Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: Two major astronomy observatories – the Gemini North Telescope in Hawaii and the Gemini South Telescope in Chile –...
Day: September 5, 2023
News Alert: Reflectiz declares war on Magecart web-skimming attacks as holidays approach – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido Tel Aviv, Israel, Sept. 5, 2023 — Reflectiz, a cybersecurity company specializing in continuous web threat management offers an exclusive, fully...
STEPS FORWARD: Regulators are on the move to set much needed IoT security rules of the road – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Byron V. Acohido New government rules coupled with industry standards meant to give formal shape to the Internet of Things...
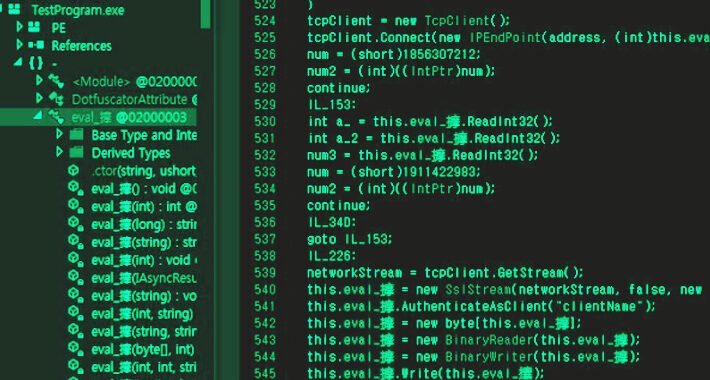
New BLISTER Malware Update Fuelling Stealthy Network Infiltration – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 05, 2023THNCyber Threat / Malware An updated version of a malware loader known as BLISTER is being used as part...
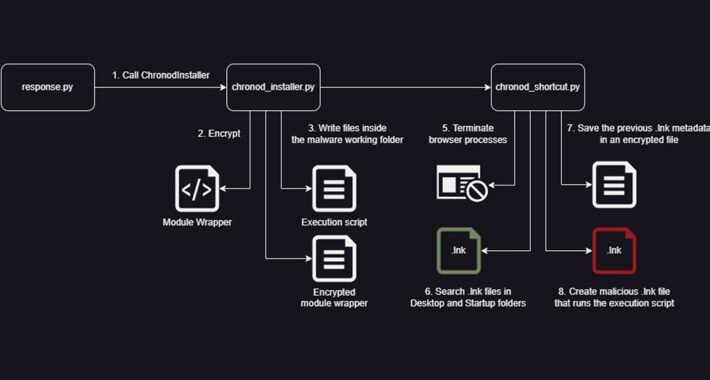
New Python Variant of Chaes Malware Targets Banking and Logistics Industries – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 05, 2023THNCyber Threat / Malware Banking and logistics industries are under the onslaught of a reworked variant of a malware...
Way Too Vulnerable: Join this Webinar to Understand and Strengthen Identity Attack Surface – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 05, 2023The Hacker NewsAttack Surface / Identity Threats In today’s digital age, it’s not just about being online but how...
Key Cybersecurity Tools That Can Mitigate the Cost of a Breach – Source:thehackernews.com
Source: thehackernews.com – Author: . IBM’s 2023 installment of their annual “Cost of a Breach” report has thrown up some interesting trends. Of course, breaches being...
Researchers Warn of Cyber Weapons Used by Lazarus Group’s Andariel Cluster – Source:thehackernews.com
Source: thehackernews.com – Author: . Sep 05, 2023THNCyber Attack / Malware The North Korean threat actor known as Andariel has been observed employing an arsenal of...
Mend.io SAML Vulnerability Exposed – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 WithSecure has unveiled a new security vulnerability in Mend.io’s application security platform today, raising concerns about data privacy and potential exploitation. ...
Airlines Battle Surge in Loyalty Program Fraud – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Cyber fraudsters have been observed increasingly exploiting vulnerabilities in air miles and customer service systems across the EU, the UK and...
UK Electoral Commission Fails Cybersecurity Test Amid Data Breach – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The UK’s Electoral Commission has admitted to failing a crucial cybersecurity test at the same time that hackers breached its systems,...
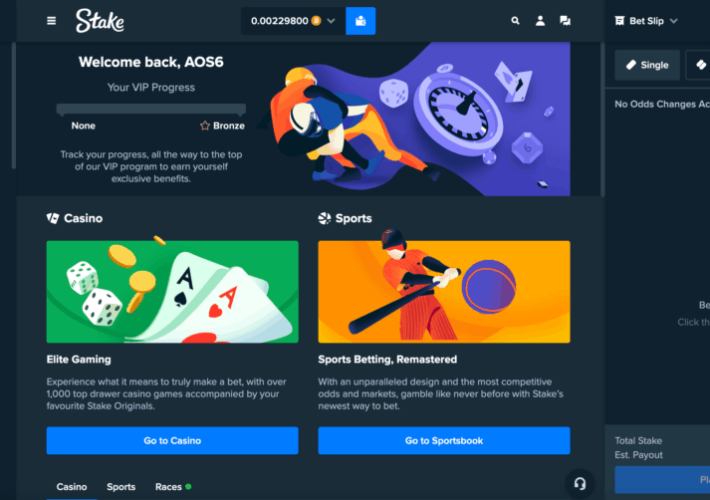
Hackers stole $41M worth of crypto assets from crypto gambling firm Stake – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Hackers stole $41M worth of crypto assets from crypto gambling firm Stake Pierluigi Paganini September 05, 2023 Crypto gambling site...
Freecycle data breach impacted 7 Million users – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Freecycle data breach impacted 7 Million users Pierluigi Paganini September 05, 2023 The nonprofit organization Freecycle Network (Freecycle.org) confirmed that...
Meta disrupted two influence campaigns from China and Russia – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Meta disrupted two influence campaigns from China and Russia Pierluigi Paganini September 05, 2023 Meta disrupted two influence campaigns orchestrated...
A massive DDoS attack took down the site of the German financial agency BaFin – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A massive DDoS attack took down the site of the German financial agency BaFin Pierluigi Paganini September 05, 2023 A...
Hackers Target High-Privileged Okta Accounts via Help Desk – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Threat actors are using social engineering to convince IT desk personnel to reset multifactor authentication (MFA) for...
Data Initiatives Force Closer Partnership Between CISOs, CDOs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Big data initiatives and the growing adoption of generative AI and other data-driven projects are accelerating...
Russia Undertakes Disinformation Campaign Across Africa – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Russia has launched sympathetic media outlets, courted anti-French public support and created civil society organizations in turbulent...
How Companies Can Cope With the Risks of Generative AI Tools – Source: www.darkreading.com
Source: www.darkreading.com – Author: Shay Levi, Co-Founder & CTO, Noname Security Everyone’s experienced the regret of telling a secret they should’ve kept. Once that information is...
As LotL Attacks Evolve, So Must Defenses – Source: www.darkreading.com
Source: www.darkreading.com – Author: Troy Gill, Senior Manager of Threat Research, OpenText Cybersecurity What began as malware utilizing native applications and processes to hide malicious activity, living-off-the-land...
Name That Edge Toon: Prized Possessions – Source: www.darkreading.com
Source: www.darkreading.com – Author: John Klossner, Cartoonist Some people collect trading cards and comic books. Others collect coins and stamps. The guy above? We call on...
Inconsistencies in the Common Vulnerability Scoring System (CVSS) – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier Interesting research: Shedding Light on CVSS Scoring Inconsistencies: A User-Centric Study on Evaluating Widespread Security Vulnerabilities Abstract: The Common Vulnerability...
LockBit ransomware gang steals data related to security of UK military bases – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley An attack by the notorious LockBit ransomware gang stole 10 GB of data from a company that provides high-security fencing...
Mitigating AI Risks: UK Calls for Robust Guardrails – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Artificial Intelligence & Machine Learning , General Data Protection Regulation (GDPR) , Legislation & Litigation Britain’s Global AI Summit to Focus...
Cybercrime Tremors: Experts Forecast Qakbot Resurgence – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cybercrime , Cybercrime as-a-service , Endpoint Security TrickBot and Emotet Botnets Both Returned After Disruption by Law Enforcement Mathew J. Schwartz...
Securing Linux Policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Linux is a powerful and customizable operating system that has been the backbone of many businesses for decades. This policy from TechRepublic...
Developers Warned of Malicious PyPI, NPM, Ruby Packages Targeting Macs – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Threat actors have started uploading malicious packages to PyPI, NPM, and RubyGems repositories in a new campaign aimed at stealing...
Cybersecurity M&A Roundup: 40 Deals Announced in August 2023 – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Forty cybersecurity-related merger and acquisition (M&A) deals were announced in August 2023. The number of transactions has bounced back in...
Ransomware Attack on Fencing Systems Maker Zaun Impacts UK Military Data – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire British mesh fencing systems maker Zaun has disclosed a LockBit ransomware attack that potentially led to the compromise of data...
More Schools Hit By Cyber-Attacks Before Term Begins – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A north London school and a Berkshire schools group have become the latest victims of serious cyber-attacks ahead of the new term, according...