Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Healthcare Also: ISMG’s Healthcare Summit and Emerging Trends, Challenges, New Tech...
Author:
Webinar | Graduating into a New Era: Cloud Security’s Biggest Challenges – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
Florida Hospital Says Data Theft Attack Affects 1.2 Million – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Breach Notification , Fraud Management & Cybercrime , Ransomware Tampa General Hospital Says Incident Involved Thwarted Ransomware Encryption Attempt Marianne Kolbasuk...
7 Tech Firms Pledge to White House to Make AI Safe, Secure – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Government , Industry Specific Microsoft, Google, Meta, Amazon Among Companies Making ‘Voluntary Commitments’ Marianne Kolbasuk...
US DoJ Announces Plan to Shakeup Cybercrime Investigations – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The US Department of Justice (DoJ) is doubling the size of the team investigating cryptocurrency crime, with the fight against ransomware...
Plurilock Launches Generative AI ‘Guardrails’ Product for Workforces – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Generative AI tools have conquered the workplace, especially large language model-based (LLM) chatbots like OpenAI’s ChatGPT and Google’s Bard. These powerful...
Russian Prosecutor Asks for 18 Years in Jail for Group-IB Founder – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The Russian state prosecution asked the Moscow City Court to impose 18 years in a strict colony regime on Ilya Sachkov,...
Chinese Hackers Breached Ambassador’s Email – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A Chinese cyber-espionage campaign revealed by Microsoft last week compromised the government email account of the US ambassador to China and...
Clop Drives Record Ransomware Activity in June – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Ransomware attacks in June soared 221% year-on-year to hit a record 434 for the month, according to an analysis from NCC...
GitHub Warns Devs of North Korean Attacks – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 GitHub has warned of a new North Korean threat campaign designed to compromise victims via malicious npm package dependencies. The development...
TrustArc Announces TRUSTe EU-US Data Privacy Framework Verification – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 SAN FRANCISCO, July 20, 2023 /PRNewswire/ — On July 10, 2023, the European Commission announced the official adoption of its adequacy decision for the EU-U.S. Data Privacy Framework...
Deloitte Global Expands MXDR Cybersecurity SaaS Solution With Operational Technology and Identity Modules – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 NEW YORK, July 20, 2023 /PRNewswire/ — Deloitte, a leader in global security services and incident response services, has expanded their Managed Extended Detection...
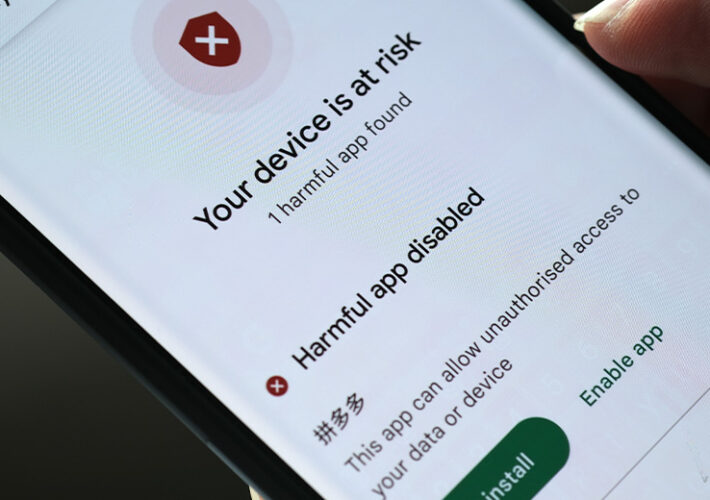
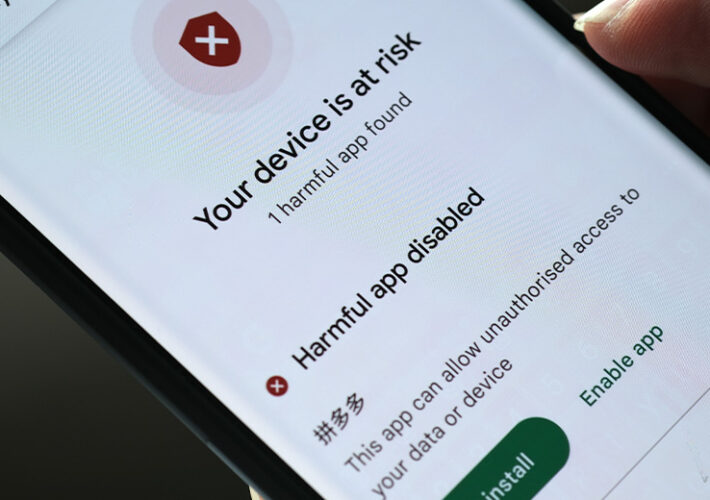
Chinese Threat Group APT41 Linked To Android Malware Attacks – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Mobile Payments Fraud APT41 Used WyrmSpy and DragonEgg Surveillance Malware to...
KillNet DDoS Attacks Further Moscow’s Psychological Agenda – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Government More Evidence Suggests Self-Promoting ‘Hacktivist’ Group Is Tool of Russian...
When Cybercriminals Go Phishing, Emails Get the Most Bites – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Developing a Multilayered Defense Strategy for the Most Common Attack Techniques Troy Gill • July 20, 2023 For cybercriminals...
JumpCloud Blames North Korean Hackers on Breach – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cryptocurrency Fraud , Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Threat Actor Is Financially Motivated Focusing on Cryptocurrency, Says...
Black SEO Offerings Gaining Momentum in Underground Forums – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Social Engineering Malvertising Campaigns Trick Users Searching for AI-Related Tools Such as ChatGPT Prajeet...
Adobe Fixes ColdFusion Zero-Day – Again – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Application Security , Governance & Risk Management , Next-Generation Technologies & Secure Development Rework of Previous Update Available for ColdFusion Versions 2023,...
Chinese Threat Group APT41 Linked To Android Malware Attacks – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Mobile Payments Fraud APT41 Used WyrmSpy and DragonEgg Surveillance Malware to...
KillNet DDoS Attacks Further Moscow’s Psychological Agenda – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Government More Evidence Suggests Self-Promoting ‘Hacktivist’ Group Is Tool of Russian...
When Cybercriminals Go Phishing, Emails Get the Most Bites – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Developing a Multilayered Defense Strategy for the Most Common Attack Techniques Troy Gill • July 20, 2023 For cybercriminals...
JumpCloud Blames North Korean Hackers on Breach – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cryptocurrency Fraud , Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Threat Actor Is Financially Motivated Focusing on Cryptocurrency, Says...
Black SEO Offerings Gaining Momentum in Underground Forums – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Social Engineering Malvertising Campaigns Trick Users Searching for AI-Related Tools Such as ChatGPT Prajeet...
Adobe Fixes ColdFusion Zero-Day – Again – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Application Security , Governance & Risk Management , Next-Generation Technologies & Secure Development Rework of Previous Update Available for ColdFusion Versions 2023,...
New Study Highlights Critical Infrastructure’s Resilience – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Security behavior change firm Hoxhunt has published its latest research highlighting employees’ resilience in critical infrastructure, showing a higher engagement level in...
Zyxel Vulnerability Exploited by DDoS Botnets on Linux Systems – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Distributed Denial of Service (DDoS) botnets have been used to actively exploit a critical vulnerability found in Zyxel firewall models. The...
Microsoft Strengthens Cloud Logging Against Nation-State Threats – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Microsoft has announced intentions to enhance cloud logging and improve security visibility for its customers in response to the growing frequency...
Old Roblox Data Leak Resurfaces, 4000 Users’ Personal Information Exposed – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A data breach affecting the online game platform Roblox has exposed sensitive information from thousands of users. Troy Hunt, founder of...
Half of AI Open Source Projects Reference Buggy Packages – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Open source is playing a growing role across the AI technology stack, but most (52%) projects reference known vulnerable dependencies in...
CNI Firms: Climate Tech is Increasing Cyber Risk – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Over eight in 10 (83%) of the UK’s critical national infrastructure (CNI) firms believe new technologies designed to enhance sustainability will...