Source: securityboulevard.com – Author: Deepak Gupta – Tech Entrepreneur, Cybersecurity Author Account takeover – also referred to as credential stuffing or account hijacking – involves cybercriminals...
Month: January 2024
Prosecutors Add to Evidence Against Alleged Vastaamo Hacker – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime Extortion Money Found in Bank Account of Aleksanteri Kivimaki, Prosecutors Say Akshaya Asokan (asokan_akshaya) •...
On Point: Offensive Security for Mobile Network Operators – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Critical Infrastructure Security , Training & Security Leadership Build Resiliency by Simulating Real-World Attacks and Gaining Insight Into Threats CyberEdBoard •...
Microsoft’s Latest Hack Sparks Major Security Concerns – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , IT Risk Management , Legacy Infrastructure Security Experts Warn Tech Giant Faces Potential for Future Cyberattacks...
France’s OFAC to Tackle Cyberthreats Ahead of Olympics – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime French Police Office for Cybercrime Has a Staff of 180 Akshaya Asokan (asokan_akshaya) • January...
Report: Hackers Scammed $7.5M From HHS Grant Payment System – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Healthcare , Industry Specific Money Meant for Poor Communities Stolen as Authorities Issued Phishing Scam Alerts...
SEC confirms X account was hacked in SIM swapping attack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams The U.S. Securities and Exchange Commission confirmed today that its X account was hacked through a SIM-swapping attack on the...
Cracked macOS apps drain wallets using scripts fetched from DNS records – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Hackers are using a stealthy method to deliver to macOS users information-stealing malware through DNS records that hide malicious scripts....
FTC orders Intuit to stop pushing “free” software that isn’t really free – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Today, the U.S. Federal Trade Commission (FTC) ordered Intuit to stop promoting its software products and services as “free” unless...
Malicious web redirect scripts stealth up to hide on hacked sites – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Security researchers looking at more than 10,000 scripts used by the Parrot traffic direction system (TDS) noticed an evolution marked by...
Apple fixes first zero-day bug exploited in attacks this year – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Apple released security updates to address this year’s first zero-day vulnerability exploited in attacks that could impact iPhones, Macs, and...
Ivanti: VPN appliances vulnerable if pushing configs after mitigation – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Ivanti warned admins to stop pushing new device configurations to appliances after applying mitigations because this will leave them vulnerable...
loanDepot cyberattack causes data breach for 16.6 million people – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Mortgage lender loanDepot says that approximately 16.6 million people had their personal information stolen in a ransomware attack disclosed earlier...
Trezor support site breach exposes personal data of 66,000 customers – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Trezor issued a security alert after identifying a data breach that occurred on January 17 due to unauthorized access to their...
Hackers start exploiting critical Atlassian Confluence RCE flaw – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Security researchers are observing exploitation attempts for the CVE-2023-22527 remote code execution flaw vulnerability that affects outdated versions of Atlassian Confluence servers....
North Korean Hackers Weaponize Fake Research to Deliver RokRAT Backdoor – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 22, 2024NewsroomCyber Attack / Hacking Media organizations and high-profile experts in North Korean affairs have been at the receiving end...
MavenGate Attack Could Let Hackers Hijack Java and Android via Abandoned Libraries – Source:thehackernews.com
Source: thehackernews.com – Author: . Several public and popular libraries abandoned but still used in Java and Android applications have been found susceptible to a new...
NS-STEALER Uses Discord Bots to Exfiltrate Your Secrets from Popular Browsers – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 22, 2024NewsroomBrowser Security / Cyber Threat Cybersecurity researchers have discovered a new Java-based “sophisticated” information stealer that uses a Discord...
52% of Serious Vulnerabilities We Find are Related to Windows 10 – Source:thehackernews.com
Source: thehackernews.com – Author: . We analyzed 2,5 million vulnerabilities we discovered in our customer’s assets. This is what we found. Digging into the data The...
With hackers poisoning water systems, US agencies issue incident response guide to boost cybersecurity – Source: www.tripwire.com
Source: www.tripwire.com – Author: Graham Cluley US federal agencies have teamed up to release a cybersecurity best practice guidance for the water and wastewater sector (WWS)....
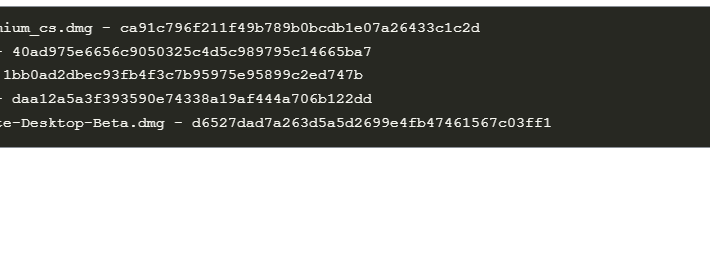
Cracked software beats gold: new macOS backdoor stealing cryptowallets – Source: securelist.com
Source: securelist.com – Author: Sergey Puzan A month ago, we discovered some cracked apps circulating on pirating websites and infected with a Trojan proxy. The malicious...
Data Privacy Week: Lack of Understanding, Underfunding Threaten Data Privacy and Compliance – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A lack of understanding combined with budgetary squeezes are significant obstacles for organization’s navigating data privacy and compliance with data protection...
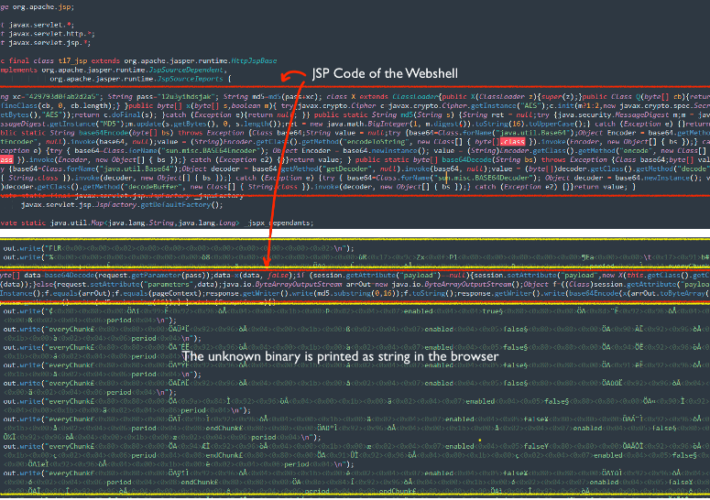
Threat actors exploit Apache ActiveMQ flaw to deliver the Godzilla Web Shell – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Threat actors exploit Apache ActiveMQ flaw to deliver the Godzilla Web Shell Researchers warn of a spike in attacks exploiting...
Cybercriminals leaked massive volumes of stolen PII data from Thailand in Dark Web – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Cybercriminals leaked massive volumes of stolen PII data from Thailand in Dark Web Resecurity researchers warn of massive leak of...
Backdoored pirated applications targets Apple macOS users – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Backdoored pirated applications targets Apple macOS users Researchers warned that pirated applications have been employed to deliver a backdoor to...
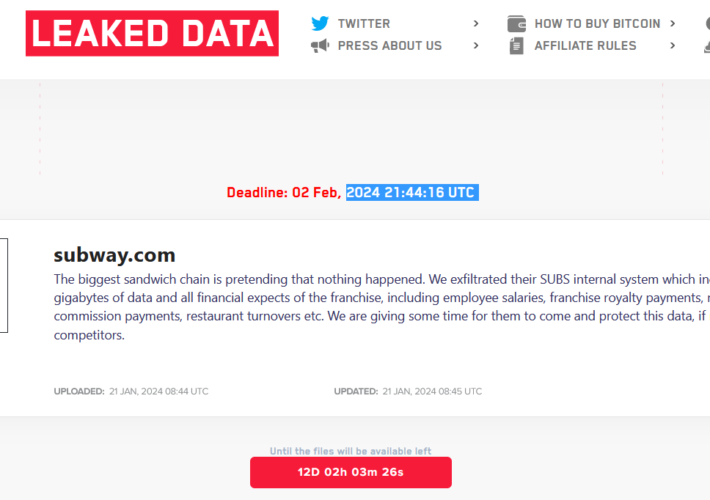
LockBit ransomware gang claims the attack on the sandwich chain Subway – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini LockBit ransomware gang claims the attack on the sandwich chain Subway The LockBit ransomware gang claimed to have hacked Subway,...
FTC Bans InMarket for Selling Precise User Location Without Consent – Source:thehackernews.com
Source: thehackernews.com – Author: . The U.S. Federal Trade Commission (FTC) is continuing to clamp down on data brokers by prohibiting InMarket Media from selling or...
Apache ActiveMQ Flaw Exploited in New Godzilla Web Shell Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 22, 2024NewsroomVulnerability / Malware Cybersecurity researchers are warning of a “notable increase” in threat actor activity actively exploiting a now-patched...
Tietoevry ransomware attack causes outages for Swedish firms, cities – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Finnish IT services and enterprise cloud hosting provider Tietoevry has suffered a ransomware attack impacting cloud hosting customers in one...
Watch out for “I can’t believe he is gone” Facebook phishing posts – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams A widespread Facebook phishing campaign stating, “I can’t believe he is gone. I’m gonna miss him so much,” leads unsuspecting...