Source: – Author: 1 Bills granting access to end-to-end encrypted systems, opportunity for cybercriminals, abuse by authority, human rights, and tech companies leaving the UK? Original...
Author:
Gathering dust and data: How robotic vacuums can spy on you – Source:
Source: – Author: 1 Mitigate the risk of data leaks with a careful review of the product and the proper settings. Original Post URL: Category &...
Dear all, What are some common subject lines in phishing emails? – Source:
Source: – Author: 1 Scammers exploit current ongoing events, account notifications, corporate communication, and a sense of urgency. Original Post URL: Category & Tags: – Views:...
What happens if AI is wrong? – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Responses generated by ChatGPT about individual people could be misleading or harmful or spill their personal information. What are the takeaways for...
8 common work-from-home scams to avoid – Source:
Source: – Author: 1 That ‘employer’ you’re speaking to may in reality be after your personal information, your money or your help with their illegal activities...
Child identity theft: how do I keep my kids’ personal data safe? – Source:
Source: – Author: 1 Why is kids’ personal information in high demand, how do criminals steal it, and what can parents do to help prevent child...
Protect yourself from ticketing scams ahead of the Premier League Summer Series USA Tour – Source:
Source: – Author: 1 There is a significant secondary marketplace where tickets can sell for several times their original value, opening the opportunity for scammers and...
Key findings from ESET Threat Report H1 2023 – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Here’s how cybercriminals have adjusted their tactics in response to Microsoft’s stricter security policies, plus other interesting findings from ESET’s new Threat...
The danger within: 5 steps you can take to combat insider threats – Source:
Source: – Author: 1 Some threats may be closer than you think. Are security risks that originate from your own trusted employees on your radar? Original...
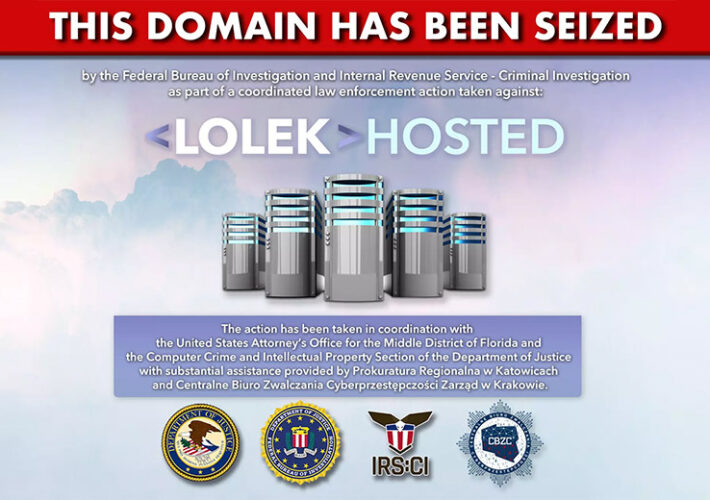
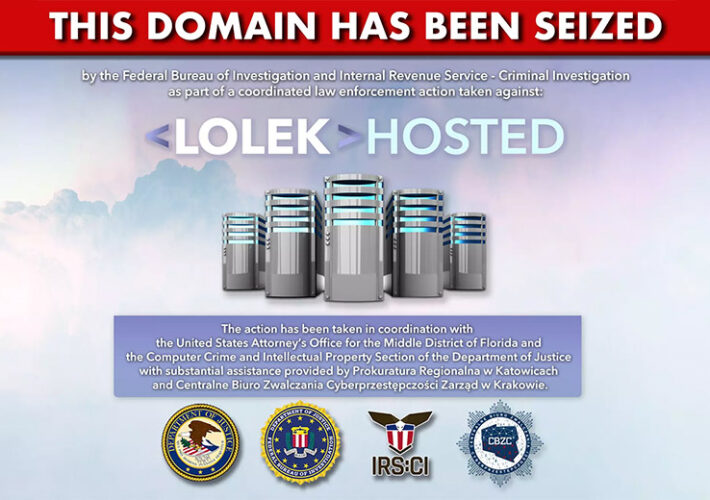
‘Bulletproof’ LolekHosted Down Following Police Operation – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Ransomware NetWalker Ransomware Hackers Used the Polish Web-Hosting Service Akshaya Asokan (asokan_akshaya) • August...
Cyber Review: Teens Caused Chaos With Low-Complexity Attacks – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cybercrime , Fraud Management & Cybercrime Voice and Text Not Secure Enough for Authentication, Cyber Safety Review Board Says Mathew J....
Using AI to Prevent Cyberattacks and Fill the Skills Gap – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 As generative AI has evolved with alarming speed, it has brought “huge amounts of innovation,” said Aaron Cockerill, the chief strategy...
Protect AI Purchases Huntr to Extend Bug Bounties to AI, ML – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Artificial Intelligence & Machine Learning , Governance & Risk Management , Next-Generation Technologies & Secure Development Deal Allows Protect AI Customers...
Honor Among Cybercriminals? Why a Canadian Firm Paid Ransom – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Fraud Management & Cybercrime , Healthcare , Industry Specific Alberta Dental Paid ‘Substantial’ Ransom for Decryptor Key, Deletion of Stolen Data...
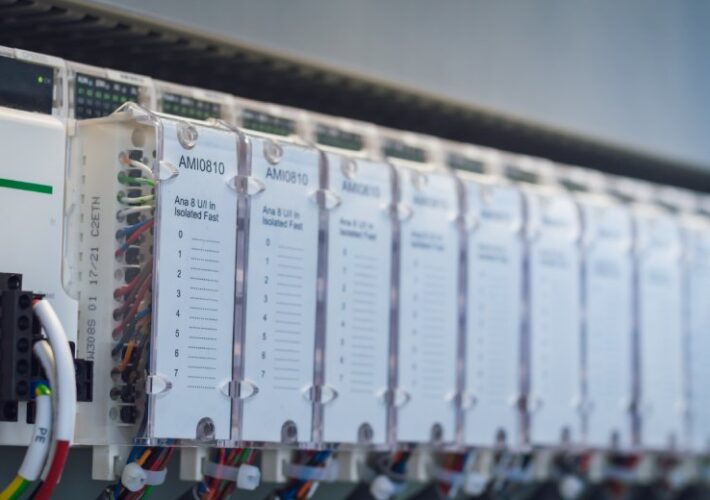
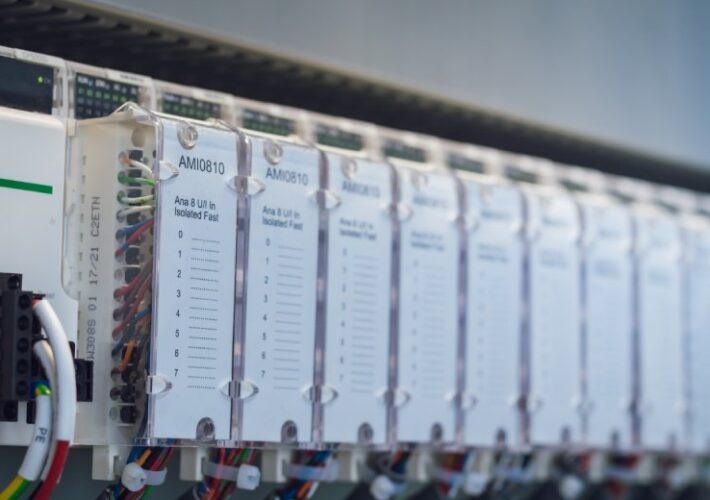
Researchers Unveil Widespread Flaw In Industrial Systems – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Governance & Risk Management , Operational Technology (OT) Exploitation Could Lead to RCE and DoS Attacks in Millions of Devices Mihir...
‘Bulletproof’ LolekHosted Down Following Police Operation – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Ransomware NetWalker Ransomware Hackers Used the Polish Web-Hosting Service Akshaya Asokan (asokan_akshaya) • August...
Cyber Review: Teens Caused Chaos With Low-Complexity Attacks – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime Voice and Text Not Secure Enough for Authentication, Cyber Safety Review Board Says Mathew J....
Using AI to Prevent Cyberattacks and Fill the Skills Gap – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 As generative AI has evolved with alarming speed, it has brought “huge amounts of innovation,” said Aaron Cockerill, the chief strategy...
Protect AI Purchases Huntr to Extend Bug Bounties to AI, ML – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Governance & Risk Management , Next-Generation Technologies & Secure Development Deal Allows Protect AI Customers...
Honor Among Cybercriminals? Why a Canadian Firm Paid Ransom – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Healthcare , Industry Specific Alberta Dental Paid ‘Substantial’ Ransom for Decryptor Key, Deletion of Stolen Data...
Researchers Unveil Widespread Flaw In Industrial Systems – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Operational Technology (OT) Exploitation Could Lead to RCE and DoS Attacks in Millions of Devices Mihir...
DARPA Taps RTX to Attune AI Decisions to Human Values – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 CAMBRIDGE, Mass., Aug. 10, 2023 /PRNewswire/ — RTX’s (NYSE: RTX) BBN division received a contract award to support DARPA’s “In The Moment” program. ITM aims to...
Fortinet Announces Free Security Awareness Curriculum for K-12 Students Tied to White House’s Cyber Initiatives – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 SUNNYVALE, Calif. – Aug 9, 2023 — John Maddison, Chief Marketing Officer and EVP, Product Strategy at Fortinet “Expanding the cybersecurity knowledge...
Rootly Raises $12M to Help Enterprise IT Teams Resolve Incidents 80 Percent Faster – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 San Francisco, Calif. – Aug. 10, 2023 – Rootly, which offers the first and only enterprise-grade incident management platform, announced today that...
Osano Secures $25M Series B to Advance Data Privacy Platform – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 AUSTIN, Texas, Aug. 10, 2023 /PRNewswire/ — Osano today announces a $25 million Series B funding round led by Baird Capital, with participation from Jump Capital, LiveOak Venture Partners, Next...
Multiple Flaws Found in the Avada WordPress Theme and Plugin – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Multiple vulnerabilities have been identified in the widely used Avada theme and its accompanying Avada Builder plugin. These security flaws, uncovered...
Lapsus$ Hacker Group Exposed in Latest CSRB Report – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The US Cyber Safety Review Board (CSRB) has issued a comprehensive report shedding light on the operations of the notorious extortion-focused...
DHS to Review Microsoft’s Security in Chinese Email Hack – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The US Department of Homeland Security (DHS) has announced it will investigate Microsoft’s security practices in relation to the recent Chinese...
Time is money, and online game scammers have lots of it – Source:
Source: – Author: 1 Gamers and cybersecurity professionals have something in common – the ever-terrible presence of hacking, scams, and data theft – but how and...
Check cybersecurity pre-invest – Week in security with Tony Anscombe – Source:
Source: – Author: 1 When you invest in a company, do you check its cybersecurity? The U.S. Securities and Exchange Commission has adopted new cybersecurity rules....