Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Cyber espionage attacks against organizations in Taiwan have surged against the backdrop of recent political tensions,...
Author: admin
10 Types of AI Attacks CISOs Should Track – Source: www.darkreading.com
Source: www.darkreading.com – Author: Ericka Chickowski, Contributing Writer, Dark Reading Keep up with the latest cybersecurity threats, newly-discovered vulnerabilities, data breach information, and emerging trends. Delivered...
Microsoft Azure VMs Hijacked in Cloud Cyberattack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading A threat actor known for targeting Microsoft cloud environments now is employing the serial console feature on...
Once Again, Malware Discovered Hidden in npm – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer, Dark Reading Two code packages named “nodejs-encrypt-agent” in the popular npm JavaScript library and registry recently were discovered...
Aviatrix is transforming cloud network security with distributed firewalling – Source: www.csoonline.com
Source: www.csoonline.com – Author: The new distributed cloud firewall offering distributes both inspection and policy enforcement into the original path of application traffic, eliminating the need...
Russian national indicted for ransomware attacks against the US – Source: www.csoonline.com
Source: www.csoonline.com – Author: Mikhail Pavlovich Matveev is charged with conspiring to transmit ransom demands, conspiring to damage protected computers, and intentionally damaging protected computers. Metamorworks...
Lemon Group Uses Millions of Pre-Infected Android Phones to Enable Cybercrime Enterprise – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Millions of Android phone users around the world are contributing daily to the financial wellbeing of...
5 Ways Security Testing Can Aid Incident Response – Source: www.darkreading.com
Source: www.darkreading.com – Author: David Dunn, Senior Managing Director and Head of EMEA Cybersecurity, FTI Consulting The importance for organizations to understand who their adversaries are...
BianLian Cybercrime Group Changes Up Extortion Methods, Warns CISA – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading In an advisory this week, the US Cybersecurity and Infrastructure Security Agency (CISA) alongside the Federal Bureau...
Houthi-Backed Spyware Effort Targets Yemen Aid Workers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading An ongoing spyware campaign is targeting attendees of Saudi government-led negotiations on Yemen, along with humanitarian and...
Apple Boots a Half-Million Developers From Official App Store – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading The Apple App Store supports more than 36 million registered Apple developers, but not all...
Microsoft Teams Features Amp Up Orgs’ Cyberattack Exposure – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Researchers have identified several ways hackers can leverage Microsoft Teams functionalities to phish users, or deliver...
Talking Security Strategy: Cybersecurity Has a Seat at the Boardroom Table – Source: www.darkreading.com
Source: www.darkreading.com – Author: Christopher Hentner, Chair, Panzura Customer Security Advisory Council Cybersecurity is no longer a fringe issue for businesses. What was once a siloed...
Sunday Paper Debacle: Philadelphia Inquirer Scrambles to Respond to Cyberattack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading The city of Philadelphia’s largest newspaper couldn’t publish its Sunday edition last week due to a weekend...
Transform Any Place into a Smart Space – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Transform rooms, buildings, and spaces into assets that inform new insights, inspire collaboration, and drive efficiencies through automation and analytics. With our...
Unpatched Wemo Smart Plug Bug Opens Countless Networks to Cyberattacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading The Wemo Mini Smart Plug V2, which allows users to remotely control anything plugged into...
Attackers Target macOS With ‘Geacon’ Cobalt Strike Tool – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Heads up: threat actors are now deploying a Go-language implementation of Cobalt Strike called Geacon that...
Russian Ransomware Perp Charged After High-Profile Hive, Babuk & LockBit Hits – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Russian national Mikahail Pavlovich Matveev has been charged by the US Department of Justice (DoJ) for launching...
Qilin Ransomware Operation Outfits Affiliates With Sleek, Turnkey Cyberattacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Ransomware-as-a-service (RaaS) operation Qilin has been arming its affiliates with malware and supporting services to target education,...
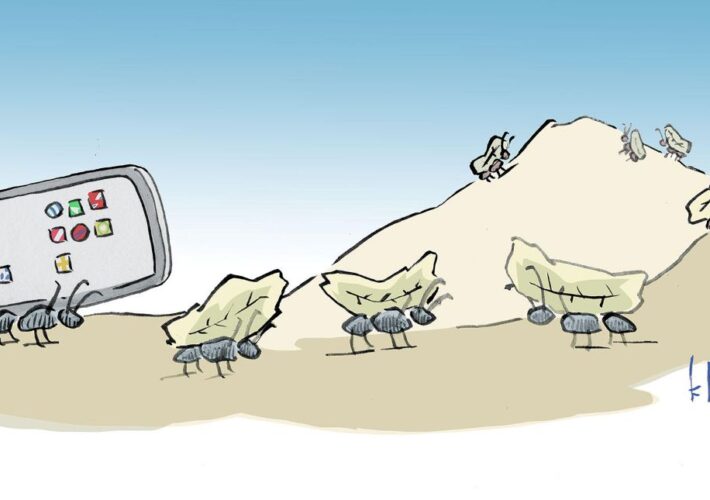
Name That Toon: One by One – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Klossner, Cartoonist Your marching orders are simple: Come up with a clever cybersecurity-related caption for the cartoon above. Now comes the...
Severe RCE Bugs Open Thousands of Industrial IoT Devices to Cyberattack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Eleven vulnerabilities in the cloud-management platforms of three industrial cellular router vendors put operational technology (OT) networks...
‘MichaelKors’ Showcases Ransomware’s Fashionable VMware ESXi Hypervisor Trend – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading The widespread use of VMware’s ESXi hypervisor and the fact that it does not support any...
PharMerica Leaks 5.8M Deceased Users’ PII, Health Information – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading PharMerica Healthcare has disclosed that its systems were breached earlier this year by an unauthorized third party, which...
RA Ransomware Group Emerges With Custom Spin on Babuk – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading A newly discovered ransomware gang dubbed RA Group is ramping up its cyberattacks — the...
Generative AI Empowers Users but Challenges Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Michael Bargury, CTO & Co-Founder, Zenity In recent years low-code/no-code has been empowering business users to address their needs on their own,...
Toyota Discloses Decade-Long Data Leak Exposing 2.15M Customers’ Data – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Toyota has disclosed that for more than 10 years, a misconfigured cloud bucket left more 2.15 million...
Microsoft Follina Bug Is Back in Meme-Themed Cyberattacks Against Travel Orgs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading A threat actor is exploiting last year’s Follina (RCE) remote code execution vulnerability to deploy the...
TSA Official: Feds Improved Cybersecurity Response Post-Colonial Pipeline – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer, Dark Reading In the wake of the ransomware attack on the Colonial Pipeline, the US Transportation Security Agency...
Tomiris called, they want their Turla malware back – Source: securelist.com
Source: securelist.com – Author: Pierre Delcher, Ivan Kwiatkowski Introduction We introduced Tomiris to the world in September 2021, following our investigation of a DNS-hijack against a...
QBot banker delivered through business correspondence – Source: securelist.com
Source: securelist.com – Author: Victoria Vlasova, Andrey Kovtun, Darya Ivanova In early April, we detected a significant increase in attacks that use banking Trojans of the...