PURPOSE This Media disposal policy from TechRepublic Premium provides specific instructions for ensuring organization data is properly protected when disposing of old storage media. From the...
Author: admin
How to Overcome 5 Common Obstacles to Implementing Zero Trust
How to Overcome 5 Common Obstacles to Implementing Zero Trust 6 min read ZTNA offers significant security advantages, but key obstacles can hinder a successful implementation....
USENIX Security ’22 – Mohannad Ismail, Andrew Quach, Christopher Jelesnianski, Yeongjin Jang, Changwoo Min – ‘Tightly Seal Your Sensitive Pointers With PACTight’
USENIX Security ’22 – Mohannad Ismail, Andrew Quach, Christopher Jelesnianski, Yeongjin Jang, Changwoo Min – ‘Tightly Seal Your Sensitive Pointers With PACTight’Our thanks to USENIX for...
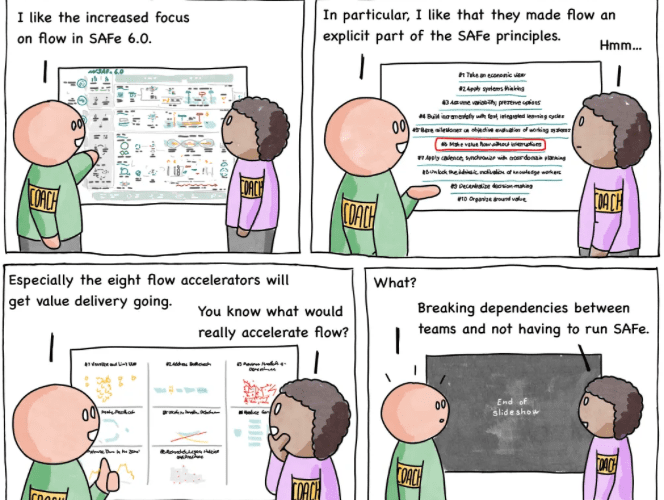
Comic Agilé – Mikkel Noe-Nygaard, Luxshan Ratnarav – #234 – SAFe Flow
Comic Agilé – Mikkel Noe-Nygaard, Luxshan Ratnarav – #234 – SAFe Flow via the respected Software Engineering expertise of Mikkel Noe-Nygaard as well as the lauded...
API Security 101 for Developers: How to Easily Secure Your APIs
API Security 101 for Developers: How to Easily Secure Your APIsAPI security is an ongoing process that demands continual attention and effort from everyone on the...
Everything to Know About ISO 27001 Internal Audits
Everything to Know About ISO 27001 Internal AuditsWhen a restaurant expects an inspection from the Health Department, management takes a number of steps to prepare. The...
North Korean threat actor APT43 pivots back to strategic cyberespionage
North Korean threat actor APT43 pivots back to strategic cyberespionageWhen it comes to threat actors working for the North Korean government, most people have heard of...
USENIX Security ’22 – Bernd Prünster, Alexander Marsalek, Thomas Zefferer – ‘Total Eclipse Of The Heart – Disrupting The InterPlanetary File System’
USENIX Security ’22 – Bernd Prünster, Alexander Marsalek, Thomas Zefferer – ‘Total Eclipse Of The Heart – Disrupting The InterPlanetary File System’Our thanks to USENIX for...
USENIX Security ’22 – Bernd Prünster, Alexander Marsalek, Thomas Zefferer – ‘Total Eclipse Of The Heart – Disrupting The InterPlanetary File System’
USENIX Security ’22 – Bernd Prünster, Alexander Marsalek, Thomas Zefferer – ‘Total Eclipse Of The Heart – Disrupting The InterPlanetary File System’Our thanks to USENIX for...
Spera Unveils Platform for Finding and Tracking Identities
Spera Unveils Platform for Finding and Tracking Identities Spera emerged from stealth today to launch a namesake platform that discovers and tracks identities to enable organizations...
Microsoft Introduces GPT-4 AI-Powered Security Copilot Tool to Empower Defenders
Microsoft Introduces GPT-4 AI-Powered Security Copilot Tool to Empower DefendersMicrosoft on Tuesday unveiled Security Copilot in preview, marking its continued push to embed AI-oriented features in an attempt to...
SHEIN fined US$1.9mn over data breach affecting 39 million customers
SHEIN fined US$1.9mn over data breach affecting 39 million customersThe fast fashion brand failed to disclose a data breach in 2018 that saw hackers access customer’s...
How carding can affect your business
How carding can affect your businessAn exploration of the carding threat vector and why ecommerce sites are vulnerable to itLeer másCategories RSS FeedAn exploration of the...
Banking Trojan apocalypse: how hackers are stealing millions
Banking Trojan apocalypse: how hackers are stealing millionsA guide to what Trojan malware is and why you should guard against this dangerous threat vectorLeer másCategories RSS...
How does CISO strategy prevent threats?
How does CISO strategy prevent threats?Explore about the challenges CISO was facing to protect the organization and how they overcome this with strategies to prevent threats.Leer...
How to foster secure and efficient data practices
How to foster secure and efficient data practicesDiscover how to apply secure file transfer practices without affecting the efficiency of your businessLeer másCategories RSS FeedDiscover how...
Cybercriminals are using ChatGPT to create malware
Cybercriminals are using ChatGPT to create malwareHow malicious parties are using AI chatbots to help power cyber crimeLeer másCategories RSS FeedHow malicious parties are using AI...
IOTW: Malicious actors gain access to GitHub source code
IOTW: Malicious actors gain access to GitHub source codeA hacker has cloned repositories associated with multiple GitHub-owned organizationsLeer másCategories RSS FeedA hacker has cloned repositories associated...
The dangerous vulnerabilities caused by weak email security
The dangerous vulnerabilities caused by weak email securityWhy email security is integral to protecting your internal business and external brand and how to improve itLeer másCategories...
What is business email compromise?
What is business email compromise?Cyber Security Hub investigates a threat vector that specifically targets employees via their emailLeer másCategories RSS FeedCyber Security Hub investigates a threat...
The ultimate guide to malware
The ultimate guide to malwareThis all-encompassing guide explores what malware is, how attacks using this dangerous threat vector are launched and how to mitigate themLeer másCategories...
Google suspends Pinduoduo app over malware concerns
Google suspends Pinduoduo app over malware concernsThe app has been suspended for failing to be compliant with Google’s policyLeer másCategories RSS FeedThe app has been suspended...
IOTW: Source code stolen in Reddit phishing attack
IOTW: Source code stolen in Reddit phishing attackCompromised employee credentials allowed the hacker to access Reddit’s internal documentsLeer másCategories RSS FeedCompromised employee credentials allowed the hacker...
We are less than a year away from a cyber attack credited to ChatGPT
We are less than a year away from a cyber attack credited to ChatGPTDirector of sales engineering APJ at BlackBerry Cybersecurity, Jonathan Jackson, explains why artificial...
IOTW: Russian hackers target NATO sites with DDoS attack
IOTW: Russian hackers target NATO sites with DDoS attackThe cyber attack has reportedly affected NATOs response to the recent earthquakes affecting Syria and TurkeyLeer másCategories RSS...
German airports hit with DDoS attack
German airports hit with DDoS attackThe suspected attack took the websites of seven airports offlineLeer másCategories RSS FeedThe suspected attack took the websites of seven airports...
How Covid-19 impacted cyber security challenges, focus and spends
How Covid-19 impacted cyber security challenges, focus and spendsPractitioner insight on how cyber security challenges, focus and spend was affected by the global pandemicLeer másCategories RSS...
Top seven hacks and cyber security threats in APAC
Top seven hacks and cyber security threats in APACCyber Security Hub explores some of the most impactful cyber attacks in the APAC regionLeer másCategories RSS FeedCyber...
Why healthcare providers are focusing on cyber resilience
Why healthcare providers are focusing on cyber resilienceCyber Security Hub interviews Jojo Nufable, group IT infrastructure and cyber security head at Metro Pacific Health Solutions, to...
IOTW: US Marshals Service suffers ransomware attack
IOTW: US Marshals Service suffers ransomware attackThe cyber attack saw confidential information held by the law enforcement office compromisedLeer másCategories RSS FeedThe cyber attack saw confidential...