Source: securityaffairs.com – Author: Pierluigi Paganini UK Greater Manchester Police disclosed a data breach Pierluigi Paganini September 14, 2023 UK Greater Manchester Police (GMP) disclosed a...
Day: September 15, 2023
The iPhone of a Russian journalist was infected with the Pegasus spyware – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The iPhone of a Russian journalist was infected with the Pegasus spyware Pierluigi Paganini September 14, 2023 The iPhone of...
Kubernetes flaws could lead to remote code execution on Windows endpoints – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Kubernetes flaws could lead to remote code execution on Windows endpoints Pierluigi Paganini September 14, 2023 Researchers discovered three security...
How the U.S. Government Views the Bright, Dark Sides of AI – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development White House, DOD, DHS Leaders Reveal How their Agencies Use...
Breach Roundup: Pegasus on Exiled Russian Journalist’s Phone – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Also: 9-Year Prison Sentence for Insider Trading Fueled by Password Theft Anviksha More (AnvikshaMore) • September 14, 2023 Image:...
Panel | Secrets on the Loose: How to Get the Most out of Your Secrets Management Program – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Robert Sawyer Sr. Director of Solutions Marketing, CyberArk Robert Sawyer is a software engineer turned marketing leader with over 20 years...
Live Fireside Chat | Getting Governance that Works – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
China Denies Banning Government Use of Apple iPhones – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Geo Focus: Asia , Geo-Specific , Government China Cites Apple Security Flaws in Warning to Foreign Mobile Device Manufacturers Jayant Chakravarti...
U.S. Senator Seeks Input on Ways to Protect Patient Privacy – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Healthcare , HIPAA/HITECH , Industry Specific Inquiry is Latest Move by a Lawmaker Hinting of New Data Protection Legislation Marianne Kolbasuk...
BSides Buffalo 2023 – Magno Logan – Hacking GitHub Actions – Abusing GitHub And Azure For Fun And Profit – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Very Important – Follow available standards and guidelines (NIST, CIS, SLSA etc.) Important – Taken significant steps to secure our...
Shifting Perspectives and Regulations Relating to Consent Management – Source: securityboulevard.com
Source: securityboulevard.com – Author: ForgeRock Guest Contributor Businesses have a certain responsibility to disclose how consumer data is being used, and if they don’t, they face...
Patch Tuesday Update – September 2023 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Bill Niester Fall is here in much of America, and amidst the crunching of football pads and the smashing of apples for...
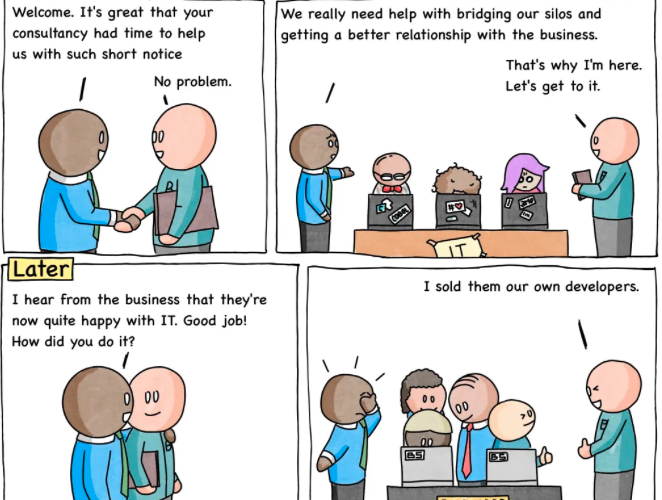
Comic Agilé – Mikkel Noe-Nygaard, Luxshan Ratnarav – #258 — The Business Are Happy – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Very Important – Follow available standards and guidelines (NIST, CIS, SLSA etc.) Important – Taken significant steps to secure our...
Automating Kubernetes Cost Reductions – Source: securityboulevard.com
Source: securityboulevard.com – Author: Anthony Day Meet Rosie & Her Architecture Cloud costs are a common pain point. We hear about it all the time from...
What is Tier Zero — Part 2 – Source: securityboulevard.com
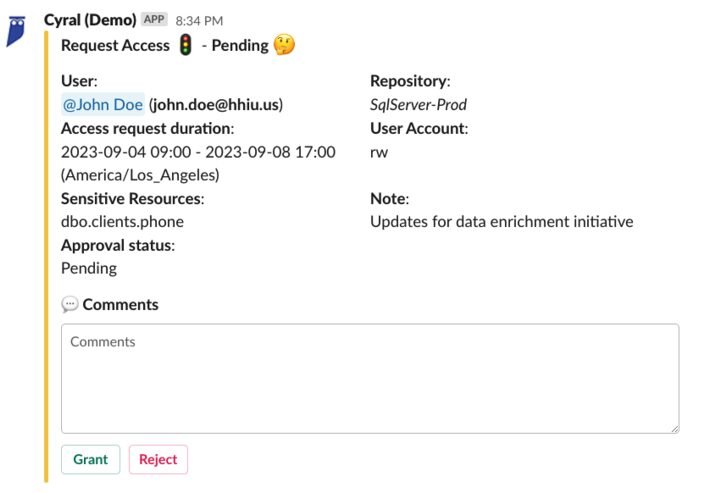
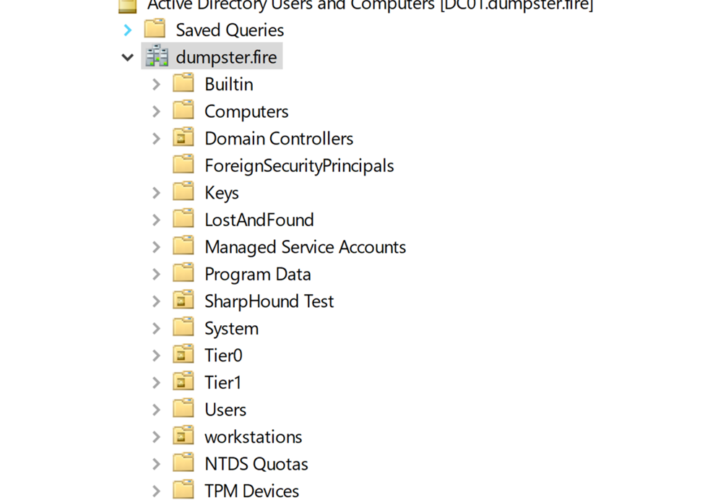
Source: securityboulevard.com – Author: Jonas Bülow Knudsen What is Tier Zero — Part 2 Round 2! This is Part 2 of our webinar and blog post series Defining the...
BSides Buffalo 2023 – Destiney M. Plaza – I Spy With My Hacker Eye – How Hackers Use Public Info To Crack Your Creds – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Very Important – Follow available standards and guidelines (NIST, CIS, SLSA etc.) Important – Taken significant steps to secure our...
Microsoft’s September 2023 Patch Tuesday Addresses 2 Zero-Days, 59 Vulnerabilities – Source: securityboulevard.com
Source: securityboulevard.com – Author: Team Nuspire Microsoft has released its latest release of security updates for September 2023. In its most recent Patch Tuesday, the tech...
A Second Major British Police Force Suffers a Cyberattack in Less Than a Month – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press Personal details of thousands of police officers and staff from Greater Manchester Police have been hacked from a company that...
Caesars Confirms Ransomware Hack, Stolen Loyalty Program Database – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Caesars Entertainment, Inc., a well-known global hospitality brand, has been hacked by a cybercrime gang that stole a vast chunk...
MGM casino’s ESXi servers allegedly encrypted in ransomware attack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ionut Ilascu An affiliate of the BlackCat ransomware group, also known as APLHV, is behind the attack that disrupted MGM Resorts’ operations, forcing...
Auckland transport authority hit by suspected ransomware attack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas The Auckland Transport (AT) transportation authority in New Zealand is dealing with a widespread outage caused by a cyber incident,...
Windows 11 Snipping Tool gets OCR support to copy text from images – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft has added text recognition support to the latest Snipping Tool build, allowing users to select and copy text from...
Caesars Entertainment confirms ransom payment, customer data theft – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Caesars Entertainment, self-described as the largest U.S. casino chain with the most extensive loyalty program in the industry, says it...
Iranian hackers breach defense orgs in password spray attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Image: Midjourney Microsoft says an Iranian-backed threat group has targeted thousands of organizations in the U.S. and worldwide in password...
Windows 11 ‘ThemeBleed’ RCE bug gets proof-of-concept exploit – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Proof-of-concept exploit code has been published for a Windows Themes vulnerability tracked as CVE-2023-38146 that allows remote attackers to execute code....
Manchester Police officers’ data exposed in ransomware attack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas United Kingdom’s Greater Manchester Police (GMP) said earlier today that some of its employees’ personal information was impacted by a...
Criminal IP Elevates Payment Security with PCI DSS Level 1 Certification – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sponsored by Criminal IP With payment card information being an enticing target for cyber attackers, the safeguarding of payment card transactions is...
Fake Cisco Webex Google Ads abuse tracking templates to push malware – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Threat actors use Google Ads tracking templates as a loophole to create convincing Webex software search ads that redirect users...
Manchester Police Officers’ Data Breached in Third-Party Attack – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Officers working undercover or in sensitive roles like intelligence could be exposed Original Post URL: https://www.infosecurity-magazine.com/news/manchester-police-data-breached/ Category & Tags: – Views:...
Elon Musk in Hot Water With FTC Over Twitter Privacy Issues – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A new court filing from the US Department of Justice suggests the billionaire “may have jeopardized data privacy and security” at...