Source: www.databreachtoday.com – Author: 1 Endpoint Security , Government , Hardware / Chip-level Security High-Assurance Security Tech Boosts Everfox’s Government and Infrastructure Tools Michael Novinson (MichaelNovinson)...
Month: June 2024
Fraudsters Impersonate CISA in Money Scams – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Social Engineering CISA Won’t Ask You to Wire Money or Keep Discussions Secret Chris Riotta (@chrisriotta)...
Live Webinar | Special Delivery! Defending and Investigating Advanced Intrusions on Secure Email Gateways – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Nader Zaveri Senior Manager – Incident Response & Remediation, Google Cloud Nader Zaveri has over 15 years in the cybersecurity industry,...
Justifying Your Hybrid Cloud Network Security Investment – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 David Holmes Research Analyst for Zero Trust, Security, and Risk, Forrester David Holmes is a principal analyst at Forrester, advising security...
Ransomware: Disruption of Hospitals and Nearby Facilities – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Healthcare , Industry Specific Researchers Rahi Abouk and David Powell on Study Findings, Need for Better...
The Shift to Skills-Based Hiring – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Leadership & Executive Communication , Recruitment & Reskilling Strategy , Training & Security Leadership How and Why to Select Candidates Based...
On the Future of Cybersecurity in Hybrid Cloud Environments – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Cloud Security , Next-Generation Technologies & Secure Development An Interview with Gigamon’s Chief Security Officer,...
UK Sides With APP Fraud Victims – Despite Industry Pressure – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Fraud Risk Management , Geo Focus: The United Kingdom Payments Regulator Says Banks Should Prioritize Customer...
Metaverse Identity:
Defining the Self in a Blended Reality The document delves into the significance of identity within the metaverse, emphasizing its pivotal role in shaping human experiences...
Manual nmap
The Nmap Reference Guide provides comprehensive information on Nmap, a security scanner developed by Insecure.Com LLC. It covers topics such as port scanning, TCP window probing,...
MEMORY FORENSICS VOLATILITY
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Managing Artificial Intelligence-Specific Cybersecurity Risks in the Financial Services Sector
The U.S. Department of the Treasury’s report focuses on the use of Artificial Intelligence (AI) in the financial services sector, particularly in cybersecurity and fraud protection....
7 Steps to your SOC Analyst Career
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Ransomware Gang TellYouThePass Exploits PHP Vulnerability – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Governance & Risk Management , Patch Management Flaw Allows Unauthenticated Attackers to Execute Arbitrary Code Prajeet...
Chinese-Made Biometric Access System Has 24 Vulnerabilities – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Identity & Access Management , Security Operations Kaspersky Unveils 24 Flaws in ZKTeco Terminals Prajeet Nair (@prajeetspeaks) • June 11, 2024...
Cleveland Cyber Incident Prompts Shutdown of City IT Systems – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Incident & Breach Response Cleveland Investigating Cyber Incident that Forced City to Shutdown IT...
Dutch Agency Renews Warning of Chinese Fortigate Campaign – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Network Firewalls, Network Access Control Chinese Cyber Espionage Campiagn Is ‘Much...
Managing Insider Threats
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
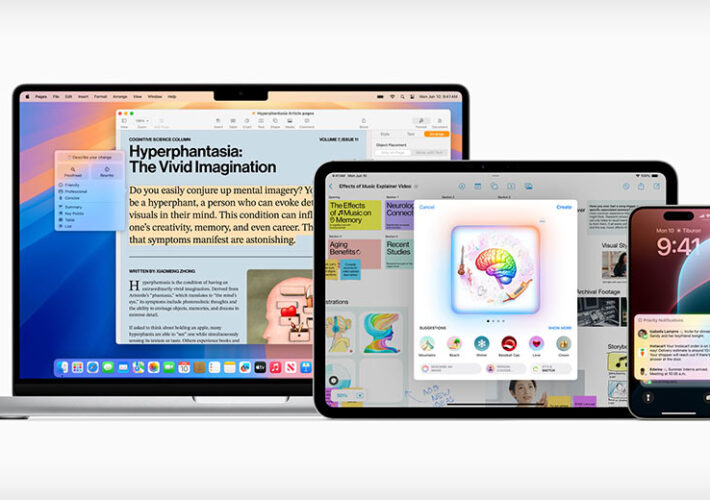
ChatGPT Integration Fortifies Apple’s Siri and Writing Tools – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development AI Integration Boosts Siri’s User Writing Tools As Apple Plays...
FCC Advances BGP Security Rules for Broadband Providers – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Standards, Regulations & Compliance Regulatory Body Approves Notice of Proposed Rulemaking Targeting BGP Hijacking Chris Riotta (@chrisriotta) • June 10, 2024...
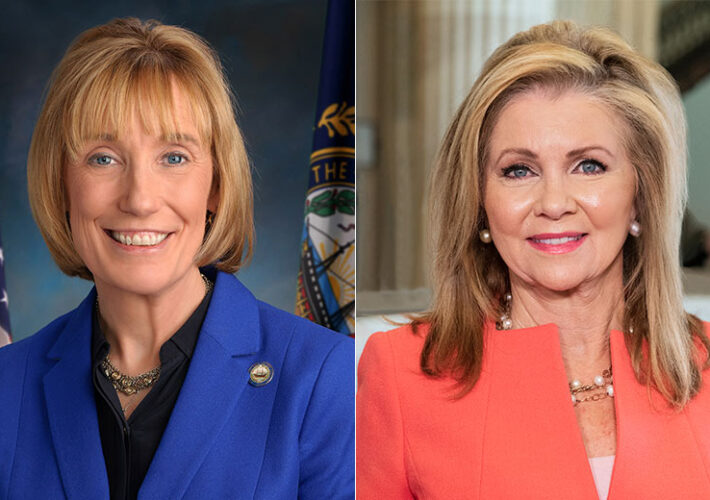
Lawmakers: UHG Violating HIPAA Breach Notification Rule – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Breach Notification , Fraud Management & Cybercrime , Healthcare Bipartisan U.S. Senators Demand Change Healthcare Breach Notification by June 21 Marianne...
Psychological Strategies for Bridging the IT-OT Divide – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Governance & Risk Management Ilionx’s Trish McGill on Tackling Geopolitical Risks...
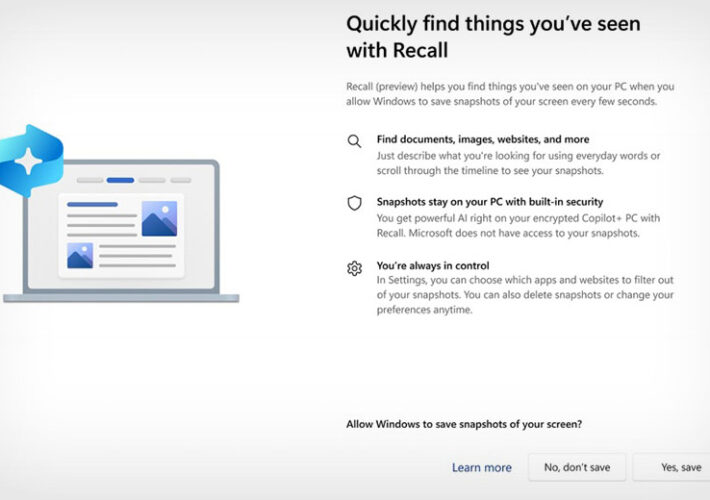
Microsoft Now Promises Extra Security for AI-Driven Recall – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development Concerns Remain Over Screenshot-Capture Feature and Microsoft’s Security Practices Mathew...
The Silent Spectre Haunting Your Network: QPhishing, the CISO’s Unspoken Nightmare.
The Silent Spectre Haunting Your Network: QPhishing, the CISO’s Unspoken Nightmare As cyber threats continue to evolve, a new and insidious danger has emerged from the...
Hackers Claim They Breached Telecom Firm in Singapore – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Breach Notification , Cybercrime , Fraud Management & Cybercrime Threat Actor GhostR Says It Stole 34 GB of Data Prajeet Nair...
CISO: The Jedi Master of Cybersecurity. Take Off Strong in Your First 100 Days! Detailed Strategic and Tactical Plan.
My personal recommendations on the relevant topics to be addressed, taking a comprehensive approach during the first 100 days of a CISO in office in a...
Critical PHP Vulnerability Threatens Windows Servers – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Patch Management , Vulnerability Assessment & Penetration Testing (VA/PT) Remote Code Execution Exploit Found; Patch Now...
ISMG Editors: Infosecurity Europe Conference 2024 Wrap-Up – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Application Security , Events , Infosecurity Europe Conference Panelists Discuss Latest Updates on AI Tech, Cyber Resilience and Regulations Anna Delaney...
Hypr Secures $30M to Expand Identity Protection Platform – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Identity & Access Management , Multi-factor & Risk-based Authentication , Security Operations Silver Lake Waterman Investment in Hypr Fuels Product Development,...
CISA Planning JCDC Overhaul as Experts Criticize Slow Start – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Government , Industry Specific , Standards, Regulations & Compliance Top US Cyber Defense Agency Aims to Revamp Its Key Public-Private Collaborative...