The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Month: January 2024
ISO 22301:2019 BUSINESS CONTINUITY STANDARD IMPLEMENTATION GUIDE
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Introduction to Cybersecurity for Commercial Satellite Operations
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
ILO – Protection of workers personal data
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Illicit Financial Flows Cyber Enabled Fraud
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Identity Maturity in the Cloud – Humans do not have or need access to production cloud accounts
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Identidad Digital Corporativa INCIBE
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
HPH Sector Mitigation Guide TLP CLEAR 508c
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
How to Design a Secure Serverless Architecture
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
How I Build Engaging Tabletop Exercises in 6 Steps
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Homeland Threat Assessment 2024
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Handbook on Threat Assessments
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
H1 2023 Brief Overview of Main Incidents in Industrial CS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Guiding Cyber Security From The Boardroom
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Guia de implementa o do SOC
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
AchievingGRC ExcellenceThe Roadmap to a Career in Governance,Risk, and Compliance
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The GDPR Playbook – Discover, Plan, and Act on the Upcoming EU Data Protection Regulation
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
GDPR Compliance Checklist
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Fuerza Laboral Ciberseguridad en una era de escacez de talento y habilidades
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The best cyber security event of the year – Register now! – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: You’re invited! The premiere cyber security event of the year awaits. Registration for CPX 2024 is open. This event...
Express Guide to Ransomware in Kubernetes
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Express Guide Kubernetes Backup Recovery
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Planning Considerations Cyber Incidents 2023 – Guidance for Emergency Managers
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Facilitating Global Interoperability of Cyber Regulations in the Electricity Sector – S Y S T E M S O F C Y B E R R E S I L I E N C E : E L E C T R I C I T Y I N I T I AT I V E P O S I T I O N P A P E R N O V E M B E R 2 0 2 3
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Experts spotted a new macOS Backdoor named SpectralBlur linked to North Korea – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Experts spotted a new macOS Backdoor named SpectralBlur linked to North Korea Researchers discovered a macOS backdoor, called SpectralBlur, which shows...
Merck settles with insurers regarding a $1.4 billion claim over NotPetya damages – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Merck settles with insurers regarding a $1.4 billion claim over NotPetya damages Merck has resolved a dispute with insurers regarding...
Law firm Orrick data breach impacted 638,000 individuals – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Law firm Orrick data breach impacted 638,000 individuals Law firm Orrick, Herrington & Sutcliffe disclosed a data breach that took...
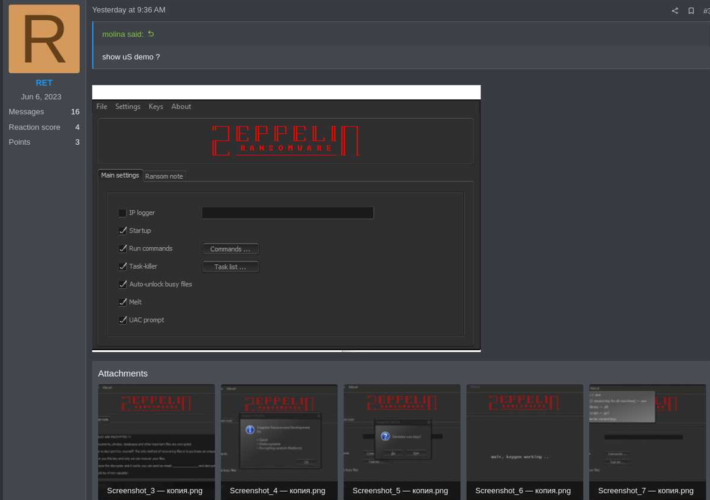
The source code of Zeppelin Ransomware sold on a hacking forum – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The source code of Zeppelin Ransomware sold on a hacking forum A threat actor announced the sale of the source...
Russia-linked APT Sandworm was inside Ukraine telecoms giant Kyivstar for months – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Russia-linked APT Sandworm was inside Ukraine telecoms giant Kyivstar for months Ukrainian authorities revealed that Russia-linked APT Sandworm had been inside...
Ivanti fixed a critical EPM flaw that can result in remote code execution – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Ivanti fixed a critical EPM flaw that can result in remote code execution Ivanti fixed a critical vulnerability in its...