022 EditionMicrosoft today released updates to fix at least 85 security holes in its Windows operating systems and related software, including a...
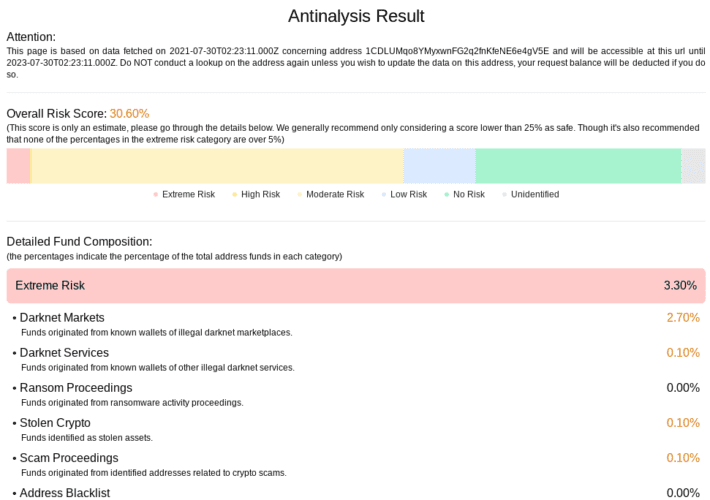
Anti-Money Laundering Service AMLBot Cleans House
Anti-Money Laundering Service AMLBot Cleans HouseAMLBot, a service that helps businesses avoid transacting with cryptocurrency wallets that have been sanctioned for cybercrime activity, said an investigation...
Understanding The True Financial Risk of Ransomware Attacks
Understanding The True Financial Risk of Ransomware AttacksBy Mark Guntrip, Senior Director of Cybersecurity Strategy at Menlo Security The European Union Agency for Cybersecurity (ENISA) […]...
Using Identity for Access Is a Huge Cybersecurity Risk
Using Identity for Access Is a Huge Cybersecurity RiskWhy FIDO’s proposal to use identification for cyber access opens more security vulnerabilities for threat actors to exploit...
What We Have Learnt Building a Global Security Conscious Culture
What We Have Learnt Building a Global Security Conscious CultureBy Nicola McCoy, Chief Information Security Officer at RSM International The growing cyber risk is impacting global...
Security startups to watch for 2022
Security startups to watch for 2022The problems cybersecurity startups attempt to solve are often a bit ahead of the mainstream. They can move faster than most...
Why CSOs Are Decluttering Their Cybersecurity Toolboxes
Why CSOs Are Decluttering Their Cybersecurity ToolboxesBy Motti Elloul, VP Customer Success and Incident Response, Perception Point Slashed budgets, staff shortages, and the significant […] The...
Why Cyber-Attacks on The Cloud Are Rising and How to Prevent Them
Why Cyber-Attacks on The Cloud Are Rising and How to Prevent ThemIncrease in implementation of cloud by government and private organizations to improve efficiency and save...
Why Throwing Money at Cybersecurity Doesn’t Work
Why Throwing Money at Cybersecurity Doesn’t WorkBy Zac Amos, Features Editor, ReHack Cyberattacks have become more frequent and debilitating as the work gets more […] The...
Cybersecurity For Our Nation’s Critical Infrastructure
Cybersecurity For Our Nation’s Critical InfrastructureHow you can do your part to protect mission-critical assets and services By Kamil Karmali, Global Commercial Manager, […] The post...
Women in Cryptology – USPS celebrates WW2 codebreakers
Women in Cryptology – USPS celebrates WW2 codebreakersWhat did you do in the war, Mom? Oh, y'know, a bit of this and that...Leer másNaked SecurityWhat did...