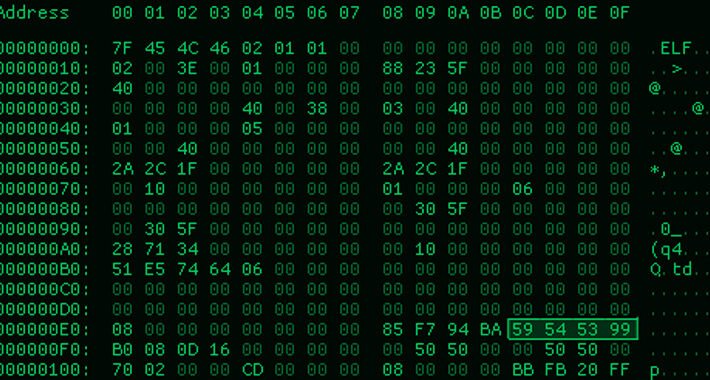
Source: thehackernews.com – Author: . Aug 30, 2023THNMalware / Endpoint Security New findings show that malicious actors could leverage a sneaky malware detection evasion technique and...
Day: August 30, 2023
MMRat Android Trojan Executes Remote Financial Fraud Through Accessibility Feature – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 30, 2023THNMobile Security / Malware A previously undocumented Android banking trojan dubbed MMRat has been observed targeting mobile users in...
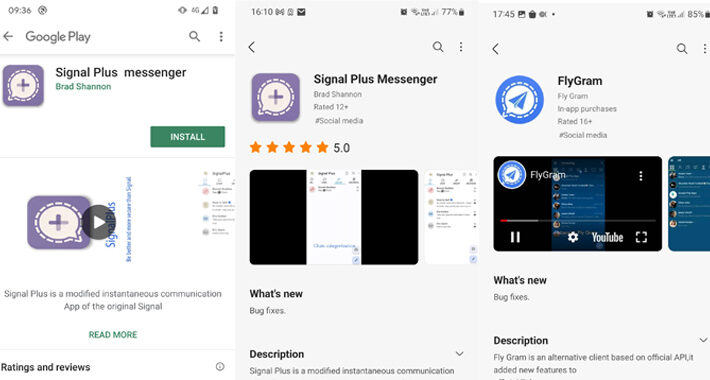
China-Linked BadBazaar Android Spyware Targeting Signal and Telegram Users – Source:thehackernews.com
Source: thehackernews.com – Author: . Cybersecurity researchers have discovered malicious Android apps for Signal and Telegram distributed via the Google Play Store and Samsung Galaxy Store...
How to Prevent ChatGPT From Stealing Your Content & Traffic – Source:thehackernews.com
Source: thehackernews.com – Author: . ChatGPT and similar large language models (LLMs) have added further complexity to the ever-growing online threat landscape. Cybercriminals no longer need...
Malicious npm Packages Aim to Target Developers for Source Code Theft – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 30, 2023THNSoftware Security / Malware An unknown threat actor is leveraging malicious npm packages to target developers with an aim...
Alert: Juniper Firewalls, Openfire, and Apache RocketMQ Under Attack from New Exploits – Source:thehackernews.com
Source: thehackernews.com – Author: . Recently disclosed security flaws impacting Juniper firewalls, Openfire, and Apache RocketMQ servers have come under active exploitation in the wild, according...
New Android Banking Trojan Targets Southeast Asia Region – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Fraud Management & Cybercrime , Social Engineering Android Banking Trojan Disguised As Dating or Government App Prajeet Nair (@prajeetspeaks) • August...
Live Webinar | Data Protection and its Modern Role in Cyber Recovery – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Data Loss Prevention (DLP) , Endpoint Security Presented by CommVault 60 minutes Sophisticated cyberthreats are challenging businesses...
Why Criminals Keep Reusing Leaked Ransomware Builders – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Fraud Management & Cybercrime , Ransomware Blame Police Crackdowns on Big Names, Hacker Thrift, Ransomware Grifters in Trouble Mathew J. Schwartz...
US Aids Costa Rican Post-Hack Push for Robust SOC, Secure 5G – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Fraud Management & Cybercrime , Security Operations , Security Operations Center (SOC) US Funds for Regional SOC, Use of Trusted 5G...
Midwest Hospital Group Experiencing Systemwide IT Outage – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Fraud Management & Cybercrime , Healthcare , Industry Specific Incident Comes as Several Other Regional Providers Recover From Recent Attacks Marianne...
Chinese Hackers Anticipated Barracuda ESG Patch – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 3rd Party Risk Management , Cybercrime , Cyberwarfare / Nation-State Attacks Threat Actor Deployed an Additional Backdoor to Select Targets David...
4 Strategies to Safeguard the Finance Industry Against Deepfake Onslaught – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kevin Kirkwood, Deputy CISO, LogRhythm With the rise of deepfake technology, the financial sector faces a new and growing threat landscape, as...
Performance-Enhanced Android MMRat Scurries onto Devices Via Fake App Stores – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading A newly detected Android Trojan with performance enhancements for transferring large amounts of data is infecting user...
Should Senior IT Professionals Be Accountable for Professional Decisions? – Source: www.darkreading.com
Source: www.darkreading.com – Author: James Watts, Managing Director, Databarracks In July, SolarWinds CISO Tim Brown and CFO Bart Kalsu received Securities and Exchange Commission notices of...
In Airbnb, Cybercriminals Find a Comfortable Home for Fraud – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Cybercriminals are always looking for that next hacking adventure, so it’s fitting that Airbnb has become an...
Somalia Orders ISPs to Block Telegram and TikTok – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dan Raywood, Senior Editor, Dark Reading The Somali government recently announced plans to shut down access to some social media platforms, including...
Rackspace Faces Massive Cleanup Costs After Ransomware Attack – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading After being hit with a ransomware attack at the end of 2022, Rackspace is now faced with...
Addressing Cybersecurity’s Talent Shortage & Its Impact on CISOs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Michael Scott, CISO, Immuta The cybersecurity sector continues to face a dire talent shortage as the threat landscape evolves, according to recent research...
Kroll’s Crypto Breach Highlights SIM-Swapping Risk – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading A recent supply chain breach at Kroll, the risk and financial advisory firm, affected downstream customers and...
Here’s What Your Breach Response Plan Might Be Missing – Source: www.darkreading.com
Source: www.darkreading.com – Author: Anthony Cusimano, Technical Director, Object First Armed with an outline of what to do in a data breach, companies might feel confident...
IT threat evolution in Q2 2023. Non-mobile statistics – Source: securelist.com
Source: securelist.com – Author: AMR IT threat evolution in Q2 2023 IT threat evolution in Q2 2023. Non-mobile statistics IT threat evolution in Q2 2023. Mobile...
IT threat evolution in Q2 2023. Mobile statistics – Source: securelist.com
Source: securelist.com – Author: Anton Kivva IT threat evolution in Q2 2023 IT threat evolution in Q2 2023. Non-mobile statistics IT threat evolution in Q2 2023....
IT threat evolution in Q2 2023 – Source: securelist.com
Source: securelist.com – Author: David Emm IT threat evolution in Q2 2023 IT threat evolution in Q2 2023. Non-mobile statistics IT threat evolution in Q2 2023....
‘Earth Estries’ Cyberespionage Group Targets Government, Tech Sectors – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs A cyberespionage group possibly linked to China has targeted government-related organizations and technology companies in various parts of the world....
Healthcare Organizations Hit by Cyberattacks Last Year Reported Big Impact, Costs – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Roughly 78% of the healthcare organizations in North America, South America, the APAC region, and Europe experienced a cyberattack over...
Recent Juniper Flaws Chained in Attacks Following PoC Exploit Publication – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Threat actors have started exploiting four recently patched vulnerabilities in the J-Web component of Juniper Networks’ Junos OS after proof-of-concept...
GitHub Enterprise Server Gets New Security Capabilities – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire GitHub on Tuesday announced the general availability of Enterprise Server 3.10 with new security capabilities, including support for custom deployment...
BGP Flaw Can Be Exploited for Prolonged Internet Outages – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs A serious flaw affecting several major Border Gateway Protocol (BGP) implementations can be exploited to cause prolonged internet outages, but...
How Quantum Computing Will Impact Cybersecurity – Source: www.securityweek.com
Source: www.securityweek.com – Author: Marie Hattar Quantum computers live in research universities, government offices, and leading scientific companies and, except in rare circumstances, find themselves out...