Source: www.govinfosecurity.com – Author: 1 Critical Infrastructure Security , Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime Symantec Finds APT41 Fingerprint in a ShadowPad Trojan...
Day: September 14, 2023
Microsoft Patches Fix Word and Streaming Services Zero-Days – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Governance & Risk Management , Patch Management Patch Contains 59 Bugs Fixes, Including 5 Critical Ones Mihir Bagwe (MihirBagwe) • September...
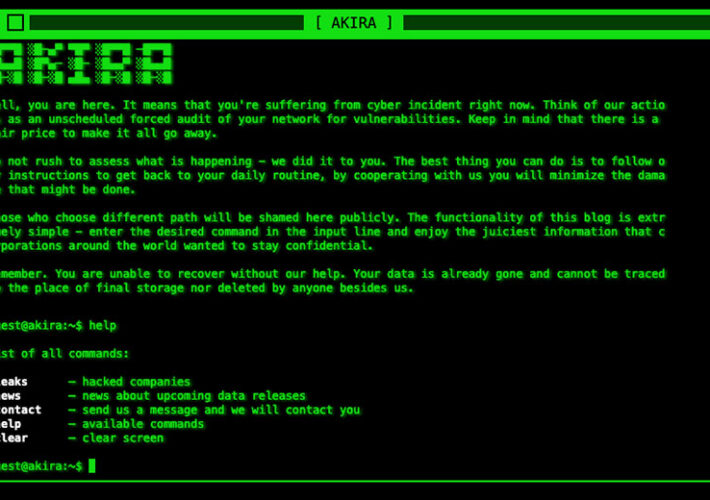
Feds Warn Healthcare Sector of Akira Ransomware Threats – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Fraud Management & Cybercrime , Governance & Risk Management , Healthcare HHS: Group Seems to Favor Targeting Small & Midsized Entities...
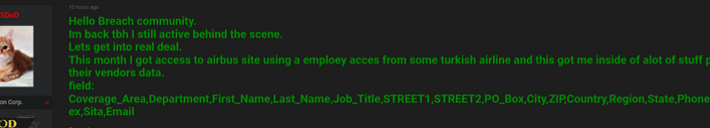
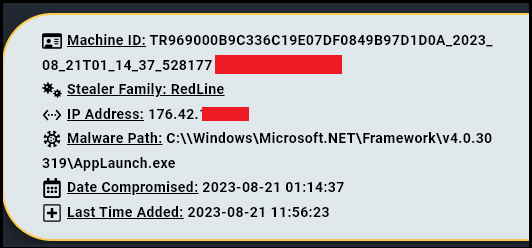
FBI Hacker Dropped Stolen Airbus Data on 9/11 – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs In December 2022, KrebsOnSecurity broke the news that a cybercriminal using the handle “USDoD” had infiltrated the FBI‘s vetted information sharing...
Threat actor leaks sensitive data belonging to Airbus – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Threat actor leaks sensitive data belonging to Airbus Pierluigi Paganini September 14, 2023 The multinational aerospace corporation Airbus has launched an investigation...
A new ransomware family called 3AM appears in the threat landscape – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A new ransomware family called 3AM appears in the threat landscape Pierluigi Paganini September 13, 2023 3AM is a new...
Redfly group infiltrated an Asian national grid as long as six months – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Redfly group infiltrated an Asian national grid as long as six months Pierluigi Paganini September 13, 2023 A threat actor...
Mozilla fixed a critical zero-day in Firefox and Thunderbird – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Mozilla fixed a critical zero-day in Firefox and Thunderbird Pierluigi Paganini September 13, 2023 Mozilla addressed a critical zero-day vulnerability...
Microsoft September 2023 Patch Tuesday fixed 2 actively exploited zero-day flaws – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Microsoft September 2023 Patch Tuesday fixed 2 actively exploited zero-day flaws Pierluigi Paganini September 13, 2023 Microsoft September 2023 Patch...
Tech Industry Leaders Endorse Regulating Artificial Intelligence at Rare Summit in Washington – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press The nation’s biggest technology executives on Wednesday loosely endorsed the idea of government regulations for artificial intelligence at an unusual...
AuthMind Scores $8.5M Seed Funding for ITDR Tech – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Maryland startup AuthMind has raised $8.5 million in seed-stage funding to build security software in the competitive Identity Threat Detection...
Distributed Energy Resources Get Cybersecurity Boost with $39M DOE Funding – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The US Department of Energy (DOE) on Tuesday announced a total of $39 million in funding for nine National Laboratory...
CISOs and Board Reporting – an Ongoing Problem – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend For CISOs to gain the support of the board, they must first translate and report highly technical cybersecurity concerns and...
US Agencies Publish Cybersecurity Report on Deepfake Threats – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Several US government agencies on Tuesday published a cybersecurity information sheet focusing on the threat posed by deepfakes and how...
How Next-Gen Threats Are Taking a Page From APTs – Source: www.securityweek.com
Source: www.securityweek.com – Author: Derek Manky One of the ongoing threats that defenders have to deal with is APTs: advanced persistent threats. APT attackers use more...
CISA Releases Open Source Software Security Roadmap – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The US Cybersecurity and Infrastructure Security Agency (CISA) on Tuesday published a new document detailing its plan to support the...
China Says No Law Banning iPhone Use in Govt Agencies – Source: www.securityweek.com
Source: www.securityweek.com – Author: AFP China said Wednesday it was following media reports about suspected security issues with iPhones but insisted there was no ban on its officials...
macOS Info-Stealer Malware ‘MetaStealer’ Targeting Businesses – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire A recently identified macOS information stealer has been targeting businesses to exfiltrate keychain and other valuable information, cybersecurity firm SentinelOne...
Airbus Launches Investigation After Hacker Leaks Data – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Airbus has launched an investigation after a hacker leaked information allegedly stolen from the French aerospace giant’s systems. Cybercrime intelligence...
New Microsoft Teams Phishing Campaign Targets Corporate Employees – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Microsoft has detailed a new phishing campaign in which corporate employees are targeted via MS Teams. The tech giant said the...
MGM Criticized for Repeated Security Failures – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 As the dust settles for MGM and systems are restored following a suspected cyber-attack, cybersecurity experts are now scrutinizing the hospitality...
Chilling Lack of Cyber Experts in UK Government, Finds Parliamentary Inquiry – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The UK Government suffers from a major shortage of cybersecurity experts, putting critical services at high risk of cyber-attacks, a new...
Microsoft Fixes Two Zero-Day Bugs Used in Attacks – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Microsoft patched two zero-day vulnerabilities being actively exploited in the wild as part of its September Patch Tuesday yesterday. The first...
CISA Publishes Plan to Enhance Open Source Security – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A leading US security agency has released a long-awaited plan detailing how it will enhance open source security for both federal...
UK ICO and NCSC Set to Share Anonymized Threat Intelligence – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The UK’s data protection regulator and its leading security agency have signed an agreement to cooperate more closely on cyber incidents,...
Data Security in MySQL is an evolving compliance and threat landscape – Source: securityboulevard.com
Source: securityboulevard.com – Author: Min-Hank Ho, VP Product Management MySQL remains one of the most popular relational databases today. It offers a variety of data security...
BSides Buffalo 2023 – Stephen Mitchell – Building A Security Data Infrastructure – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/09/bsides-buffalo-2023-stephen-mitchell-building-a-security-data-infrastructure/ Category & Tags: CISO Suite,Governance, Risk &...
Black Hat Fireside Chat: The impactful role crowdsourced security intelligence must play – Source: securityboulevard.com
Source: securityboulevard.com – Author: bacohido By Byron V. Acohido From Kickstarter to Wikipedia, crowdsourcing has become a part of everyday life. Sharing intel for a greater...
Patch EVERYTHING: Widely Used ‘WebP’ Code has Critical Bug – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings Critical vuln in libwebp: Go get updates to Chrome, Firefox, Edge, Slack and more. After Apple’s BLASTPASS patches, come a...
Randall Munroe’s XKCD ‘Brassica’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman via the comic artistry and dry wit of Randall Munroe, maker of XKCD! Permalink *** This is a Security Bloggers...