Source: www.techrepublic.com – Author: Matthew Sainsbury Just the highlights Australia’s cyber security vision extends to 2030, with two federal elections occurring in that time frame. A...
Month: January 2024
Cybersecurity M&A Roundup: 25 Deals Announced in December 2023 – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Twenty-five cybersecurity-related merger and acquisition (M&A) deals were announced in December 2023. The post Cybersecurity M&A Roundup: 25 Deals Announced...
Palestinian Hackers Hit 100 Israeli Organizations in Destructive Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire A group of claimed Palestinian state cyber warriors has hit over 100 Israeli organizations with wipers and data theft. The...
21 New Mac Malware Families Emerged in 2023 – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs A total of 21 new malware families targeting macOS systems were discovered in 2023, a 50% increase compared to 2022. ...
Xerox Confirms Data Breach at US Subsidiary Following Ransomware Attack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Xerox says personal information was stolen in a cyberattack at US subsidiary Xerox Business Solutions. The post Xerox Confirms Data...
Massive Fallon Ambulance Data Breach Impacts Nearly One Million People – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Livia Gyongyoși Transformative Healthcare announces Fallon Ambulance data breach exposed sensitive information of 911,757 customers. Fallon ceased operations in December 2022 but...
Democracy 2024: Stakes vs. Horses – Source: securityboulevard.com
Source: securityboulevard.com – Author: hrbrmstr The 2024 U.S. Presidential election isn’t just another tick on the political timeline. It’s a crucial juncture for — quite literally...
Top 3 SEC Cyber Rule Misconceptions – Source: securityboulevard.com
Source: securityboulevard.com – Author: Joe Breen Cloud Security, Governance and Skills in 2024 Step 1 of 6 16% Who in your organization is responsible for cloud...
The state of container security: 5 key steps to locking down your releases – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jai Vijayan Container technologies are rapidly transforming application development and deployment practices at many organizations. But they also present a minefield of...
USENIX Security ’23 – Bingyu Shen, Tianyi Shan, Yuanyuan Zhou – ‘Improving Logging to Reduce Permission Over-Granting Mistakes’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman No one specifically Someone on our general security team A dedicated person/team that handles cloud security Cloud architects and developers...
Comprehensive Guide to Fraud Detection, Management, & Analysis – Source: securityboulevard.com
Source: securityboulevard.com – Author: Webzoly SEO Fraud is everywhere, and it’s affecting you whether you realize it or not. From fraudulent credit card charges to identity...
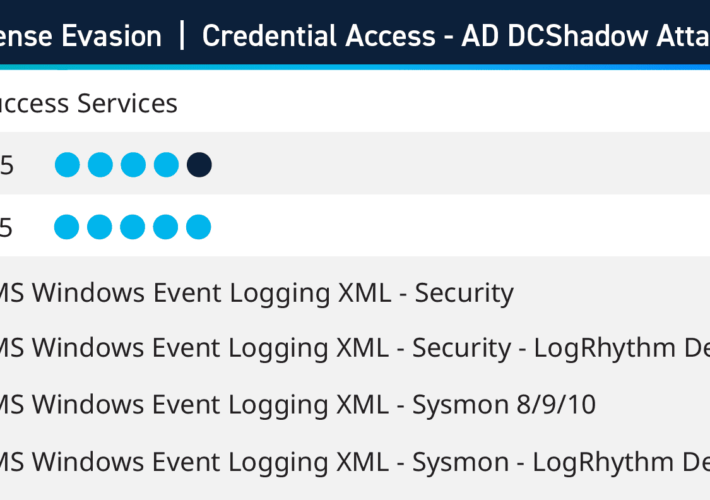
Q4 2023 Security Use Cases: Insights From Success Services – Source: securityboulevard.com
Source: securityboulevard.com – Author: Kelsey Gast As part of Success Services, this past quarter LogRhythm consultants have been hard at work helping customers improve their defenses...
The Complete Guide to Smishing (SMS Phishing) – Source: securityboulevard.com
Source: securityboulevard.com – Author: Webzoly SEO It’s unfortunately become an all-to-common scenario: you’re waiting for a package to be delivered—but then you receive an SMS text...
Abnormal Security Shares Examples of Attacks Using Generative AI – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard Abnormal Security has published examples of cyberattacks that illustrate how cybercriminals are beginning to leverage generative artificial intelligence (AI) to...
Addressing the Rising Threat of API Leaks – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jaweed Metz In the realm of cybersecurity, the metaphor of “Leaky Buckets” has become an increasingly prevalent concern, particularly in the context...
Randall Munroe’s XKCD ‘Iceland’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman No one specifically Someone on our general security team A dedicated person/team that handles cloud security Cloud architects and developers...
Industry 4.0 and OT security
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
INFORMATION SECURITY MANAGEMENT PRINCIPLES
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
DNS Security Checklist
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
DNS LAYER SECURITY FROM THE MITRE ATT&CK PERSPECTIVE
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Population Health Management Firm’s Breach Affects Millions – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 3rd Party Risk Management , Cybercrime , Fraud Management & Cybercrime HealthEC Hack Also Compromised More Than a Dozen US Healthcare...
Live Webinar | Supercharge your CMDB and Realize Value Sooner with Tanium’s ServiceNow ITAM Integration (in Spanish) – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Heriberto Cabrera Director of Technical Solutions Engineering, LATAM at Tanium Heriberto Cabrera works within Tanium as Director of Technical Solutions Engineering...
Large Language Models: Moving Past the Early Stage – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial intelligence, machine learning and large language models are not new, but they are coming to fruition with the mass adoption...
How NOT to Lead: Critical Errors in Cybersecurity Leadership – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Leadership & Executive Communication , Training & Security Leadership , Video Zero Trust Expert Chase Cunningham on His Latest Book About...
Live Webinar | Dancing with Shadows: Vendor Risk Management in the Age of AI and Cyber Intrigue – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Nate Smolenski Head of Cyber Intelligence Strategy, Netskope Nate Smolenski is an experienced CISO, Advisor, and technology leader with over two...
Ransomware Actors Steal Australian Courts’ Video Recordings – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Geo Focus: Australia , Geo-Specific Hackers Lock Up Recordings of Court Hearings to Extort Victoria’s Court...
Hack on Defunct Ambulance Firm Affects 912,000 People – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Healthcare Archived Data Stolen 2 Months After Sale of Business Affects Patients, Employees Marianne...
DevSecOpsChecklist Part 1
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
How do you define the severity of an incident?
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
DevSecOps Best Practices Guide
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...