Source: www.bleepingcomputer.com – Author: Sergiu Gatlan The Tor Project officially introduced WebTunnel, a new bridge type specifically designed to help bypass censorship targeting the Tor network...
Month: March 2024
Google paid $10 million in bug bounty rewards last year – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Google awarded $10 million to 632 researchers from 68 countries in 2023 for finding and responsibly reporting security flaws in...
Over 12 million auth secrets and keys leaked on GitHub in 2023 – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas GitHub users accidentally exposed 12.8 million authentication and sensitive secrets in over 3 million public repositories during 2023, with the...
Jailbreaking LLMs with ASCII Art – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments Peter A. • March 12, 2024 9:07 AM The whole concept of questions that shall never be asked...
Practical Cloud Security
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CISO Libro Blanco
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Study Reveals Top Vulnerabilities in Corporate Web Applications – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A recent study conducted by Kaspersky Security Assessment experts has revealed the most prevalent vulnerabilities in corporate web applications developed in-house....
US Intelligence Predicts Upcoming Cyber Threats for 2024 – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Accelerating competition between nation-states, regional conflicts with far-reaching impact, and non-state threat actors with unprecedented capabilities are three of the main...
New Cloud Attack Targets Crypto CDN Meson Ahead of Launch – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A malicious campaign has been observed exploiting the blockchain-based Meson service for illicit gains ahead of the crypto token unlock planned...
Three-Quarters of Cyber Incident Victims Are Small Businesses – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Over three-quarters of cyber incidents impacted small businesses in 2023, with ransomware having the biggest impact on these firms, according to...
Lawmakers Slam UK Government’s “Ostrich Strategy” for Cybersecurity – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The UK will remain “exposed and unprepared” for a potentially catastrophic ransomware attack if it continues to adopt a head-in-the-sand approach...
Victims Lose $47m to Crypto Phishing Scams in February – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Impersonated accounts on X (formerly Twitter) have been blamed for the majority of cryptocurrency phishing attacks last month, with victims losing...
CISO handbook 2023
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CheatSheets of Common Attacks
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CGMA Cybersecurity Tool
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
THREAT LANDSCAPE REPORT 2023
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A Historical Journey Through Cybersecurity
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A Detailed Guide for Pentester on Wfuzz
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
A Detailed Gidue on Command & Control (C2)
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
2024 Tech Predictions
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
10 Steps to Cyber Security New Explained Cyphere
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
2FA Security Issues
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Blue Team Notes
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
BEST PRACTICES FOR CYBER CRISIS MANAGEMENT
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Automated Threat Modeling with Threat Canvas
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
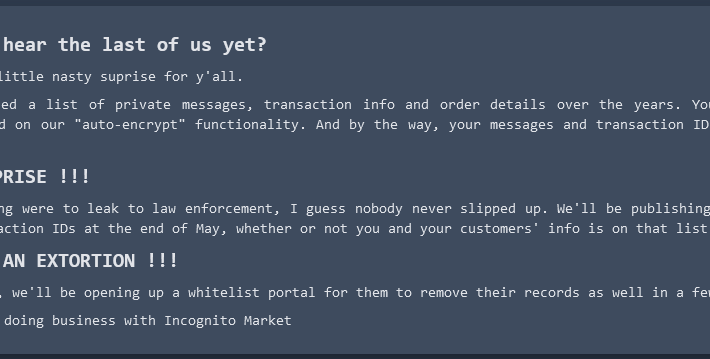
Incognito Darknet Market Mass-Extorts Buyers, Sellers – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs Borrowing from the playbook of ransomware purveyors, the darknet narcotics bazaar Incognito Market has begun extorting all of its vendors and...
ANDROID PENTEST
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Android Penetration Testing MOBSF FRAMEWORK
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Active Directory PenTesting Tools
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Vulnerability Assessment & Penetration Testing (VAPT)
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...