Source: thehackernews.com – Author: . Jan 20, 2024NewsroomNetwork Security / Threat Intelligence The U.S. Cybersecurity and Infrastructure Security Agency (CISA) on Friday issued an emergency directive...
Month: January 2024
Microsoft’s Top Execs’ Emails Breached in Sophisticated Russia-Linked APT Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 20, 2024NewsroomCyber Espionage / Emails Security Microsoft on Friday revealed that it was the target of a nation-state attack on...
Invoice Phishing Alert: TA866 Deploys WasabiSeed & Screenshotter Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . The threat actor tracked as TA866 has resurfaced after a nine-month hiatus with a new large-volume phishing campaign to deliver known...
VF Corp December data breach impacts 35 million customers – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini VF Corp December data breach impacts 35 million customers American global apparel and footwear company VF Corp revealed that the December data breach impacted 35.5...
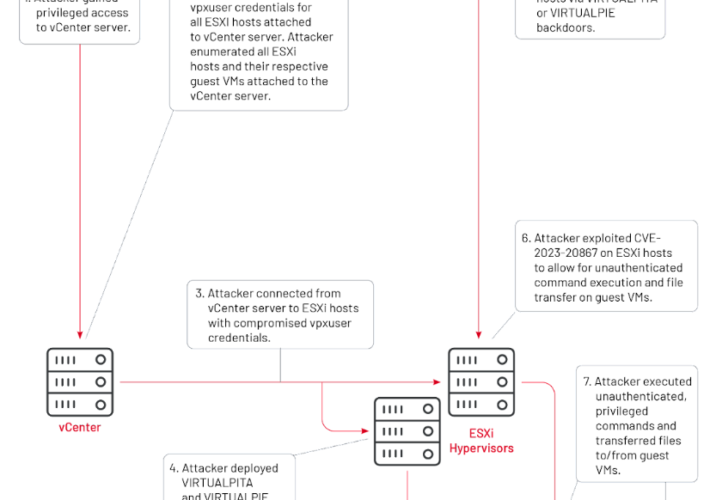
China-linked APT UNC3886 exploits VMware zero-day since 2021 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini China-linked APT UNC3886 exploits VMware zero-day since 2021 China-linked group UNC3886 has been exploiting vCenter Server zero-day vulnerability CVE-2023-34048 since...
Ransomware attacks break records in 2023: the number of victims rose by 128% – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Ransomware attacks break records in 2023: the number of victims rose by 128% Ransomware groups claimed that they successfully targeted...
U.S. CISA warns of actively exploited Ivanti EPMM flaw CVE-2023-35082 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini U.S. CISA warns of actively exploited Ivanti EPMM flaw CVE-2023-35082 U.S. Cybersecurity and Infrastructure Security Agency (CISA) adds Ivanti EPMM...
Top 3 Priorities for CISOs in 2024 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Stephen Lawton, Contributing Writer Source: Panther Media GmbH via Alamy Stock Photo As the new year begins, CISOs gather with their security...
Ransomware Actor Uses TeamViewer to Gain Initial Access to Networks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: monticello via Shutterstock TeamViewer is software that organizations have long used to enable remote support, collaboration, and...
Massive Data Breach at VF Hits 35M Vans, Retail Customers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer Source: Medicimage Education via Alamy Stock Photo Personal data belonging to 35.5 million customers of popular apparel brands...
Third Ivanti Vulnerability Exploited in the Wild, CISA Reports – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading 1 Min Read Source: Elena11 via Shutterstock A critical vulnerability affecting Ivanti Endpoint Manager Mobile (EPMM),...
CISOs Struggle for C-Suite Status Even as Expectations Skyrocket – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Zhanna Hapanovich via Shutterstock CISOs are increasingly being asked to assume the responsibilities of what would normally...
Microsoft: Iran’s Mint Sandstorm APT Blasts Educators, Researchers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: Zoonar GmbH via Alamy Stock Photo The Iran-linked Mint Sandstorm group is targeting Middle Eastern affairs specialists...
Missing the Cybersecurity Mark With the Essential Eight – Source: www.darkreading.com
Source: www.darkreading.com – Author: Arye Zacks Source: Bonaventura via Alamy Stock Photo COMMENTARYIn recent years, Australia has made some key moves to improve the country’s security...
iPhone, Android Ambient Light Sensors Allow Stealthy Spying – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nathan Eddy, Contributing Writer Source: Yalcin Sonat via Alamy Stock Photo The ambient light sensors typically employed in smart devices for adjusting...
CISA’s Road Map: Charting a Course for Trustworthy AI Development – Source: www.darkreading.com
Source: www.darkreading.com – Author: Stu Sjouwerman The agency aims to build a more robust cybersecurity posture for the nation. 4 Min Read Source: GK Images via...
First Step in Securing AI/ML Tools Is Locating Them – Source: www.darkreading.com
Source: www.darkreading.com – Author: Fahmida Y. Rashid, Managing Editor, Features, Dark Reading Source: Andrey Popov via Adobe Stock Photo The growing number of applications incorporating artificial...
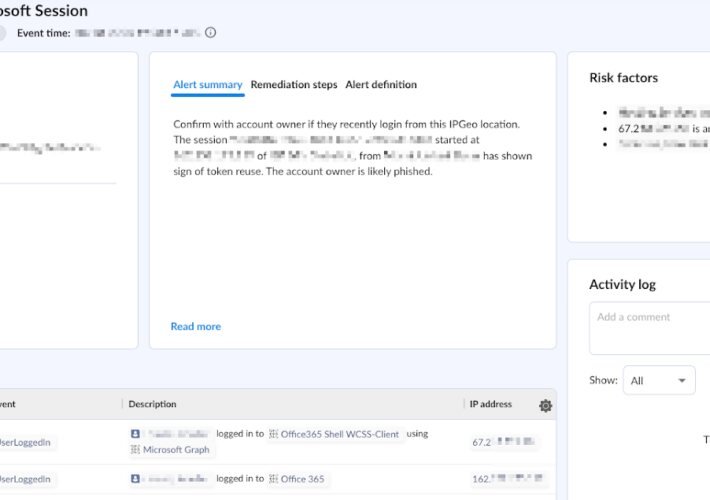
Behind the Breach: Pass-The-Cookie Beyond IdPs – Source: securityboulevard.com
Source: securityboulevard.com – Author: Farah Iyer Pass-The-Cookie (PTC), also known as token compromise, is a common attack technique employed by threat actors in SaaS environments. In...
USENIX Security ’23 – Habiba Farrukh, Reham Mohamed, Aniket Nare, Antonio Bianchi, Z. Berkay Celik – LocIn: Inferring Semantic Location from Spatial Maps in Mixed Reality – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Many thanks to USENIX for publishing their outstanding USENIX Security ’23 Presenter’s content, and the organizations strong commitment to Open...
Introducing DataDome Companion: A Powerful New ChatGPT Application to Build Custom Rules Fast – Source: securityboulevard.com
Source: securityboulevard.com – Author: Andrew Hendry Challenge: Sophisticated Bots Are Evolving Fast Via AI Sophisticated bots targeting your business are evolving rapidly every day. A big...
Empowering You for a Secure 2024: Your Journey with DataDome in Review & Ahead – Source: securityboulevard.com
Source: securityboulevard.com – Author: DataDome 2023 in Review As we know all too well at DataDome, bots are always evolving to perform more attacks and bypass...
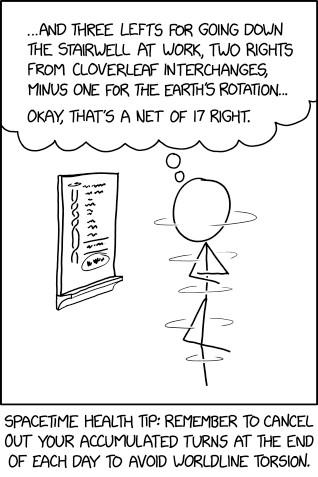
Randall Munroe’s XKCD ‘Net Rotations’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
Latest OpenPubkey Project Initiative Makes SSH More Secure – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard The OpenPubkey project this week shared a mechanism for remotely logging into IT environments based on the OpenID Connect (OIDC)...
Devo Achieves ATO, and Federal CISOs Gain Another Key Resource – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Thelander Of all the SaaS tools used by federal IT teams, cutting-edge cybersecurity tools may be the ones in highest demand....
Response to CISA Advisory (AA24-016A): Known Indicators of Compromise Associated with Androxgh0st Malware – Source: securityboulevard.com
Source: securityboulevard.com – Author: Francis Guibernau On January 16, 2024, the Federal Bureau of Investigation (FBI) and the Cybersecurity and Infrastructure Security Agency (CISA) released a...
USENIX Security ’23 – Hidden Reality: Caution, Your Hand Gesture Inputs in the Immersive Virtual World are Visible to All! – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters: Sindhu Reddy Kalathur Gopal, Diksha Shukla, James David Wheelock, Nitesh Saxena Many thanks to USENIX for publishing their outstanding...
Considerations for outsourcing your penetration testing – Source: securityboulevard.com
Source: securityboulevard.com – Author: Adam King Penetration testing has become a cornerstone of robust cybersecurity strategy. It’s a critical process where experts simulate cyber attacks on...
Microsoft: Russian State Hackers Obtained Access to Leadership Emails – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Computing Giant Says Hackers Did Not Access Customer Data or Production Systems...
XDR and the Benefits of Managed Services – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Extended Detection and Response (XDR) has evolved significantly over the past few years, becoming more critical than ever for organizations in...
French CNIL Imposes Fine of 10 Million Euros on Yahoo – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 General Data Protection Regulation (GDPR) , Standards, Regulations & Compliance Company Fined for Dropping Advertising Cookies Without Consent Akshaya Asokan (asokan_akshaya)...