Source: www.schneier.com – Author: Bruce Schneier New law journal article: Smart Device Manufacturer Liability and Redress for Third-Party Cyberattack Victims Abstract: Smart devices are used to...
Month: January 2024
Cybersecurity & Data Privacy Risk Management Model (CP-RMM) Overview
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
MITRE PLAYBOOK – Understanding Today’s Threat Landscape Using MITRE ATACK Frameworks
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cyber Security Obligations for Corporate leaders
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cyber Security Governance Principles
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CYBER SECURITY AUDIT BASELINE REQUIREMENTS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cyber SecurityCareer in 2024
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Decoding Cyber Attacks
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
TRAINING PROGRAM CAPTURE THE FLAG
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Critical Infrastructure Resources
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Criptografía sin secretoscon Python
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CRACKING SIN SECRETOS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Consumer IoT Device Cybersecurity Standard
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
662 CompTIA A+ Core 1Practice Questions & Answers Overview
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cloud-Based FINTECH Cyber Threats
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Security Guidance for Critical Areas of Focus in Cloud Computing
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Juniper Networks fixed a critical RCE bug in its firewalls and switches – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Juniper Networks fixed a critical RCE bug in its firewalls and switches Juniper Networks fixed a critical pre-auth remote code...
Vast Voter Data Leaks Cast Shadow Over Indonesia ’s 2024 Presidential Election – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Vast Voter Data Leaks Cast Shadow Over Indonesia ’s 2024 Presidential Election Investigators from Resecurity’s HUNTER (HUMINT) warn that Indonesia...
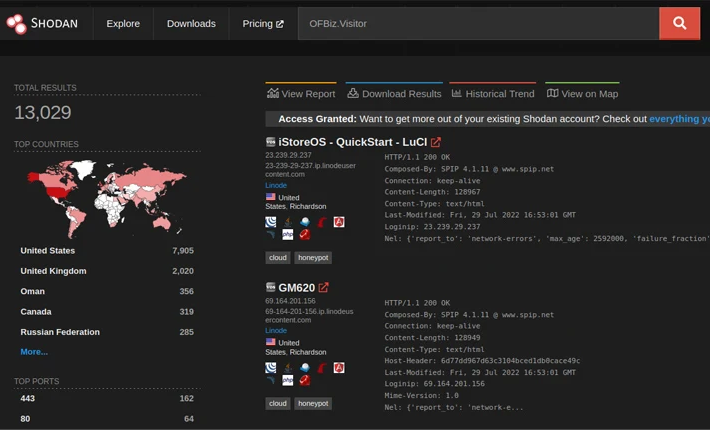
Researchers created a PoC for Apache OFBiz flaw CVE-2023-51467 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Researchers created a PoC for Apache OFBiz flaw CVE-2023-51467 Researchers published a proof-of-concept (PoC) code for the recently disclosed critical flaw CVE-2023-51467 in...
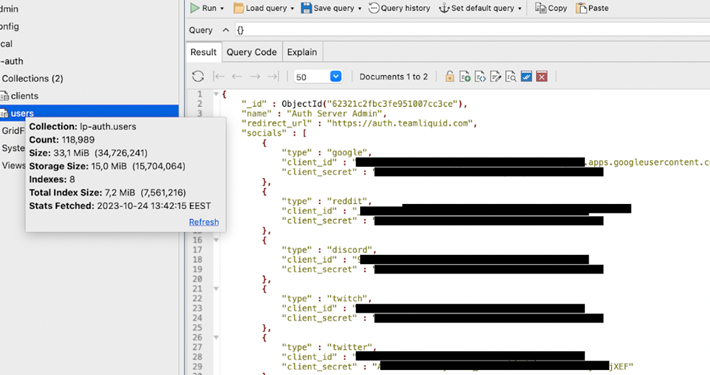
Team Liquid’s wiki leak exposes 118K users – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Team Liquid’s wiki leak exposes 118K users Liquipedia, an online e-sports platform run by Team Liquid, exposed a database revealing...
The CISO’sGuide to YourFirst 100 Days
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Webinar: Solving the Bi-Directional Sync Problem with Microsoft Sentinel and D3 Smart SOAR – Source: securityboulevard.com
Source: securityboulevard.com – Author: Shriram Sharma We’re looking forward to having you join us for our upcoming webinar on January 24th, at 10AM PST/1PM EST. It’s...
USENIX Security ’23 – Guanhong Tao, Shengwei An, Siyuan Cheng, Guangyu Shen, Xiangyu Zhang – Hard-Label Black-Box Universal Adversarial Patch Attack – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Network Security Security Bloggers Network Home » Cybersecurity » Network Security » USENIX Security ’23 – Guanhong Tao, Shengwei An, Siyuan...
Randall Munroe’s XKCD ‘Like This One’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
Sift’s innovative journey: 40 patents and counting in the fight against evolving online fraud through AI, machine learning, and Workflows – Source: securityboulevard.com
Source: securityboulevard.com – Author: Neeraj Gupta The landscape of online fraud has undergone a profound transformation since the early days of the internet. Initially, simple rule-based...
5 Free Online Brand Protection Software Tools: Pros and Cons – Source: securityboulevard.com
Source: securityboulevard.com – Author: Mitch W Online brand impersonation attacks threaten businesses large and small, but do brands really need to open their wallets to protect...
Joining My 5th Bot Mitigation Company – Why Kasada – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lucy McCue In October 2023, we welcomed Arif Husain to the team as our first Technical Director of Security Solutions. Arif has...
Before starting your 2024 security awareness program, ask these 10 questions – Source: securityboulevard.com
Source: securityboulevard.com – Author: Seed and Soil Knowing this will allow you to have these customized groups and targeted training ready in advance, so teams don’t...
USENIX Security ’23 – Shibo Zhang, Yushi Cheng, Wenjun Zhu, Xiaoyu Ji, Wenyuan Xu – CAPatch: Physical Adversarial Patch against Image Captioning Systems – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Network Security Security Bloggers Network Home » Cybersecurity » Network Security » USENIX Security ’23 – Shibo Zhang, Yushi Cheng, Wenjun...
FCC Asks Carmakers, Carriers How They’re Protecting Abuse Survivors – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jeffrey Burt The Federal Communications Commission is pressing automakers and wireless service providers to say how they are protecting victims of domestic...