Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: Seemanta Dutta via Alamy Stock Photo About 15 million names, usernames, and emails associated...
Author: admin
Nozomi Networks Delivers Multi-Spectrum Wireless Security Sensor for Global OT and IoT Environments – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE SAN FRANCISCO, January 24, 2024 — Nozomi Networks Inc., the leader in OT and IoT security, today introduced Guardian Air™, the industry’s only...
ChatGPT Cybercrime Discussions Spike to Nearly 3K Posts on Dark Web – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading 1 Min Read Source: Ascannio via Shutterstock In new findings from Kaspersky’s Digital Footprint Intelligence service,...
CISA’s Water Sector Guide Puts Incident Response Front & Center – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: M Production via Shutterstock Water and wastewater utilities last week received new guidance for improving their response...
Jason’s Deli Accounts Compromised by Credential Stuffing – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Source: William Morgan via Alamy Stock Photo Texas-based soup and sandwich slinger Jason’s Deli is alerting members...
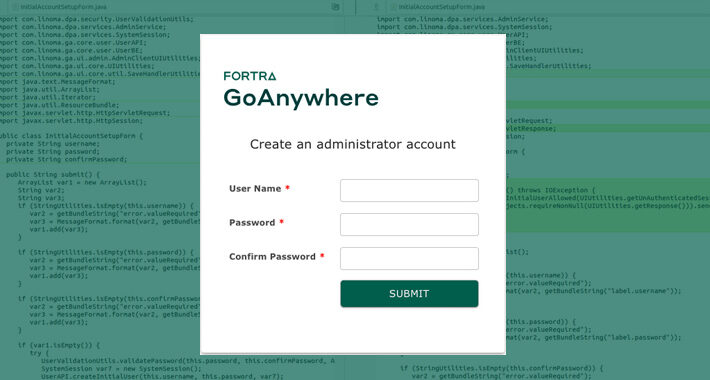
Fortra Discloses Critical Auth Bypass Vuln in GoAnywhere MFT – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Tanoy1412 via Shutterstock A proof-of-concept exploit is now available for a near maximum-severity flaw in Fortra’s GoAnywhere...
Cyber Threat Landscape: 7 Key Findings and Upcoming Trends for 2024 – Source:thehackernews.com
Source: thehackernews.com – Author: . The 2023/2024 Axur Threat Landscape Report provides a comprehensive analysis of the latest cyber threats. The information combines data from the...
China-backed Hackers Hijack Software Updates to Implant “NSPX30” Spyware – Source:thehackernews.com
Source: thehackernews.com – Author: . A previously undocumented China-aligned threat actor has been linked to a set of adversary-in-the-middle (AitM) attacks that hijack update requests from...
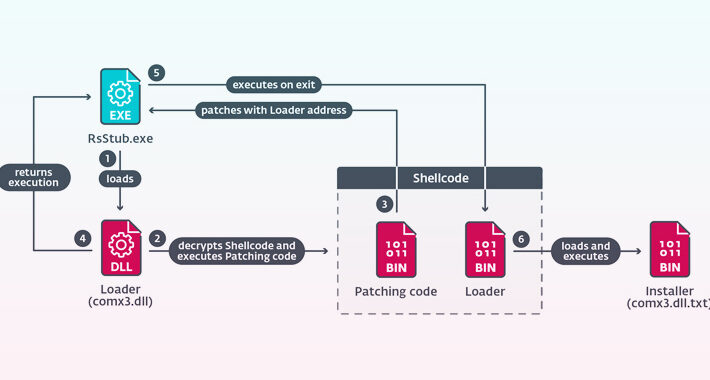
New CherryLoader Malware Mimics CherryTree to Deploy PrivEsc Exploits – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 25, 2024NewsroomThreat Intelligence / Malware Research A new Go-based malware loader called CherryLoader has been discovered by threat hunters in...
Tech Giant HP Enterprise Hacked by Russian Hackers Linked to DNC Breach – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 25, 2024NewsroomCyber Attack / Data Breach Hackers with links to the Kremlin are suspected to have infiltrated information technology company...
Top Cybersecurity Predictions for 2024 (Free Download) – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: While artificial intelligence discourse and chatbots dominated 2023, the cybersecurity space still pulled our attention now and then with cyberattacks, reminding us...
Information Security Incident Reporting Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: This policy from TechRepublic Premium provides guidelines for the reporting of information security incidents by company employees. The goal is to facilitate...
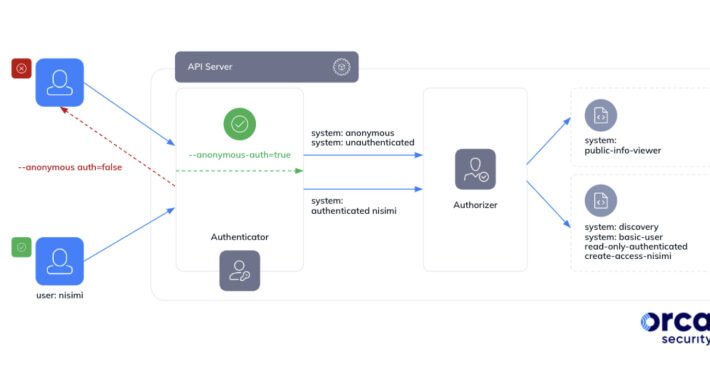
Google Kubernetes Misconfig Lets Any Gmail Account Control Your Clusters – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 24, 2024NewsroomCloud Security / Kubernetes Cybersecurity researchers have discovered a loophole impacting Google Kubernetes Engine (GKE) that could be potentially...
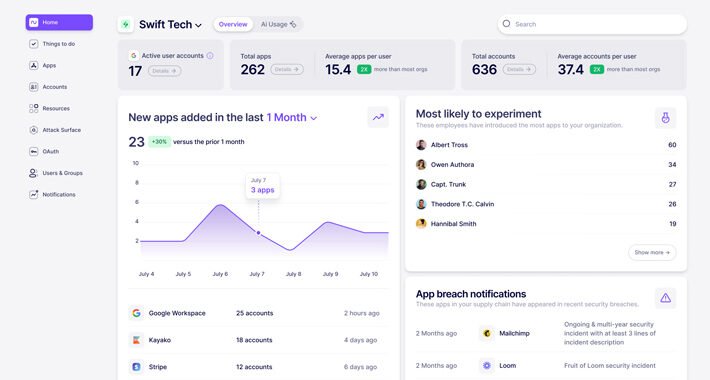
What is Nudge Security and How Does it Work? – Source:thehackernews.com
Source: thehackernews.com – Author: . In today’s highly distributed workplace, every employee has the ability to act as their own CIO, adopting new cloud and SaaS...
Kasseika Ransomware Using BYOVD Trick to Disarms Security Pre-Encryption – Source:thehackernews.com
Source: thehackernews.com – Author: . The ransomware group known as Kasseika has become the latest to leverage the Bring Your Own Vulnerable Driver (BYOVD) attack to...
Kasseika Ransomware Linked to BlackMatter in BYOVD Attack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Marcos Alvarado via Alamy Stock Photo A ransomware group potentially linked to the defunct BlackMatter gang has...
Researchers Map AI Threat Landscape, Risks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Krot Studio via Shutterstock Many of the security problems of large language models (LLMs) boil down to...
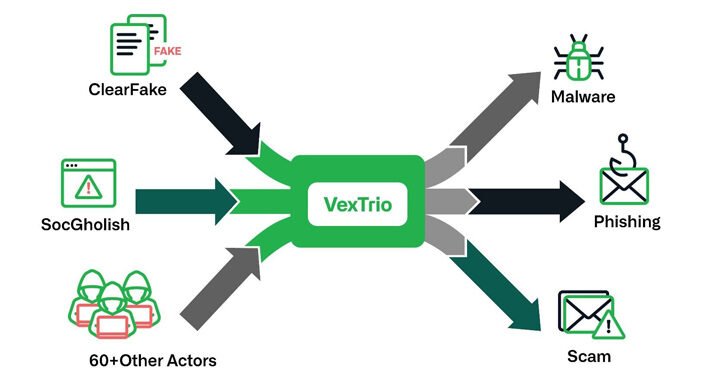
‘VexTrio’ TDS: The Biggest Cybercrime Operation on the Web? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Amanda Ahn via Alamy Stock Photo A single traffic distribution system (TDS) operator in possession of more...
U.S., U.K., Australia Sanction Russian REvil Hacker Behind Medibank Breach – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 24, 2024NewsroomCryptocurrency / Cybercrime Governments from Australia, the U.K., and the U.S. have imposed financial sanctions on a Russian national...
Patch Your GoAnywhere MFT Immediately – Critical Flaw Lets Anyone Be Admin – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 24, 2024NewsroomVulnerability / Endpoint Security A critical security flaw has been disclosed in Fortra’s GoAnywhere Managed File Transfer (MFT) software...
Days After Google, Apple Reveals Exploited Zero-Day in Browser Engine – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: mindea via Shutterstock Apple has patched an actively exploited zero-day bug in its WebKit browser engine for...
US, UK, AU Officials Sanction 33-Year-Old Russian Medibank Hacker – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Takatoshi Kurikawa via Alamy Stock Photo A Russian national has been identified and sanctioned by Australia, the...
MacOS Malware Targets Bitcoin, Exodus Cryptowallets – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer Source: Nikolay Vinokurov via Alamy Stock Photo Fresh malware targeting Apple users in the US and Germany is...
Subway Puts a LockBit Investigation on the Menu – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: graham jepson via Alamy Stock Photo The Subway restaurant chain, creator of the Sweet...
SEC Says SIM Swap to Blame for Breached X Account – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading 2 Min Read Source: dennizn via Alamy Stock Photo A new statement from the Securities and Exchange...
Millions at Risk As ‘Parrot’ Web Server Compromises Take Flight – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributing Writer Source: Sergei Simonov via Alamy Stock Photo Threat actors behind a traffic redirect system (TDS) that’s been active...
CISA Director Jen Easterly Targeted in Swatting Incident – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading 1 Min Read On Dec. 30, CISA Director Jen Easterly was the target of a swatting...
Magecart Adds Middle East Retailers to Long List of Victims – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Metamorworks via Shutterstock Retailers in the Middle East and Africa account for a greater number of victims...
VexTrio: The Uber of Cybercrime – Brokering Malware for 60+ Affiliates – Source:thehackernews.com
Source: thehackernews.com – Author: . The threat actors behind ClearFake, SocGholish, and dozens of other actors have established partnerships with another entity known as VexTrio as...
Malicious NPM Packages Exfiltrate Hundreds of Developer SSH Keys via GitHub – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 23, 2024NewsroomSoftware Security / Supply Chain Two malicious packages discovered on the npm package registry have been found to leverage...