Source: www.govinfosecurity.com – Author: 1 API Security Flaws That Give Back-End Access to an Object Can Cause Large Breaches, Agencies Say Mihir Bagwe (MihirBagwe) • July...
Author:
FBI: Hackers Use AI for Sextortion, Explosives, Bad Websites – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development China Seeks to Level AI Playing Field by Stealing IP...
UK MoD Error Sends Emails to Russia’s Ally Instead of US – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The UK’s Ministry of Defence (MoD) is launching an investigation after a typing error reportedly led to classified emails being sent...
New Study Reveals Forged Certificate Attack Risks – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 New research has highlighted the severe risks posed by forged certificate attacks, which can lead to unauthorized access to important company...
40% of Ubuntu Cloud Workloads Vulnerable to Exploits – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Two high-priority vulnerabilities have been discovered in the OverlayFS module of Ubuntu Linux, impacting approximately 40% of Ubuntu cloud workloads. According...
Microsoft Accused of Negligence in Recent Email Compromise – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A US Senator has demanded that the Whitehouse holds Microsoft to account for a Chinese cyber campaign that compromised US government...
Australia and US Issue Warning About Web App Threats – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The Australian and US governments have issued a joint advisory about the growing cyber-threats to web applications and application programming interfaces...
SSNDOB Marketplace Admin Pleads Guilty – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A Ukrainian man has pleaded guilty to charges connected with his role as an administrator of notorious cybercrime marketplace SSNDOB. Vitalii...
North Korean Hackers Bag Another $100m in Crypto Heists – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 North Korea’s infamous Lazarus hacking group has been linked to two new attacks on cryptocurrency firms which led to the theft...
MOVEit Campaign Claims Millions More Victims – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Another 8–11 million individuals are believed to have had their personal information compromised by the Clop ransomware gang after a US...
7 in 10 MSPs Name Data Security and Network Security As Their Top IT Priorities for 2023 – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 FRISCO, Texas, July 27, 2023 /PRNewswire/ — Netwrix, a cybersecurity vendor, today announced additional findings for the MSP sector from its survey of more than...
CompTIA ChannelCon Technology Vendor Fair Highlights Tech Solutions – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 DOWNERS GROVE, Ill., July 27, 2023 /PRNewswire/ — More than 160 product vendors and distributors will be on hand for the Technology Vendor...
Gathering dust and data: How robotic vacuums can spy on you. – Source:
Source: – Author: 1 Mitigate the risk of data leaks with a careful review of the product and the proper settings. Original Post URL: Category &...
Dear all, What are some common subject lines in phishing emails? – Source:
Source: – Author: 1 Scammers exploit current ongoing events, account notifications, corporate communication, and a sense of urgency. Original Post URL: Category & Tags: – Views:...
What happens if AI is wrong? – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Responses generated by ChatGPT about individual people could be misleading or harmful or spill their personal information. What are the takeaways for...
8 common work-from-home scams to avoid – Source:
Source: – Author: 1 That ‘employer’ you’re speaking to may in reality be after your personal information, your money or your help with their illegal activities...
Child identity theft: how do I keep my kids’ personal data safe? – Source:
Source: – Author: 1 Why is kids’ personal information in high demand, how do criminals steal it, and what can parents do to help prevent child...
Protect yourself from ticketing scams ahead of the Premier League Summer Series USA Tour – Source:
Source: – Author: 1 There is a significant secondary marketplace where tickets can sell for several times their original value, opening the opportunity for scammers and...
Key findings from ESET Threat Report H1 2023 – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Here’s how cybercriminals have adjusted their tactics in response to Microsoft’s stricter security policies, plus other interesting findings from ESET’s new Threat...
The danger within: 5 steps you can take to combat insider threats – Source:
Source: – Author: 1 Some threats may be closer than you think. Are security risks that originate from your own trusted employees on your radar? Original...
ESET Research Podcast: Finding the mythical BlackLotus bootkit – Source:
Source: – Author: 1 Here’s a story of how an analysis of a supposed game cheat turned into the discovery of a powerful UEFI threat Original...
ESET Threat Report H1 2023 – Source:
Source: – Author: 1 A view of the H1 2023 threat landscape as seen by ESET telemetry and from the perspective of ESET threat detection and...
Emotet: sold or on vacation? – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Originally a banking trojan, Emotet later evolved into a full-blown botnet and went on to become one of the most dangerous cyberthreats...
What’s up with Emotet? – Source:
Source: – Author: 1 A brief summary of what happened with Emotet since its comeback in November 2021 Original Post URL: Category & Tags: – Views:...
Deepfaking it: What to know about deepfake-driven sextortion schemes – Source:
Source: – Author: 1 Criminals increasingly create deepfake nudes from people’s benign public photos in order to extort money from them, the FBI warns Original Post...
Verizon 2023 DBIR: What’s new this year and top takeaways for SMBs – Source:
Source: – Author: 1 Here are some of the key insights on the evolving data breach landscape as revealed by Verizon’s analysis of more than 16,000...
The good, the bad and the ugly of AI – Week in security with Tony Anscombe – Source:
Source: – Author: 1 The growing use of synthetic media and the difficulties in distinguishing between real and fake content raise a slew of legal and...
Moscow Court Convicts Former Group-IB Chief for Treason – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Governance & Risk Management , IT Risk Management Ilya Sachkov Sentenced to 14 Years in Prison Mihir Bagwe (MihirBagwe) • July...
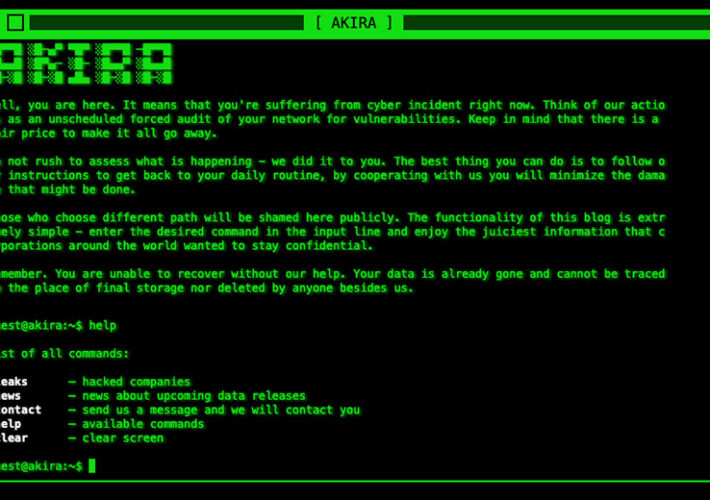
Are Akira Ransomware’s Crypto-Locking Malware Days Numbered? – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Fraud Management & Cybercrime , Ransomware Ransomware-Building Group Lost Royal-Organized Competition, Researchers Say Mathew J. Schwartz (euroinfosec) • July 27, 2023...
Coro Buys Privatise to Infuse SASE With Network Connectivity – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Governance & Risk Management , SASE , Security Operations Privatise Will Add DNS Filtering, Content Filtering, ZTNA to Coro’s SASE Platform...