Source: thehackernews.com – Author: . Jan 15, 2024NewsroomWebsite Security / Vulnerability Thousands of WordPress sites using a vulnerable version of the Popup Builder plugin have been...
Author: admin
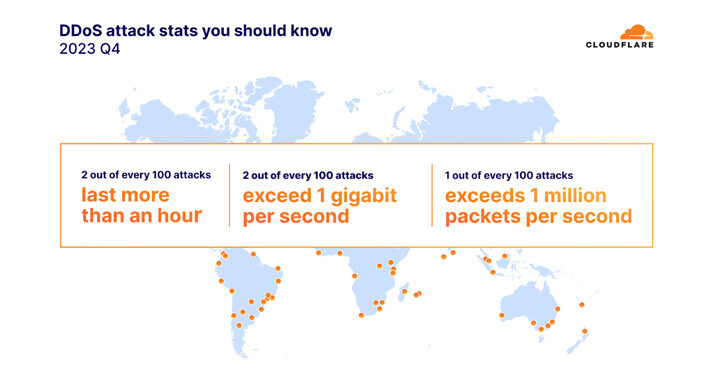
DDoS Attacks on the Environmental Services Industry Surge by 61,839% in 2023 – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 15, 2024NewsroomServer Security / Cyber Attack The environmental services industry witnessed an “unprecedented surge” in HTTP-based distributed denial-of-service (DDoS) attacks,...
New Findings Challenge Attribution in Denmark’s Energy Sector Cyberattacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 14, 2024NewsroomCyber Attack / Vulnerability The cyber attacks targeting the energy sector in Denmark last year may not have had...
Former Secretary of State Mike Pompeo Joins Cyabra Board of Directors – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE Cyabra, the leading counter-disinformation company, is pleased to announce the appointment of 70th Secretary of State Mike Pompeo to its...
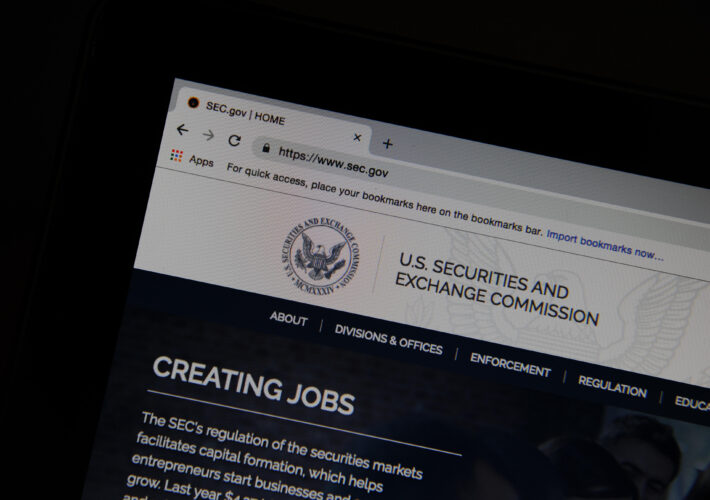
SEC X Account Hack Draws Senate Outrage – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading 2 Min Read Source: Louisa Svenson via Alamy Stock Photo Following the Securities and Exchange Commission’s X...
Cybersecurity Incidents Consistently Increase in UAE – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nicholas Fearn, Contributing Writer Source: 3D generator via Alamy Stock Photo During the past two years, the vast majority of United Arab...
Critical RCE Vulnerability Uncovered in Juniper SRX Firewalls and EX Switches – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 13, 2024NewsroomVulnerability / Network Security Juniper Networks has released updates to fix a critical remote code execution (RCE) vulnerability in...
29-Year-Old Ukrainian Cryptojacking Kingpin Arrested for Exploiting Cloud Services – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 13, 2024NewsroomCryptojacking / Cloud Security A 29-year-old Ukrainian national has been arrested in connection with running a “sophisticated cryptojacking scheme,”...
Nation-State Actors Weaponize Ivanti VPN Zero-Days, Deploying 5 Malware Families – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 12, 2024NewsroomVulnerability / Threat Intelligence As many as five different malware families were deployed by suspected nation-state actors as part...
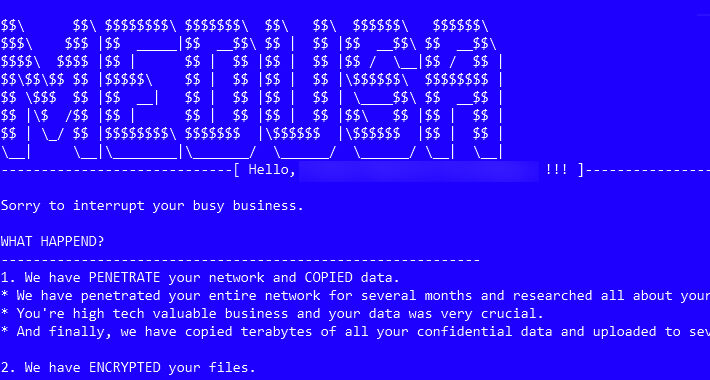
Medusa Ransomware on the Rise: From Data Leaks to Multi-Extortion – Source:thehackernews.com
Source: thehackernews.com – Author: . The threat actors associated with the Medusa ransomware have ramped up their activities following the debut of a dedicated data leak...
Applying the Tyson Principle to Cybersecurity: Why Attack Simulation is Key to Avoiding a KO – Source:thehackernews.com
Source: thehackernews.com – Author: . Picture a cybersecurity landscape where defenses are impenetrable, and threats are nothing more than mere disturbances deflected by a strong shield....
Urgent: GitLab Releases Patch for Critical Vulnerabilities – Update ASAP – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 12, 2024NewsroomDevSecOps / Software security GitLab has released security updates to address two critical vulnerabilities, including one that could be...
Claroty Welcomes Former US National Cyber Director Chris Inglis to Advisory Board – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE NEW YORK, Jan. 10, 2024 /PRNewswire/ — Claroty, the cyber-physical systems protection company, today announced the appointment of Chris Inglis, former U.S. National Cyber...
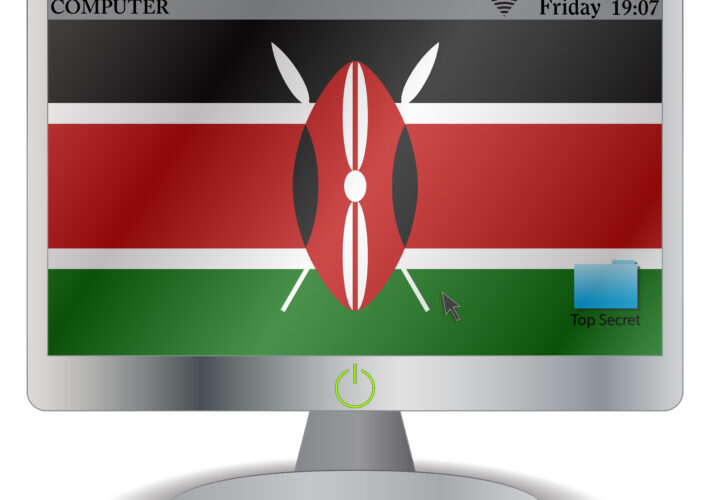
Kenya Issues New Guidance for Protecting Personal Data – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: David Makings via Alamy Stock Photo Kenya’s Office of the Data Protection Commissioner (ODPC) this week issued...
War or Cost of Doing Business? Cyber Insurers Hashing Out Exclusions – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Drugmaker Merck’s long legal battle with its insurance companies over the damages caused to its business by the...
New Developer Tools Necessary to Boost Passkey Adoption – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Artemis Diana via Alamy The passwordless technology known as passkeys remains esoteric, far from widespread adoption, and...
Cryptominers Targeting Misconfigured Apache Hadoop and Flink with Rootkit in New Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 12, 2024NewsroomCryptocurrency / Malware Cybersecurity researchers have identified a new attack that exploits misconfigurations in Apache Hadoop and Flink to...
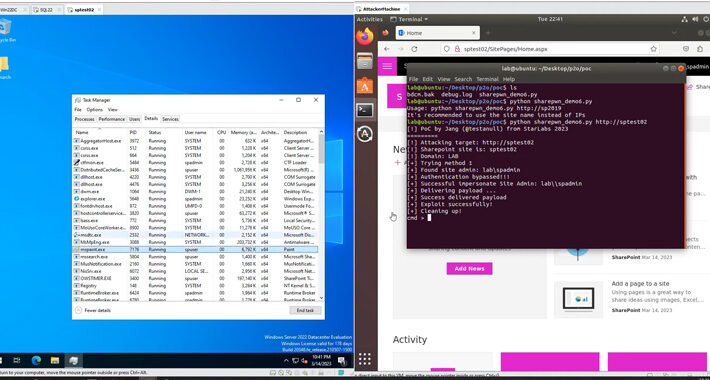
Act Now: CISA Flags Active Exploitation of Microsoft SharePoint Vulnerability – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 12, 2024NewsroomCyber Attack / Vulnerability The U.S. Cybersecurity and Infrastructure Security Agency (CISA) has added a critical security vulnerability impacting...
Mandiant, SEC Lose Control of X Accounts Without 2FA – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading 2 Min Read Source: Techa Tungateja via Alamy Stock Photo Upon review, Google’s cybersecurity operation at Mandiant...
The Future of IT: Info-Tech LIVE 2024 Conference Announced for September – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE TORONTO, Jan. 9, 2024 /PRNewswire/ – Info-Tech Research Group, a global leader in IT research and advisory, has announced that its flagship...
Volt Typhoon Ramps Up Malicious Activity Against Critical Infrastructure – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: NicoElNino via Shutterstock China-backed cyber espionage group Volt Typhoon is systematically targeting legacy Cisco devices in a...
OpenAI’s New GPT Store May Carry Data Security Risks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: SOPA Images Limited via Alamy Stock Photo A new kind of app store for ChatGPT may expose...
Move Over, APTs: Cybercriminals Now Target Critical Infrastructure Too – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: hoch2wo via Alamy Stock Photo A “crimewave” of mass exploitation of Zyxel firewall devices...
Ivanti Researchers Report Two Critical Zero-Day Vulnerabilities – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading 1 Min Read Source: Alexander Tolstykh via Shutterstock Ivanti researchers this week flagged two zero-day vulnerabilities...
Critical Start Implements Cyber Risk Assessments With Peer Benchmarking and Prioritization Engine – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE PLANO, Texas, Jan. 11, 2024 /PRNewswire/ — Today, Critical Start, a leading provider of Managed Detection and Response (MDR) cybersecurity solutions and pioneer...
Fake Recruiters Defraud Facebook Users via Remote-Work Offers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Prostock Studio via Alamy Stock Photo A fresh wave of job scams is spreading on Meta’s Facebook...
Orca Security Appoints Raf Chiodo As Chief Revenue Officer – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE PORTLAND, Ore. – January 10, 2024 – Orca Security, the leader in agentless cloud security, today announced the appointment of Raf...
Threat Actors Increasingly Abusing GitHub for Malicious Purposes – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 11, 2024NewsroomCybersecurity / Software Security The ubiquity of GitHub in information technology (IT) environments has made it a lucrative choice...
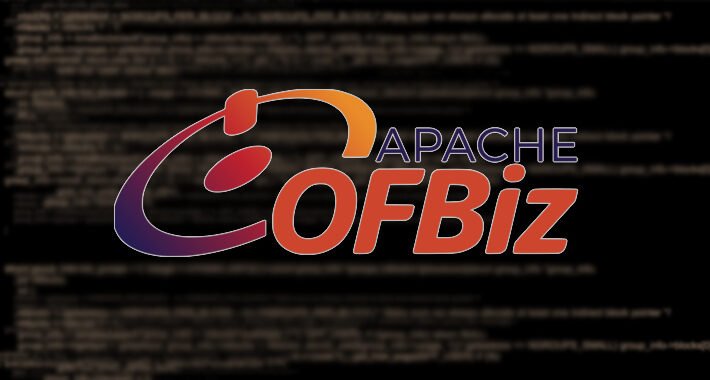
New PoC Exploit for Apache OfBiz Vulnerability Poses Risk to ERP Systems – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 11, 2024NewsroomVulnerability / Cyber Attack Cybersecurity researchers have developed a proof-of-concept (PoC) code that exploits a recently disclosed critical flaw...
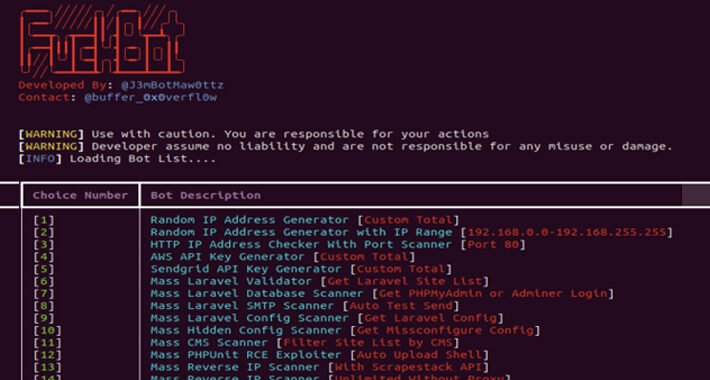
New Python-based FBot Hacking Toolkit Aims at Cloud and SaaS Platforms – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 11, 2024NewsroomCloud Security / Cyber Attacks A new Python-based hacking tool called FBot has been uncovered targeting web servers, cloud...