Source: www.infosecurity-magazine.com – Author: 1 The government sector has witnessed the most significant growth in crowdsourced security in 2023, marking a 151% increase in vulnerability submissions...
Month: January 2024
North Korea Hacks Crypto: More Targets, Lower Gains – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 North Korea-backed threat actors hacked more crypto platforms than ever in 2023 but stole less of the digital currency in total...
Data Privacy Week: US Data Breaches Surge, 2023 Sees 78% Increase in Compromises – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Written by The number of reported data compromises in the US in 2023 increased by 78% compared to 2022, reaching 3205,...
Southern Water Confirms Data Breach Following Black Basta Claims – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 UK water supplier Southern Water has confirmed that it suffered a data breach after the Black Basta ransomware group appeared to...
Pwn2Own Contest Unearths Dozens of Zero-Day Vulnerabilities – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Some of the world’s top ethical hackers are competing in Tokyo this week, having already found close to 40 zero-day vulnerabilities...
HPE Says SolarWinds Hackers Accessed its Emails – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 An infamous Russian state hacking unit compromised the cloud-based email environment of HPE and exfiltrated data from a “small percentage” of...
Privacy predictions for 2024 – Source: securelist.com
Source: securelist.com – Author: Anna Larkina, Vladislav Tushkanov, Dmitry Momotov Kaspersky Security Bulletin In our previous privacy predictions piece, we outlined trends for 2023. As expected,...
Quantum Computing Skeptics – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Quantum Computing Skeptics Interesting article. I am also skeptical that we are going to see useful quantum computers anytime...
Russia-linked APT group Midnight Blizzard hacked Hewlett Packard Enterprise (HPE) – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Russia-linked APT group Midnight Blizzard hacked Hewlett Packard Enterprise (HPE) Hewlett Packard Enterprise (HPE) revealed that Russia-linked APT group Midnight...
CISA adds Atlassian Confluence Data Center bug to its Known Exploited Vulnerabilities catalog – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini CISA adds Atlassian Confluence Data Center bug to its Known Exploited Vulnerabilities catalog U.S. Cybersecurity and Infrastructure Security Agency (CISA)...
5379 GitLab servers vulnerable to zero-click account takeover attacks – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini 5379 GitLab servers vulnerable to zero-click account takeover attacks Thousands of GitLab servers are vulnerable to zero-click account takeover attacks...
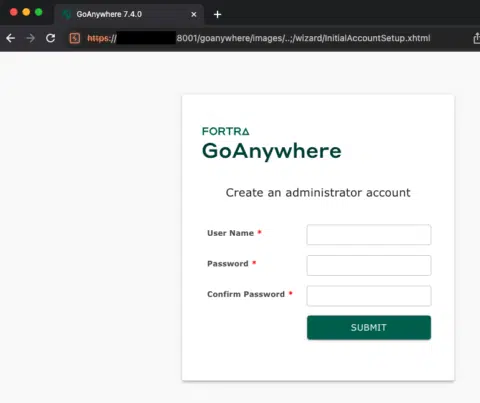
Experts released PoC exploit for Fortra GoAnywhere MFT flaw CVE-2024-0204 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Experts released PoC exploit for Fortra GoAnywhere MFT flaw CVE-2024-0204 Researchers released PoC exploit code for a recently disclosed critical...
Darktrace and Garland Technology Collaborate to Help Businesses Secure Operational Technology Environments – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE CAMBRIDGE, England, Jan. 24, 2024 /PRNewswire/ — Darktrace, a global leader in cyber security AI, and Garland Technology, a leading manufacturer of network TAP...
Peters and Braun Introduce Bipartisan Bill to Bolster Government’s Cybersecurity Capabilities – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE WASHINGTON, D.C. – U.S. Senators Gary Peters (D-MI), Chairman of the Homeland Security and Governmental Affairs Committee, and Mike Braun (R-IN) introduced bipartisan...
Managed Ransomware Detect & Respond (RDR) Offering From Zyston – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE DALLAS, Jan. 24, 2024 /PRNewswire-PRWeb/ — Zyston, a leading Managed Security Services Provider (MSSP) based in Dallas, Texas, is excited to introduce Managed Ransomware Detect...
Atlassian Tightens API After Hacker Scrapes 15M Trello Profiles – Source: www.darkreading.com
Source: www.darkreading.com – Author: Tara Seals, Managing Editor, News, Dark Reading Source: Seemanta Dutta via Alamy Stock Photo About 15 million names, usernames, and emails associated...
Nozomi Networks Delivers Multi-Spectrum Wireless Security Sensor for Global OT and IoT Environments – Source: www.darkreading.com
Source: www.darkreading.com – Author: PRESS RELEASE SAN FRANCISCO, January 24, 2024 — Nozomi Networks Inc., the leader in OT and IoT security, today introduced Guardian Air™, the industry’s only...
ChatGPT Cybercrime Discussions Spike to Nearly 3K Posts on Dark Web – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kristina Beek, Associate Editor, Dark Reading 1 Min Read Source: Ascannio via Shutterstock In new findings from Kaspersky’s Digital Footprint Intelligence service,...
CISA’s Water Sector Guide Puts Incident Response Front & Center – Source: www.darkreading.com
Source: www.darkreading.com – Author: Robert Lemos, Contributing Writer Source: M Production via Shutterstock Water and wastewater utilities last week received new guidance for improving their response...
Jason’s Deli Accounts Compromised by Credential Stuffing – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Source: William Morgan via Alamy Stock Photo Texas-based soup and sandwich slinger Jason’s Deli is alerting members...
Fortra Discloses Critical Auth Bypass Vuln in GoAnywhere MFT – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer Source: Tanoy1412 via Shutterstock A proof-of-concept exploit is now available for a near maximum-severity flaw in Fortra’s GoAnywhere...
Cyber Threat Landscape: 7 Key Findings and Upcoming Trends for 2024 – Source:thehackernews.com
Source: thehackernews.com – Author: . The 2023/2024 Axur Threat Landscape Report provides a comprehensive analysis of the latest cyber threats. The information combines data from the...
China-backed Hackers Hijack Software Updates to Implant “NSPX30” Spyware – Source:thehackernews.com
Source: thehackernews.com – Author: . A previously undocumented China-aligned threat actor has been linked to a set of adversary-in-the-middle (AitM) attacks that hijack update requests from...
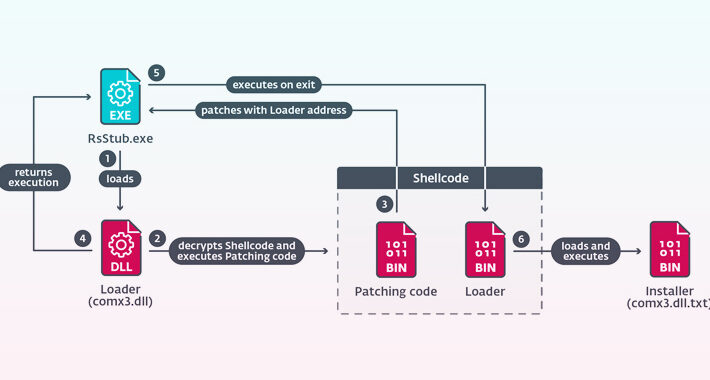
New CherryLoader Malware Mimics CherryTree to Deploy PrivEsc Exploits – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 25, 2024NewsroomThreat Intelligence / Malware Research A new Go-based malware loader called CherryLoader has been discovered by threat hunters in...
Tech Giant HP Enterprise Hacked by Russian Hackers Linked to DNC Breach – Source:thehackernews.com
Source: thehackernews.com – Author: . Jan 25, 2024NewsroomCyber Attack / Data Breach Hackers with links to the Kremlin are suspected to have infiltrated information technology company...
HPE: Russian hackers breached its security team’s email accounts – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Hewlett Packard Enterprise (HPE) disclosed today that suspected Russian hackers known as Midnight Blizzard gained access to the company’s Microsoft...
VexTrio TDS: Inside a massive 70,000-domain cybercrime operation – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A previously unknown traffic distribution system (TDS) named ‘VexTrio’ has been active since at least 2017, aiding 60 affiliates in...
Over 5,300 GitLab servers exposed to zero-click account takeover attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Over 5,300 internet-exposed GitLab instances are vulnerable to CVE-2023-7028, a zero-click account takeover flaw GitLab warned about earlier this month....
UK says AI will empower ransomware over the next two years – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The United Kingdom’s National Cyber Security Centre (NCSC) warns that artificial intelligence (AI) tools will have an adverse near-term impact...
Global fintech firm EquiLend offline after recent cyberattack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan New York-based global financial technology firm EquiLend says its operations have been disrupted after some systems were taken offline in...