Source: www.bleepingcomputer.com – Author: Lawrence Abrams Windows 10 users worldwide report problems installing Microsoft’s January Patch Tuesday updates, getting 0x80070643 errors when attempting to install the...
Day: January 11, 2024
Microsoft Exchange 2019 has reached end of mainstream support – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft announced the end of mainstream support for its Exchange Server 2019 on-premises mail server software on January 9, 2023....
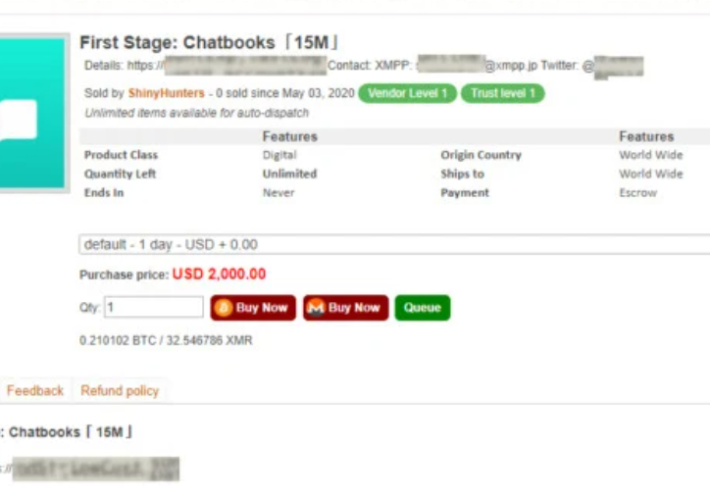
ShinyHunters member gets 3 years in prison for breaching 60 firms – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The U.S. District Court in Seattle sentenced ShinyHunters member Sebastien Raoult to three years in prison and ordered a restitution...
Exploring The Benefits Of Multi-Factor Authentication For Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Toback I understand that security is a top priority for you. That’s why I want to talk about multi-factor authentication (MFA)...
Beyond the Crystal Ball: What API security may look like in 2024 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dana Epp API security isn’t a dark art. But no soothsayer out there can predict what the threat landscape may look like...
USENIX Security ’23 – Rosetta: Enabling Robust TLS Encrypted Traffic Classification in Diverse Network Environments with TCP-Aware Traffic Augmentation – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Authors/Presenters: Renjie Xie, Jiahao Cao, Enhuan Dong, Mingwei Xu, Kun Sun, Qi Li, Licheng Shen, Menghao Zhang Many thanks to...
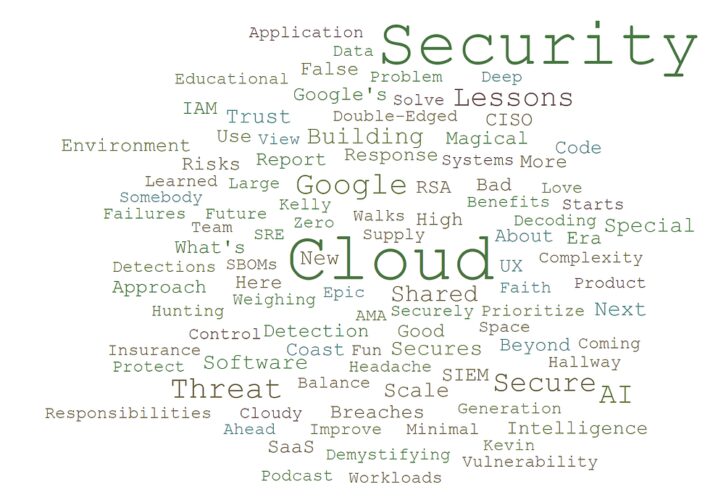
We Are Almost 3! Cloud Security Podcast by Google 2023 Reflections – Source: securityboulevard.com
Source: securityboulevard.com – Author: Anton Chuvakin So, we (Tim and Anton, the crew behind the podcast) wanted to post another reflections blog based on our Cloud...
Kasada Embraces Machine Learning to Reduce Bot Traffic – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard Kasada has updated its bot defense platform to add hundreds of sensors and machine learning algorithms that detect, in real-time,...
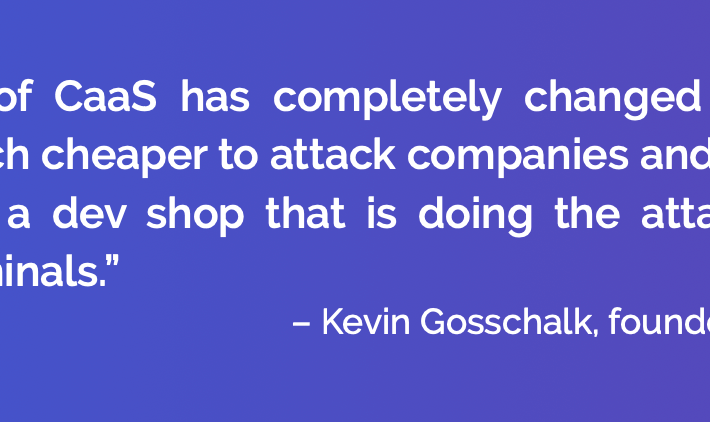
Cybercrime Marketplaces Soar in 2024: All Threats Now Available ‘As-a-Service’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Jenn Jeffers Looking ahead to the digital terrain of 2024, it is clear that cybercrime marketplaces are on the brink of a...
Comic Agilé – Mikkel Noe-Nygaard, Luxshan Ratnaravi – #274 – The World-Renowned Agile Coach – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Wednesday, January 10, 2024 Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News...
China Cracks Apple Private Protocol — AirDrop Pwned – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings Chinese citizens using peer-to-peer wireless comms “must be identified.” The Beijing Bureau of Justice claims it can trace senders of...
In the News | How To Measure Cybersecurity ROI for Schools – Source: securityboulevard.com
Source: securityboulevard.com – Author: Katie Fritchen This article was originally published in Hackernoon on 12.13.23 by Charlie Sander, CEO at ManagedMethods. With the surge in cyber...
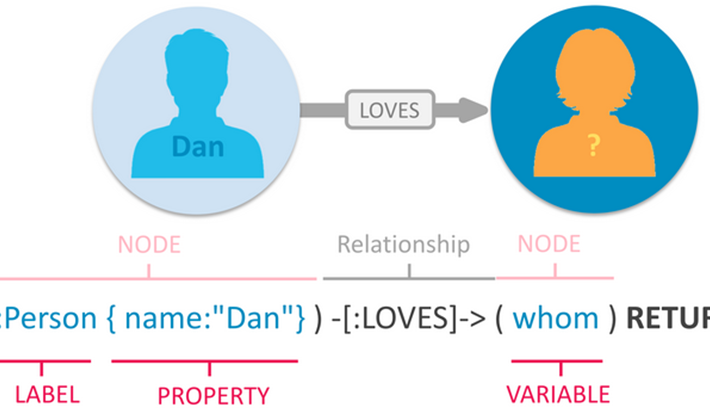
Cypher Queries in BloodHound Enterprise – Source: securityboulevard.com
Source: securityboulevard.com – Author: Nathan D. BloodHound Enterprise (BHE) recently saw the addition of a new, game-changing feature: open-ended Cypher searches. For those unfamiliar, Cypher is...
EU Enhances Cybersecurity Requirements for Agencies – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , IT Risk Management Cyber Regulation Requires EU Agencies to Assess Risks and Report Incidents Akshaya Asokan...
Cybercriminals Bully Cancer Patients With Swatting Threat – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Ransomware Extortion Demands, Lawsuits Pile Up After Fred Hutchinson Cancer Center Hack Marianne Kolbasuk...
How Our Own Insecurity Fuels Global Threats – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Leadership & Executive Communication Professor John Walker on Need for Organizational Introspection, Global Perspective...
EU Commission Examines OpenAI, Microsoft Relationship – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development Commission Says Close Company Connections Make Conditions Ripe for Merger...
Facial Scanning by Burger King in Brazil – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier In 2000, I wrote: “If McDonald’s offered three free Big Macs for a DNA sample, there would be lines around...
ShinyHunters member sentenced to three years in prison – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini ShinyHunters member sentenced to three years in prison A U.S. District Court sentenced ShinyHunters hacker Sebastien Raoult to three years...
HMG Healthcare disclosed a data breach – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini HMG Healthcare disclosed a data breach The Healthcare services provider HMG Healthcare has disclosed a data breach that impacted 40...
Threat actors hacked the X account of the Securities and Exchange Commission (SEC) and announced fake Bitcoin ETF approval – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Threat actors hacked the X account of the Securities and Exchange Commission (SEC) and announced fake Bitcoin ETF approval Threat...
Entire population of Brazil possibly exposed in massive data leak – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Entire population of Brazil possibly exposed in massive data leak The private data of hundreds of millions of Brazilian individuals...
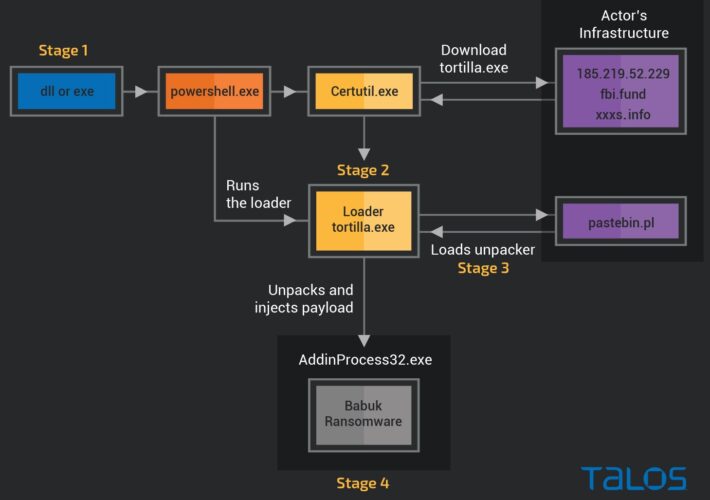
Decryptor for Tortilla variant of Babuk ransomware released – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Decryptor for Tortilla variant of Babuk ransomware released Researchers and the Dutch Police released a decryptor for the Tortilla variant...