Source: www.govinfosecurity.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Social Engineering Toitoin Trojan Campaign Uses Six-Staged Infection Chain to Steal Data Prajeet Nair...
Author:
Web-Browsing Glitch Prompts Apple to Withdraw Zero-Day Fix – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Governance & Risk Management , Patch Management , Vulnerability Assessment & Penetration Testing (VA/PT) The Latest Rapid Security Response Might Prevent...
Clop: Behind MOVEit Lies a Loud, Adaptable and Persistent Threat Group – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The MOVEit cyber-attack continues to grow, with more organizations falling victim every day. Brett Callow, a threat analyst at Emsisoft, counted...
11 Million Patients Impacted in Healthcare Data Breach – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 HCA Healthcare has revealed it has suffered a major data breach affecting approximately 11 million patients. The private healthcare operator said...
EU Adopts New US Data Privacy Agreement – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The European Commission has adopted its adequacy decision for the EU-US Data Privacy Agreement, allowing organizations to engage in the free...
Moroccan Charged With OpenSea NFT and Crypto Theft – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A Moroccan man has been charged with four counts relating to a scheme to steal nearly half-a-million dollars’ worth of cryptocurrency...
Man Charged With Remote Attack on Water Plant – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A man has been charged with intentionally attempting to sabotage the IT infrastructure running a Californian town’s water treatment facility. Rambler...
E-commerce Fraud Surges By Over 50% Annually – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Most global e-commerce merchants are planning to hire new fraud specialists this year after being swamped with scams over the past...
Ukrainian Agencies, NATO Targeted With RATs Ahead of Summit – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Government Attackers Using RomCom, PicassoLoader and njRAT Malware to Steal Credentials...
Honeywell to Buy SCADAfence to Strengthen OT Security Muscle – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Endpoint Security , Governance & Risk Management , Internet of Things Security Security Vendor Will Provide Asset Discovery, Threat Detection to...
European Commission Adopts EU-US Data Privacy Framework – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Privacy , Standards, Regulations & Compliance New Data Regime Will Facilitate Commercial Data Flow Between the...
HCA Says Up to 11M Patients Affected by Email Data Hack – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Breach Notification , Governance & Risk Management , Privacy Hospital Chain Notifies SEC, Says Incident Not Likely to Affect Financials Marianne...
Honeywell to Acquire SCADAfence, Strengthening its Cybersecurity Software Portfolio – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 Charlotte, NC (July 10, 2023) – Honeywell (Nasdaq: HON) today announced it has agreed to acquire SCADAfence, a leading provider of...
Guardz Identifies New ‘ShadowVault’ macOS Stealer Malware – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 TEL AVIV, Israel, July 10, 2023 /PRNewswire/ — Guardz, the cybersecurity company securing and insuring SMEs, disclosed today the existence of a new information...
Why Hybrid Work Has Made Secure Access So Complicated – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 Gone are the days of working only in physical offices on corporate devices. Employees now have the freedom to work wherever...
Ukrainian Agencies, NATO Targeted With RATs Ahead of Summit – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Government Attackers Using RomCom, PicassoLoader and njRAT Malware to Steal Credentials...
Honeywell to Buy SCADAfence to Strengthen OT Security Muscle – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Endpoint Security , Governance & Risk Management , Internet of Things Security Security Vendor Will Provide Asset Discovery, Threat Detection to...
European Commission Adopts EU-US Data Privacy Framework – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Governance & Risk Management , Privacy , Standards, Regulations & Compliance New Data Regime Will Facilitate Commercial Data Flow Between the...
HCA Says Up to 11M Patients Affected by Email Data Hack – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Breach Notification , Governance & Risk Management , Privacy Hospital Chain Notifies SEC, Says Incident Not Likely to Affect Financials Marianne...
RomCom Group Targets Ukraine Supporters Ahead of NATO Summit – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The RomCom threat actor has reportedly launched a targeted cyber campaign aimed at organizations and individuals supporting Ukraine just days before...
Crimeware Group Asylum Ambuscade Ventures Into Cyber-Espionage – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Asylum Ambuscade, a crimeware group, has been observed changing tactics and moving to cyber espionage. The group, initially exposed by researchers...
Android OS Tools Fuel Cybercrime Spree, Prey on Digital Users – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Cyber-criminals have increasingly utilized specialized mobile Android OS device spoofing tools to bypass anti-fraud controls and impersonate compromised account holders. According...
Central Bankers Develop Framework For Securing Digital Currencies – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 An international financial institution owned by the world’s central banks has published a new framework designed to help members mitigate cyber...
Martin Lewis Shocked at Deepfake Investment Scam Ad – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A leading UK TV personality has hit out at a lack of regulation for fraudulent internet advertising, after a deepfake likeness...
Cyber Extortion Cases Surge 39% Annually – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Incidents of online extortion reported to the police increased by nearly two-fifths in 2022 compared to a year previously, according to...
How to Use Log Management to Retrace Your Digital Footsteps – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 Logs are like digital footprints or a letter that developers write to themselves for the future. They track every action or...
Updated Truebot Malware Targeting Orgs in US, Canada – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Malware as-a-Service New Variant of Trojan Called Silence.Downloader Seen in May Prajeet Nair (@prajeetspeaks)...
Updated Truebot Malware Targeting Orgs in US, Canada – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Malware as-a-Service New Variant of Trojan Called Silence.Downloader Seen in May Prajeet Nair (@prajeetspeaks)...
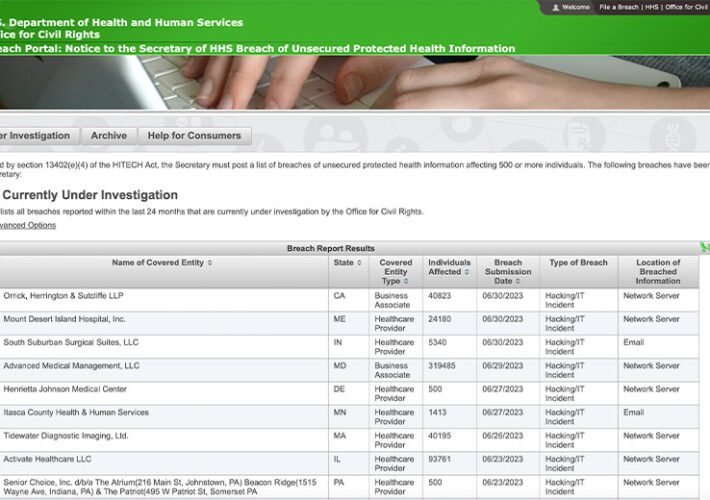
Midyear Health Data Breach Analysis: The Top Culprits – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Breach Notification , Fraud Management & Cybercrime , Governance & Risk Management Latest Hacking, Vendor Incident Trends Emerging From the Federal...
Latest MOVEit Bug Is Another Critical SQL Injection Flaw – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 3rd Party Risk Management , Fraud Management & Cybercrime , Governance & Risk Management Progress Software Reveals 1 New ‘Critical’ and...