Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Zhanna Hapanovich via Shutterstock CISOs are increasingly being asked to assume the responsibilities of what would normally...
Author: admin
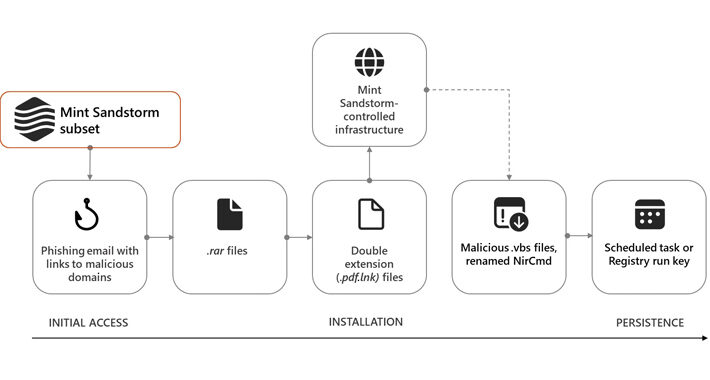
Microsoft: Iran’s Mint Sandstorm APT Blasts Educators, Researchers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Zoonar GmbH via Alamy Stock Photo The Iran-linked Mint Sandstorm group is targeting Middle Eastern affairs specialists...
iPhone, Android Ambient Light Sensors Allow Stealthy Spying – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer Source: Yalcin Sonat via Alamy Stock Photo The ambient light sensors typically employed in smart devices for adjusting...
First Step in Securing AI/ML Tools Is Locating Them – Source: www.darkreading.com
Source: www.darkreading.com – Author: Fahmida Y. Rashid, Managing Editor, Features, Dark Reading Source: Andrey Popov via Adobe Stock Photo The growing number of applications incorporating artificial...
Experts Warn of macOS Backdoor Hidden in Pirated Versions of Popular Software – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 19, 2024NewsroomMalware / Endpoint Security Pirated applications targeting Apple macOS users have been observed containing a backdoor capable of granting...
Nigerian Businesses Face Growing Ransomware-as-a-Service Trade – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Leyden, Contributing Writer Source: Pablo Lagarto via Alamy Stock Photo Ransomware-as-a-service looks set to fuel an increase in attack in Nigeria,...
Google: Russia’s ColdRiver APT Unleashes Custom ‘Spica’ Malware – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: imageBROKER.com GmbH & Co. KG via Alamy Stock Photo The Russia-backed advanced persistent threat...
Threat Actors Team Up for Post-Holiday Phishing Email Surge – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: devilmaya via Alamy Stock Photo Last week, two different threat actors teamed up to send thousands of...
Citrix Discovers 2 Vulnerabilities, Both Exploited in the Wild – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading 2 Min Read Source: Monticello via Shutterstock Two vulnerabilities have been found in NetScaler ADC and...
Cybercrooks Target Docker Containers With Novel Pageview Generator – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading 2 Min Read Source: Bob Sharples via Alamy Stock Photo Container-focused cyberattackers have a brand-new...
Npm Trojan Bypasses UAC, Installs AnyDesk with “Oscompatible” Package – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 19, 2024NewsroomSoftware Security / Spyware A malicious package uploaded to the npm registry has been found deploying a sophisticated remote...
U.S. Cybersecurity Agency Warns of Actively Exploited Ivanti EPMM Vulnerability – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 19, 2024NewsroomCyber Theat / Zero-Day The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Thursday added a now-patched critical flaw...
New Docker Malware Steals CPU for Crypto & Drives Fake Website Traffic – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 18, 2024NewsroomServer Security / Cryptocurrency Vulnerable Docker services are being targeted by a novel campaign in which the threat actors...
Russian COLDRIVER Hackers Expand Beyond Phishing with Custom Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . The Russia-linked threat actor known as COLDRIVER has been observed evolving its tradecraft to go beyond credential harvesting to deliver its...
TensorFlow CI/CD Flaw Exposed Supply Chain to Poisoning Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 18, 2024NewsroomSupply Chain Attacks / AI Security Continuous integration and continuous delivery (CI/CD) misconfigurations discovered in the open-source TensorFlow machine...
MFA Spamming and Fatigue: When Security Measures Go Wrong – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 18, 2024The Hacker NewsAuthentication Security / Passwords In today’s digital landscape, traditional password-only authentication systems have proven to be vulnerable...
Bangladeshi Elections Come into DDoS Crosshairs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Muhammad Toqeer via Alamy Stock Photo The end of 2023 saw an uptick in distributed denial-of-service (DDoS)...
With Attacks on the Upswing, Cyber-Insurance Premiums Poised to Rise Too – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Photon Photo via Shutterstock An increase in cyber-insurance claims in 2023, driven by a more active threat...
Stealthy New macOS Backdoor Hides on Chinese Websites – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Age Foto Stock via Alamy Stock Photo A sneaky macOS backdoor that allows attackers to remotely control...
‘Chaes’ Infostealer Code Contains Hidden Threat Hunter Love Notes – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading 1 Min Read Source: Grenar via Alamy Stock Photo Appearing flattered by the dogged analysis of Chaes...
Lock Down the Software Supply Chain With ‘Secure by Design’ – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer Source: Parichat via Adobe Stock Photo Software that prioritizes security at its most foundational level means designing the...
Sophisticated macOS Infostealers Get Past Apple’s Built-In Detection – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Bits and Splits via Shutterstock Increasingly sophisticated infostealers are targeting macOS with the capability to evade Apple’s...
PixieFail UEFI Flaws Expose Millions of Computers to RCE, DoS, and Data Theft – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 18, 2024NewsroomFirmware Security / Vulnerability Multiple security vulnerabilities have been disclosed in the TCP/IP network protocol stack of an open-source...
Iranian Hackers Masquerade as Journalists to Spy on Israel-Hamas War Experts – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 18, 2024NewsroomCyber Espionage / Threat Intelligence High-profile individuals working on Middle Eastern affairs at universities and research organizations in Belgium,...
Mimecast Announces New CEO – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE LEXINGTON, Mass., January 16, 2024 – Mimecast Limited (Mimecast), an advanced email and collaboration security company, announced today the appointment of Marc van Zadelhoff as...
ESET Launches New Managed Detection and Response (MDR) Service for Small and Midsize Businesses – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE BRATISLAVA/SAN DIEGO — January 17, 2024 — ESET, a global leader in cybersecurity, has announced the launch of ESET MDR, an...
Intel 471 Appoints Technology Veteran, Sonja Tsiridis, Chief Technology Officer – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE WILMINGTON, Del.- Intel 471, a premier provider of cyber threat intelligence (CTI) solutions across the globe, announced Sonja Tsiridis as its...
$80M in Crypto Disappears into Drainer-as-a-Service Malware Hell – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: Peter Horree via Alamy Stock Photo A sophisticated phishing campaign dubbed “Inferno Drainer” has...
Google Chrome Zero-Day Bug Under Attack, Allows Code Injection – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Wachiwit via Shutterstock Google has patched a high-severity zero-day bug in its Chrome Web browser that attackers...
Experts Ponder Effectiveness of Official Warnings of Cyber Scams – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading Source: Mohd Izzuan Roslan via Alamy Stock Photo The Dubai Police, from the United Arab Emirates,...