Source: www.databreachtoday.com – Author: 1 Organizations of all types have important work ahead to comply with Washington state’s new My Health My Data Act, which pertains...
Author:
Why Democracy Is a Critical Asset Against Cyberthreats – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Government , Industry Specific , Information Sharing Yigal Unna, Former DG, National Cyber Directorate, Israel, on People and Partnerships Rahul Neel...
What the Uber-Joe Sullivan Case Means for CISO Liability – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Leadership & Executive Communication , Training & Security Leadership , Video Attorney Lisa Sotto Advises Security Leaders to Seek Adequate Liability...
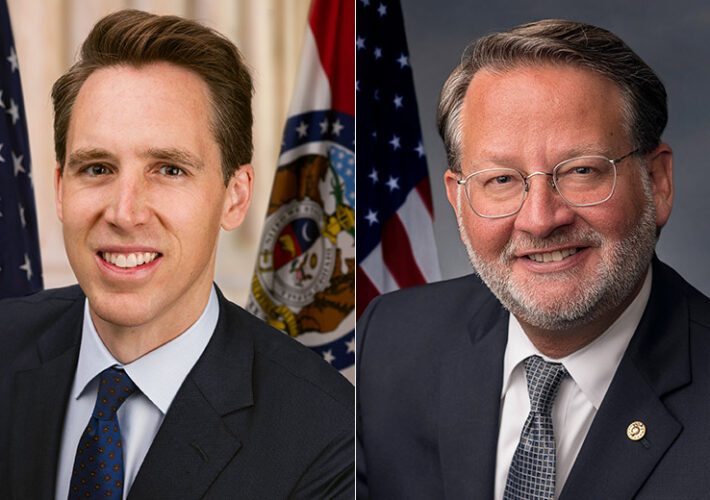
Bipartisan Bill Aims to Shut Rural Hospital Cyber Skill Gaps – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Healthcare , Industry Specific , Legislation & Litigation Calls for CISA to Develop Cyber Workforce Development Strategy Marianne Kolbasuk McGee (HealthInfoSec)...
Why Democracy Is a Critical Asset Against Cyberthreats – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Government , Industry Specific , Information Sharing Yigal Unna, Former DG, National Cyber Directorate, Israel, on People and Partnerships Rahul Neel...
Live Webinar Today | Using Machine Learning and Hyperscaled Cloud to Deliver Zero Trust – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Jason Georgi Global Field CTO, Prisma SASE, Palo Alto Networks Jason is the Global Field Chief Technology Officer for Prisma SASE...
Efficient Management of Enterprisewide Data Protection – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cloud Access Security Brokers (CASB) , Governance & Risk Management , Next-Generation Technologies & Secure Development Skyhigh Security’s Nate Brady on...
What’s Inside Washington State’s New My Health My Data Act – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Organizations of all types have important work ahead to comply with Washington state’s new My Health My Data Act, which pertains...
Bipartisan Bill Aims to Shut Rural Hospital Cyber Skill Gaps – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Healthcare , Industry Specific , Legislation & Litigation Calls for CISA to Develop Cyber Workforce Development Strategy Marianne Kolbasuk McGee (HealthInfoSec)...
PharMerica Reports Breach Affecting Nearly 6 Million People – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Fraud Management & Cybercrime , Ransomware Money Message Ransomware Group Threatens to Release 1.6 Million Records Mihir Bagwe (MihirBagwe) • May...
What the Uber-Joe Sullivan Case Means for CISO Liability – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Leadership & Executive Communication , Training & Security Leadership , Video Attorney Lisa Sotto Advises Security Leaders to Seek Adequate Liability...
Researchers Uncover New “RA Group” Ransomware – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Threat researchers have discovered another new ransomware actor, this time leveraging Babuk source code in attacks on US and South Korean...
PharMerica Breach Hits Over 5.8 Million Customers – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Nearly six million customers of a popular nationwide pharmacy services provider have had their personal, health insurance and medical data exposed in...
Qilin’s Dark Web Ransomware Targets Critical Sectors – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 New information has emerged regarding the Qilin ransomware group’s operations and Ransomware-as-a-Service (RaaS) program. In their latest research study, Group-IB’s threat...
Lacework Appoints Lea Kissner As Chief Information Security Officer – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 MOUNTAIN VIEW, Calif., May 15, 2023 /PRNewswire/ — Lacework, the data-driven cloud security company, today announced the appointment of Lea Kissner as its new Chief Information...
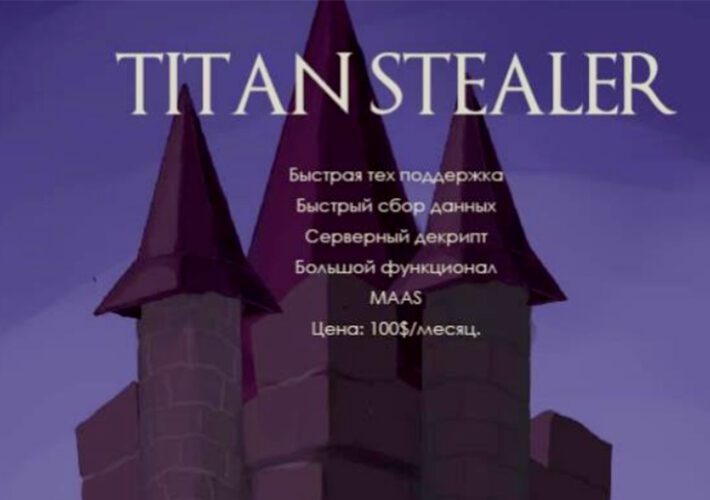
Info-Stealing Malware Populates ‘Cloud of Logs’ Offerings – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime Private Subscription Services Emerge, Together With Fresh Strains of Info Stealers Mathew J. Schwartz (euroinfosec)...
Live Webinar Tomorrow | Using Machine Learning and Hyperscaled Cloud to Deliver Zero Trust – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Jason Georgi Global Field CTO, Prisma SASE, Palo Alto Networks Jason is the Global Field Chief Technology Officer for Prisma SASE...
Discord Breached After Service Agent Targeted – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Discord has notified users of a data breach that occurred when a threat actor gained unauthorized access to the support ticket...
US Says VoIP Firm Delivered Billions of Scam Robocalls – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A Californian VoIP provider has been accused of breaking telemarketing rules by providing services that sent billions of illegal robocalls to...
UK Pension Scheme: Members Should Assume Capita Data Theft – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 One of the UK’s largest pension scheme providers has warned nearly half a million members that they should assume their data...
Uintah Basin Healthcare Data Breach Affects Over 100,000 – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Breach Notification , Healthcare , Industry Specific Hacking Incident Affects Patients Who Received Care Over a 10 Year Period Prajeet Nair...
Enigmatic Hacking Group Operating in Ukraine – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Attackers Target both Ukraine and pro-Russian Actors Anviksha More (AnvikshaMore) • May...
Uintah Basin Healthcare Data Breach Affects Over 100,000 – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Breach Notification , Healthcare , Industry Specific Hacking Incident Affects Patients Who Received Care Over a 10 Year Period Prajeet Nair...
Enigmatic Hacking Group Operating in Ukraine – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Attackers Target both Ukraine and pro-Russian Actors Anviksha More (AnvikshaMore) • May...
Webinar | Using Machine Learning and Hyperscaled Cloud to Deliver Zero Trust – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Jason Georgi Global Field CTO, Prisma SASE, Palo Alto Networks Jason is the Global Field Chief Technology Officer for Prisma SASE...
Killer Use Cases for AI Dominate RSA Conference Discussions – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Artificial Intelligence & Machine Learning , Attack Surface Management , Cybercrime Use Cases: Cybersecurity Offense, Defense and Safeguarding AI Itself, Experts...
Elementary Data Breach Questions Remain, My Dear Capita – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Fraud Management & Cybercrime , Incident & Breach Response , Ransomware Beyond $25M in Estimated Cleanup Costs, The Game Remains Afoot...
Why Datadog and Rubrik Are In Talks to Buy Laminar for $200M – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cloud Security , Governance & Risk Management , Security Operations Laminar Has Landed Multiple M&A Suitors Just 18 Months After Emerging...
HIPAA Considerations for AI Tool Use in Healthcare Research – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 The potential use cases for generative AI technology in healthcare appear limitless, but they’re weighted with an array of potential privacy,...
Why Health Entities Need to Implement NIST Cyber Framework – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 NIST Standards , Standards, Regulations & Compliance Bob Bastani of HHS ASPR Describes Perks of a Strategic Approach to Managing Risk...