Source: securityboulevard.com – Author: Rajan Sodhi Product Update: Version 4.0 As we enter the new era of 4.0, we are thrilled to introduce a range of...
Month: August 2023
Tourists Give Themselves Away by Looking Up. So Do Most Network Intruders. – Source: securityboulevard.com
Source: securityboulevard.com – Author: BrianKrebs In large metropolitan areas, tourists are often easy to spot because they’re far more inclined than locals to gaze upward at...
Securing Kubernetes in multi-cloud environments: challenges and best practices – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ben Hirschberg Kubernetes has become the de facto platform for orchestrating containerized applications at scale in today’s IT landscape. Its ability to...
Using JupyterLab to Manage Password Cracking Sessions (A CMIYC 2023 Writeup) Part 2 – Source: securityboulevard.com
Source: securityboulevard.com – Author: Matt Weir “Tools?” scoffed Kalisti, “Tools are for people who have nothing better to do than think things through and make sensible...
CVSS 4.0: How Will it Change Vulnerability Management? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Team Nuspire Security teams continue to rely on the Common Vulnerability Scoring System (CVSS) as a useful, standardized framework for assessing software...
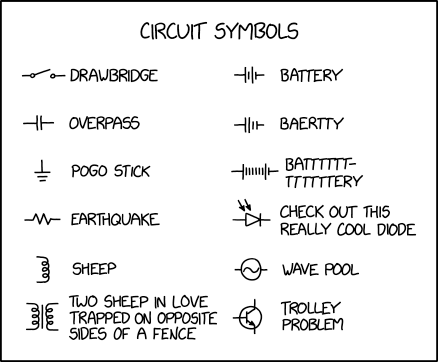
Randall Munroe’s XKCD ‘Circuit Symbols’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
Cuba Ransomware Exploits Veeam Vulnerability – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Ransomware The Attack Accesses an Exposed API on a Component of the Veeam Application Prajeet Nair...
Monti Ransomware Deploying New Linux Encryptor – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Ransomware More Ransomware Groups Targeting Linux Systems Akshaya Asokan (asokan_akshaya) • August 22, 2023 ...
BlackCat Ransomware Group Targets Japanese Watchmaker Seiko – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Governance & Risk Management , Operational Technology (OT) Seiko Hints at Data Breach But Declines to...
New Zero-Day Bug Affects All Versions of Ivanti Sentry – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Endpoint Security Zero-Day Can Be Exploited by Chaining It With Last Month’s Ivanti MobileIron Bugs Mihir Bagwe (MihirBagwe) • August 22,...
TP-Link Smart Bulb Vulnerabilities Expose Households to Hacker Attacks – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Four vulnerabilities identified by academic researchers from Italy and the UK in the TP-Link Tapo L530E smart bulb and its...
Hacker Conversations: Cris Thomas (AKA Space Rogue) From Lopht Heavy Industries – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Researchers are hackers. In the hat color terminology, there are Blackhat, Whitehat and various shades of Greyhat hackers. Today, the...
US Military Targeted in Recent HiatusRAT Attack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire A recent HiatusRAT campaign has been targeting a US military procurement system for reconnaissance, cybersecurity firm Lumen reports. Initially observed...
Ransomware Group Starts Leaking Data From Japanese Watchmaking Giant Seiko – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs A known ransomware group on Monday started publishing data allegedly stolen from the systems of Japanese watchmaking giant Seiko. Seiko...
Australian Energy Software Firm Energy One Hit by Cyberattack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Energy One, an Australian company that provides software products and services to the energy sector, has been hit by a...
New ‘Carderbee’ APT Targeted Chinese Security Software in Supply Chain Attack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire A newly discovered advanced persistent threat (APT) actor has been observed deploying the PlugX backdoor via a supply chain attack,...
Grip Security Lands $41 Million Series B Financing – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Israeli cloud data security startup Grip Security has banked $41 million in new financing from a group of investors led...
Cerby Raises $17 Million for Access Management Platform for Nonstandard Applications – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Access management startup Cerby today announced that it has raised $17 million in a Series A funding round that brings...
CISA Warns of Another Exploited Adobe ColdFusion Vulnerability – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The US Cybersecurity and Infrastructure Security Agency (CISA) is warning organizations that an Adobe ColdFusion vulnerability patched earlier this year...
Critical Insight Report: 15% Drop in Breaches, 31% Surge in Victims – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Cybersecurity-as-a-Service provider Critical Insight has unveiled its 2023 H1 Healthcare Data Breach Report, offering insights into the cybersecurity landscape of the...
Scarab Ransomware Deployed Worldwide Via Spacecolon Toolset – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Cybersecurity researchers from ESET have uncovered a malicious toolset named Spacecolon that has been deployed to spread variants of the Scarab...
US ARPA-H Initiative Counters Healthcare Cyber-Threats – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 In a bid to counter cyber-attacks targeting the US healthcare system, the Advanced Research Projects Agency for Health (ARPA-H), operating under...
Continued MOVEit Exploitation Drives Record Ransomware Attacks – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Ransomware attacks hit record levels in July 2023, driven by the Clop gang’s continued exploitation of the MOVEit vulnerability, according to...
Cyber-Attack on Australian Utility Firm Energy One Spreads to UK Systems – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A cyber-attack on Australian utility company, Energy One Limited (EOL), could have international impact with the firm’s corporate systems in the...
New APT Group Launches Supply Chain Campaign – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A newly discovered APT group has been spotted using commercial software to deploy backdoor malware to targeted victims in Hong Kong...
Ivanti Warns of Critical New Zero-Day Bug – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Security vendor Ivanti has urged customers to urgently remediate a newly discovered zero-day vulnerability in its Ivanti Sentry product. Formerly known...
Tesla: Insiders Responsible For Major Data Breach – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Tesla has confirmed a major data breach impacting nearly 76,000 employees and containing sensitive corporate information was carried out by two...
Tourists Give Themselves Away by Looking Up. So Do Most Network Intruders. – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs In large metropolitan areas, tourists are often easy to spot because they’re far more inclined than locals to gaze upward at...
Vulnerabilities in TP-Link IoT Devices Can Get You Hacked – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Andreea Chebac Four new vulnerabilities have been discovered in the TP-Link Tapo L530E smart bulb and TP-Link’s Tapo app. Researchers from Universita...
VMware Explore 2023: Keynote Highlights – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Megan Crouse Explore enterprise applications and infrastructure, AI, tools for the remote workforce, machine learning, and more from VMware Explore 2023. Image:...