Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Governance & Risk Management , Next-Generation Technologies & Secure Development Open-Source Tool Used By of...
Month: October 2023
The Hacker Perspective on Generative AI and Cybersecurity – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Unveiling the Risks and Insights: A Hacker’s Take on Generative AI and Cybersecurity Michiel Prins, Co-founder of HackerOne • October 3,...
Red Cross Tells Hacktivists: Stop Targeting Hospitals – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Of Course, KillNet and Its Ilk Don’t Care – They’re Likely Proxies...
Live Webinar | The Promise (and Peril) of A.I. in Healthcare – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Chris Logan SVP and Chief Security Officer, Censinet Chris Logan has more than 25 years in IT operations and strategy. Previously...
Attackers Exploit SQL Server to Penetrate Azure Cloud – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cloud Security , Security Operations Microsoft Discloses Unusual Hacking Attempt Prajeet Nair (@prajeetspeaks) • October 4, 2023 Image: Shutterstock...
Cyber Mavens Slam Europe’s Cyber Resilience Act – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Legislation & Litigation , Patch Management Experts Warn Vulnerability Disclosure to Government Agencies Increases Hacking Risks...
Insurance Companies Have a Lot to Lose in Cyberattacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: Stephen Lawton, Contributing Writer Insurance companies have a huge target on their proverbial backs as cyber attackers increase their focus on an...
Nokia Selected by Brazil’s K2 Telecom As Partner to Strengthen its Security and Create Revenue Streams – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 PRESS RELEASE 04 October 2023 — São Paulo, Brazil – Nokia today announced that it has been selected with partner DPR...
Trend Micro Drives Latest Phase of Channel Prosperity and Engagement – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 PRESS RELEASE DALLAS, Oct. 4, 2023 /PRNewswire/ — Global cybersecurity leader Trend Micro Incorporated (TYO: 4704; TSE: 4704) has announced a complete redesign to the company’s...
ForAllSecure Announces First Dynamic Software Bill of Materials for Application Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 PRESS RELEASE PITTSBURGH,Oct. 4, 2023/PRNewswire/ —ForAllSecure, the world’s most advanced application security testing company, today announced the debut of its runtime dynamic...
Okta Launches Cybersecurity Workforce Development Initiative to Help Close the Tech and Cybersecurity Skills Gap – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 SAN FRANCISCO — October 4, 2023 –– Okta, Inc. (NASDAQ:OKTA), the leading independent identity partner, today announced the launch of a...
37% Intimidated, 39% Frustrated With Online Security Highlighting Digital Anxiety – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 WASHINGTON – October 3, 2023 – The National Cybersecurity Alliance (NCA), the nation’s leading nonprofit empowering a more secure and interconnected world, and CybSafe, the...
BeyondID Introduces Identity-First Model for Zero-Trust Maturity – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 SAN FRANCISCO, Oct. 2, 2023 /PRNewswire/ — BeyondID, a leading managed identity solutions provider, today announced the industry’s first solution that accurately conveys the...
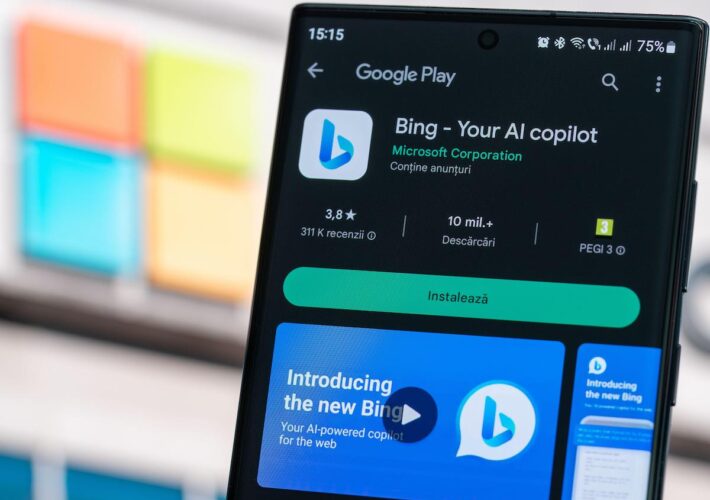
Bing Chat LLM Tricked Into Circumventing CAPTCHA Filter – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading This past week, a user on the X platform (formerly known as Twitter) devised and successfully executed...
Malicious Ads in Bing Chat – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier HomeBlog Comments K.S. • October 4, 2023 8:01 AM Advertising in search allows bypassing of any implemented relevance metric. The...
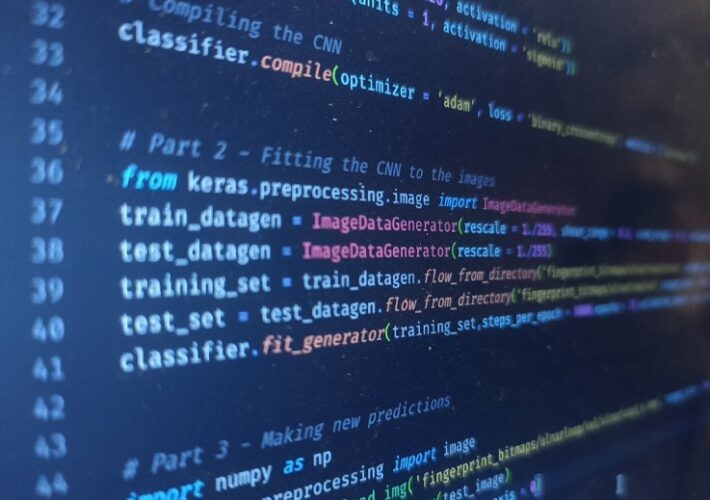
Hundreds of malicious Python packages found stealing sensitive data – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A malicious campaign that researchers observed growing more complex over the past half year, has been planting on open-source platforms...
Apple emergency update fixes new zero-day used to hack iPhones – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Apple released emergency security updates to patch a new zero-day security flaw exploited in attacks targeting iPhone and iPad users. “Apple...
Atlassian patches critical Confluence zero-day exploited in attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Australian software company Atlassian released emergency security updates to fix a maximum severity zero-day vulnerability in its Confluence Data Center...
Researchers warn of 100,000 industrial control systems exposed online – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas About 100,000 industrial control systems (ICS) were found on the public web, exposed to attackers probing them for vulnerabilities and...
Cisco fixes hard-coded root credentials in Emergency Responder – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Cisco released security updates to fix a Cisco Emergency Responder (CER) vulnerability that let attackers log into unpatched systems using...
Microsoft: Hackers target Azure cloud VMs via breached SQL servers – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Hackers have been observed trying to breach cloud environments through Microsoft SQL Servers vulnerable to SQL injection. Microsoft’s security researchers...
Enhancing your application security program with continuous monitoring – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sponsored by Outpost24 Historically, cybersecurity models have been largely reactive. Organizations would assess vulnerabilities at specified intervals, typically following a security incident...
Sony confirms data breach impacting thousands in the U.S. – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Sony Interactive Entertainment (Sony) has notified current and former employees and their family members about a cybersecurity breach that exposed...
Emergency alert on US phones and TVs today — Don’t worry, it’s just a test – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan The U.S. Federal Emergency Management Agency (FEMA) and the Federal Communications Commission (FCC) will run an emergency alert test today...
Researchers Link DragonEgg Android Spyware to LightSpy iOS Surveillanceware – Source:thehackernews.com
Source: thehackernews.com – Author: . Oct 04, 2023THNMobile Security / Spyware New findings have identified connections between an Android spyware called DragonEgg and another sophisticated modular...
Wing Disrupts the Market by Introducing Affordable SaaS Security – Source:thehackernews.com
Source: thehackernews.com – Author: . Oct 04, 2023The Hacker NewsSaaS Security / Enterprise Security Today, mid-sized companies and their CISOs are struggling to handle the growing...
Rogue npm Package Deploys Open-Source Rootkit in New Supply Chain Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Oct 04, 2023THNSupply Chain / Malware A new deceptive package hidden within the npm package registry has been uncovered deploying an...
Microsoft Warns of Cyber Attacks Attempting to Breach Cloud via SQL Server Instance – Source:thehackernews.com
Source: thehackernews.com – Author: . Oct 04, 2023THNCloud Security / Cyber Threat Microsoft has detailed a new campaign in which attackers unsuccessfully attempted to move laterally...
Apple’s Face ID Cheat Sheet: What It Is and How to Use It – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Andy Wolber Apple made a big change in November 2017 when it released the iPhone X: It ditched Touch ID fingerprint security...
This Top-Rated Ad Blocker is Just $25 Through October 15th – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: TechRepublic Academy on October 4, 2023, 6:59 AM EDT This Top-Rated Ad Blocker is Just $25 Through October 15th AdGuard gets rid...