Source: www.infosecurity-magazine.com – Author: 1 A recently discovered Chinese phishing gang has expanded its campaigns to the Middle East with new scams designed to harvest personal...
Author:
Kaspersky Says it is Being Targeted By Zero-Click Exploits – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Russian AV vendor Kaspersky has claimed that iOS devices on its network are being targeted by sophisticated zero-day exploits. The firm...
Horabot Campaign Targets Spanish-Speaking Users in the Americas – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A new cyber threat campaign named “Horabot” has been discovered by cybersecurity firm Cisco Talos targeting Spanish-speaking users in the Americas. Horabot,...
Void Rabisu’s RomCom Backdoor Reveals Shifting Threat Actor Goals – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The hacking group known as Void Rabisu has deployed a new backdoor called RomCom. According to security researchers at Trend Micro,...
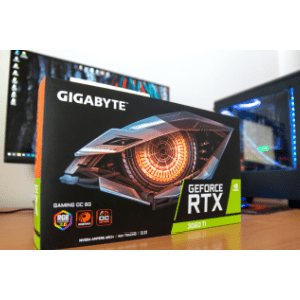
Potential Backdoor in Gigabyte PCs Exposes Supply Chain Risks – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Cybersecurity firm Eclypsium has uncovered a potential backdoor in Gigabyte systems, raising concerns about the security of the technology supply chain....
Lab Testing Firm Says Ransomware Breach Affects 2.5 Million – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Fraud Management & Cybercrime , Healthcare , Industry Specific Clinical Test Info, SSNs Exfiltrated, Company Tells SEC Marianne Kolbasuk McGee (HealthInfoSec)...
How a Layered Security Approach Can Minimize Email Threats – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 OpenText Cybersecurity’s Sam Kumarsamy on Detecting, Blocking and Filtering Out Malicious Emails Sam Kumarsamy • May 31, 2023 Attackers...
Conti’s Legacy: What’s Become of Ransomware’s Most Wanted? – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Group Lives on in the Form of More Agile Offshoots Such as Royal and Black Basta Mathew J. Schwartz (euroinfosec) •...
Are We Facing a Massive Cybersecurity Threat? – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 The way artificial intelligence has unfolded in the past few months is just the tip of the iceberg, and it’s going...
Breach Roundup: Amazon Settles US FTC Investigations – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Fraud Management & Cybercrime , Governance & Risk Management , Incident & Breach Response Also: SAS Extortion, Skolkovo Foundation Hacked, Salesforce...
Cryptohack Roundup: Hacker Yields Control of Tornado Cash – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Blockchain & Cryptocurrency , Cryptocurrency Fraud , Fraud Management & Cybercrime Also: Tron Patches a Big Bug, Binance Privacy Coin Delisting...
Hackers Exploit Progress MOVEit File Transfer Vulnerability – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Governance & Risk Management Critical Zero-Day Vulnerability Permits Escalated Privileges, Unauthorized Access Michael Novinson...
Cryptohack Roundup: Hacker Yields Control of Tornado Cash – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Blockchain & Cryptocurrency , Cryptocurrency Fraud , Fraud Management & Cybercrime Also: Tron Patches a Big Bug, Binance Privacy Coin Delisting...
Conti’s Legacy: What’s Become of Ransomware’s Most Wanted? – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Group Lives on in the Form of More Agile Offshoots Such as Royal and Black Basta Mathew J. Schwartz (euroinfosec) •...
AI Tech Execs Put AI on Par With Nukes for Extinction Risk – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development , Standards, Regulations & Compliance Sam Altman, Geoffrey Hinton Say...
Ukrainian CERT Warns of New SmokeLoader Campaign – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Attack Surface Management , Security Operations Hackers Using Compromised Email Addresses to Deliver the Malware Akshaya Asokan (asokan_akshaya) • May 31,...
Cisco Buys Armorblox to Bring Generative AI to Its Portfolio – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Email Security & Protection , Fraud Management & Cybercrime SentinelOne-Backed Armorblox Protects Email Through Natural...
SolarWinds Transforms Brand to Signify Ongoing Evolution, Portfolio Expansion, and Customer Empowerment – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 AUSTIN, TEXAS—May 30, 2023 — SolarWinds (NYSE:SWI), a leading provider of simple, powerful, secure observability and IT management software, today unveiled a...
HMRC in New Tax Credits Scam Warning – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The UK’s tax office has warned of a new set of scams designed to trick customers claiming tax credits into handing over...
Amazon to Pay $31m After FTC’s Security and Privacy Allegations – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Amazon will pay close to $31m to the Federal Trade Commission (FTC) to settle allegations relating to Alexa and its Ring...
Zyxel Customers Urged to Patch Exploited Bug – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The security community is urging Zyxel networking device users to update their firewalls and VPNs after reports that hackers are actively...
New “Migraine” Flaw Enables Attackers to Bypass MacOS Security – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A new vulnerability has been discovered in macOS that allows attackers with root access to bypass System Integrity Protection (SIP) and...
SpinOk Trojan Compromises 421 Million Android Devices – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A new Android Trojan has been discovered by security researchers that potentially compromised 421 million devices. The Doctor Web team unveiled...
IDSA: Only 49% of Firms Invest in Identity Protection Before Incidents – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Only 49% of leadership teams proactively invest in identity protection solutions before a security incident. Just 29% take action to support...
Cisco Buys Armorblox to Bring Generative AI to Its Portfolio – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Artificial Intelligence & Machine Learning , Email Security & Protection , Fraud Management & Cybercrime SentinelOne-Backed Armorblox Protects Email Through Natural...
Integrating Generative AI Into the Threat Detection Process – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Shyhawk Security has integrated generative AI into its threat detection process and significantly increased the speed and lowered the costs of...
Ukrainian CERT Warns of New SmokeLoader Campaign – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Attack Surface Management , Security Operations Hackers Using Compromised Mail to Deliver the Malware Akshaya Asokan (asokan_akshaya) • May 31, 2023...
Cyberattack Diverts Patients From Rural Idaho Hospital – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Healthcare , Incident & Breach Response , Industry Specific Ambulances Being Diverted to Other Facilities; Clinic Care Limited Marianne Kolbasuk McGee...
Ring Settles FTC Allegations of Poor Cybersecurity, Privacy – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Endpoint Security , Governance & Risk Management , Privacy Amazon-Owned Ring Will Pay $5.8 Million to Settle FTC Investigation David Perera...
What Apple’s RSRs Reveal About Mac Patch Management – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 Apple’s recent release of macOS Ventura 13.4 contained a laundry list of security fixes, including two WebKit vulnerabilities that could lead...