Source: www.infosecurity-magazine.com – Author: 1 Data theft is a primary concern for IT decision makers, ahead of ransomware attacks, according to a survey conducted by Integrity...
Month: October 2023
DEF CON 31 – Andrew Brandt’s ‘War Stories – You’re Not George Clooney, And This Isn’t Oceans 11’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
Choosing the Right Cybersecurity Awareness Training Solution: Your Ultimate Checklist – Source: securityboulevard.com
Source: securityboulevard.com – Author: Daniella Balaban Email-based attacks spiked almost 500% in the first half of 2023, making phishing the most popular form of cyberattack for...
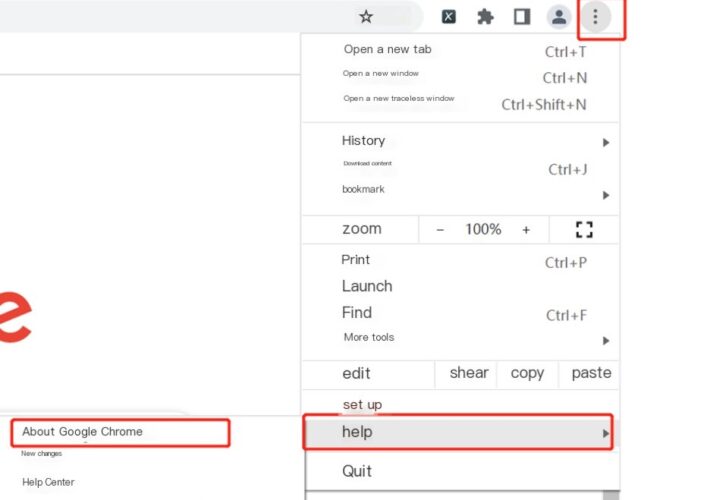
Google Chrome Heap Buffer Overflow Vulnerability (CVE-2023-5217) Notification – Source: securityboulevard.com
Source: securityboulevard.com – Author: NSFOCUS Overview Recently, NSFOCUS CERT found that Google officially fixed a zero-day exploit (CVE-2023-5217), which was caused by the heap buffer overflow...
Hackers Impersonate Meta Recruiter to Target Aerospace Firm – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Social Engineering Lazarus Deploys New Backdoor to Target Aerospace Firm Prajeet...
BlackCat gang claims they stole data of 2.5 million patients of McLaren Health Care – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini BlackCat gang claims they stole data of 2.5 million patients of McLaren Health Care The ALPHV/BlackCat ransomware gang added McLaren...
Security Affairs newsletter Round 439 by Pierluigi Paganini – International edition – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Privacy Overview This website uses cookies to improve your experience while you navigate through the website. Out of these cookies,...
Meet LostTrust ransomware — A likely rebrand of the MetaEncryptor gang – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams The LostTrust ransomware operation is believed to be a rebrand of MetaEncryptor, utilizing almost identical data leak sites and encryptors....
New Marvin attack revives 25-year-old decryption flaw in RSA – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A flaw related to the PKCS #1 v1.5 padding in SSL servers discovered in 1998 and believed to have been...
Cloudflare DDoS protections ironically bypassed using Cloudflare – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Cloudflare’s Firewall and DDoS prevention can be bypassed through a specific attack process that leverages logic flaws in cross-tenant security...
Microsoft fixes Outlook prompts to reopen closed windows – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft has resolved a known issue that caused Outlook Desktop to unexpectedly prompt users to reopen previously closed windows. “This...
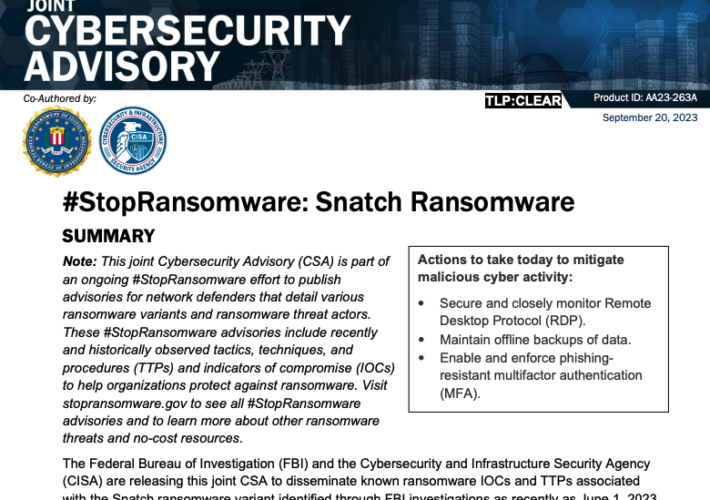
A Closer Look at the Snatch Data Ransom Group – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs Earlier this week, KrebsOnSecurity revealed that the darknet website for the Snatch ransomware group was leaking data about its users and...
Hackers Impersonate Meta Recruiter to Target Aerospace Firm – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime , Social Engineering Lazarus Deploys New Backdoor to Target Aerospace Firm Vasudevan...
Avoid libwebp Electron Woes On macOS With positron – Source: securityboulevard.com
Source: securityboulevard.com – Author: hrbrmstr If you’ve got on this blog (directly, or via syndication) you’d have to have been living under a rock to not...
A Closer Look at the Snatch Data Ransom Group – Source: securityboulevard.com
Source: securityboulevard.com – Author: BrianKrebs Earlier this week, KrebsOnSecurity revealed that the darknet website for the Snatch ransomware group was leaking data about its users and...
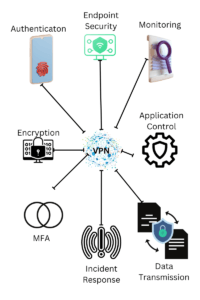
Discover Endpoint VPN in 2023: Unlocking Secure Remote Access – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Toback Introduction In today’s interconnected world, the need for secure remote access to networks and data has never been more crucial....
DEF CON 31 – Lorenzo Cococcia ‘s ‘War Stories – Finding Foes And Yourself With Latency Trilateration’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/09/def-con-31-lorenzo-cococcia-s-war-stories-finding-foes-and-yourself-with-latency-trilateration/ Category & Tags: Security Bloggers Network,Cybersecurity,cybersecurity education,DEF...
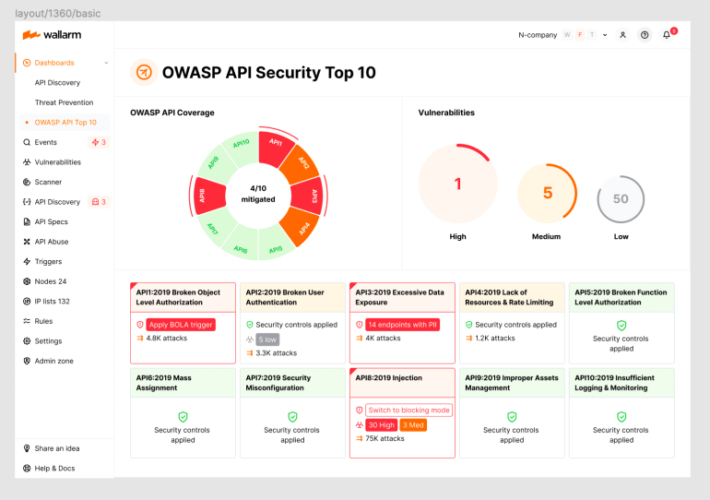
2023 OWASP Top-10 Series: API10:2023 Unsafe Consumption of APIs – Source: securityboulevard.com
Source: securityboulevard.com – Author: wlrmblog Welcome to the 11th post in our weekly series on the new 2023 OWASP API Security Top-10 list, with a particular...
Anomaly Detection in Cybersecurity for Dummies by Ram Vaidyanathan
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Blue Team Cheat Sheets by Chris Davis
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Security Awareness for dummies series by Ira Winkler
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
So You Want To Be a Hacker – A story guide by Logan Simpson
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CYBER ESSENTIALS STARTER KIT – The Basics for Building a Culture of Cyber Readiness – By CISA Cybersecurity and Infrastructure Security Agency
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Cibersecurity Capability Maturity Model (C2M2) by US Department of Energy
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The Zero Trust Model in Cybersecurity – Towards undesstanding and deployment – Community Paper – World Economic Forum
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Report on the Biden Laptop by Marco Polo
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
The SOC of the Future by Jeffrey Wheat (Lumu`s CTO)
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
10 WAYS ASSET VISIBILITY BUILDS THE FOUNDATION FOR OT CYBERSECURITY – KNOWING THE DATA YOU NEED TO COLLECT ISN’T ENOUGH IF YOU DON’T HAVE FULL ASSET VISIBILITY by DRAGOS
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Personal Cyber Security First Steps by Australian Government – ACSC
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
HTML smuggling: A Stealthier Approach to Deliver Malware by CYFIRMA
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...