Source: www.securityweek.com – Author: Eduard Kovacs Citrix is aware of attacks exploiting two new NetScaler ADC and Gateway zero-day vulnerabilities tracked as CVE-2023-6548 and CVE-2023-6549. The...
Month: January 2024
Google Warns of Chrome Browser Zero-Day Being Exploited – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine The exploited zero-day, tagged as CVE-2024-0519, is described as an out-of-bounds memory access issue in the V8 JavaScript engine. The...
Inside the Massive Naz.API Credential Stuffing List – Source: www.troyhunt.com
Source: www.troyhunt.com – Author: Troy Hunt It feels like not a week goes by without someone sending me yet another credential stuffing list. It’s usually something...
GitHub rotates keys to mitigate impact of credential-exposing flaw – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan GitHub rotated keys potentially exposed by a vulnerability patched in December that could let attackers access credentials within production containers via environment...
MacOS info-stealers quickly evolve to evade XProtect detection – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Multiple information stealers for the macOS platform have demonstrated the capability to evade detection even when security companies follow and...
Citrix warns of new Netscaler zero-days exploited in attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Citrix urged customers on Tuesday to immediately patch Netscaler ADC and Gateway appliances exposed online against two actively exploited zero-day...
Google fixes first actively exploited Chrome zero-day of 2024 – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Google has released security updates to fix the first Chrome zero-day vulnerability exploited in the wild since the start of...
Majorca city Calvià extorted for $11M in ransomware attack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The Calvià City Council in Majorca announced it was targeted by a ransomware attack on Saturday, which impacted municipal services....
FBI: Androxgh0st malware botnet steals AWS, Microsoft credentials – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan CISA and the FBI warned today that threat actors using Androxgh0st malware are building a botnet focused on cloud credential...
PixieFail flaws impact PXE network boot in enterprise systems – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A set of nine vulnerabilities, collectively called ‘PixieFail,’ impact the IPv6 network protocol stack of Tianocore’s EDK II, the open-source...
Feds Warn of AndroxGh0st Botnet Targeting AWS, Azure, and Office 365 Credentials – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 17, 2024NewsroomBotnet / Cloud Security The U.S. Cybersecurity and Infrastructure Security Agency (CISA) and the Federal Bureau of Investigation (FBI)...
Webinar: The Art of Privilege Escalation – How Hackers Become Admins – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 17, 2024The Hacker NewsCyber Threat / Live Webinar In the digital age, the battleground for security professionals is not only...
New iShutdown Method Exposes Hidden Spyware Like Pegasus on Your iPhone – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 17, 2024NewsroomSpyware / Forensic Analysis Cybersecurity researchers have identified a “lightweight method” called iShutdown for reliably identifying signs of spyware...
GitHub Rotates Keys After High-Severity Vulnerability Exposes Credentials – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 17, 2024NewsroomVulnerability / Software Security GitHub has revealed that it has rotated some keys in response to a security vulnerability...
Citrix, VMware, and Atlassian Hit with Critical Flaws — Patch ASAP! – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 17, 2024NewsroomVulnerability / Cyber Threat Citrix is warning of two zero-day security vulnerabilities in NetScaler ADC (formerly Citrix ADC) and...
Zero-Day Alert: Update Chrome Now to Fix New Actively Exploited Vulnerability – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 17, 2024NewsroomBrowser Security / Vulnerability Google on Tuesday released updates to fix four security issues in its Chrome browser, including...
GitHub Rotates Credentials and Patches New Bug – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 GitHub has revealed that service disruption in December was due to it rotating credentials after the discovery of a high-severity bug,...
Google fixed the first actively exploited Chrome zero-day of 2024 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Google fixed the first actively exploited Chrome zero-day of 2024 Google has addressed the first Chrome zero-day vulnerability of the...
Atlassian fixed critical RCE in older Confluence versions – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Atlassian fixed critical RCE in older Confluence versions Atlassian warns of a critical remote code execution issue in Confluence Data...
VMware fixed a critical flaw in Aria Automation. Patch it now! – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini VMware fixed a critical flaw in Aria Automation. Patch it now! VMware warns customers of a critical vulnerability impacting its...
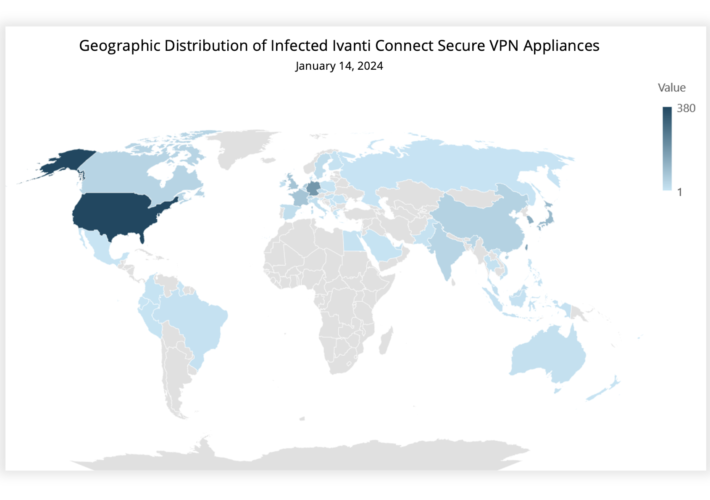
Experts warn of mass exploitation of Ivanti Connect Secure VPN flaws – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Experts warn of mass exploitation of Ivanti Connect Secure VPN flaws Experts warn that recently disclosed Ivanti Connect Secure VPN...
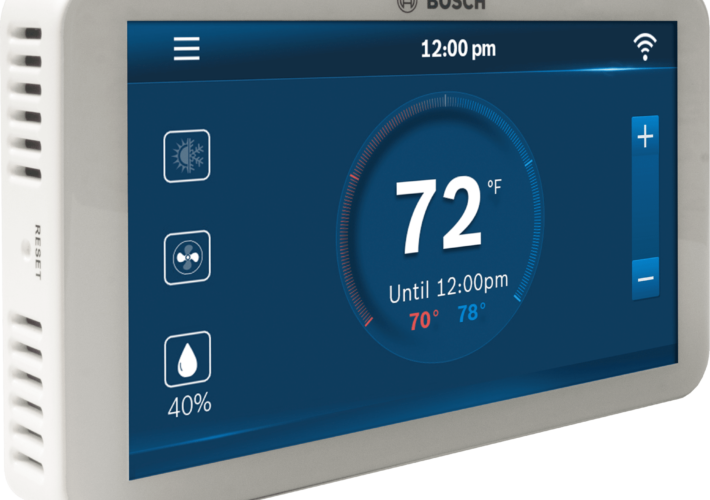
Experts warn of a vulnerability affecting Bosch BCC100 Thermostat – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Experts warn of a vulnerability affecting Bosch BCC100 Thermostat Researchers warn of high-severity vulnerability affecting Bosch BCC100 thermostats. Researchers from...
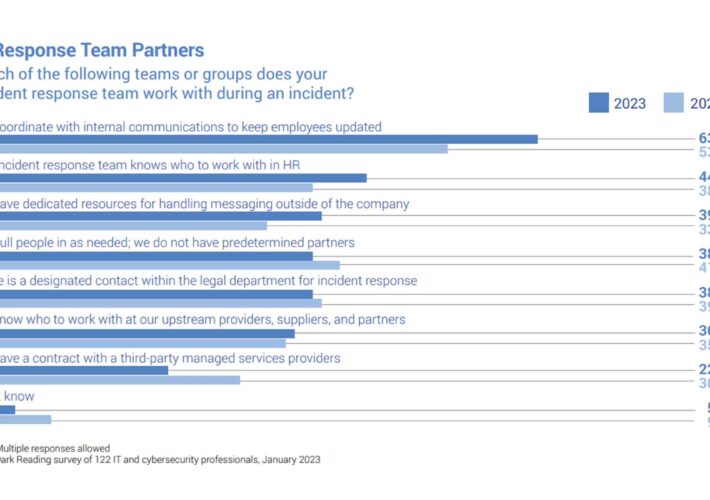
Effective Incident Response Relies on Internal and External Partnerships – Source: www.darkreading.com
Source: www.darkreading.com – Author: Edge Editors Source: How Enterprises Are Responding to the Incident Response Challenge, Dark Reading Enterprise security teams are increasingly collaborating with members...
Accenture and SandboxAQ Collaborate to Help Organizations Protect Data – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE NEW YORK; Jan. 16, 2024 – Accenture (NYSE: ACN) and SandboxAQ are partnering to deliver artificial intelligence (AI) and quantum computing solutions...
Snyk Acquires Helios for Runtime Visibility – Source: www.darkreading.com
Source: www.darkreading.com – Author: Source: Aleks P via Adobe Stock Photo Developer-focused security company Snyk said it has acquired Helios, a startup focused on helping developers...
Savvy Launches Identity-First Security Offering to Combat Toxic Combinations Driving SaaS Risk – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE TEL AVIV, Israel, Jan. 16, 2024 (GLOBE NEWSWIRE) — Savvy, a software-as-a-service (SaaS) security platform provider, today announced its Identity-First Security...
Ivanti Zero-Day Exploits Skyrocket Worldwide; No Patches Yet – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: devilmaya via Alamy Stock Photo Thousands of Ivanti VPN instances have been compromised across the globe in...
Bosch Smart Thermostat Feels the Heat From Firmware Bug – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer A critical vulnerability has been discovered in the widely used, Web-connected Bosch BCC100 thermostat, which is a popular...
Patch ASAP: Max-Critical Atlassian Bug Allows Unauthenticated RCE – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading 2 Min Read Source: Elena Uve via Alamy Stock Photo A max-critical unauthenticated remote code...
Africa, Middle East Lead Peers in Cybersecurity, but Lag Globally – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: SecurityScorecard Both Africa and the Middle East lead their economic peers in cybersecurity, but the regions fall...