Source: www.databreachtoday.com – Author: 1 Cloud-Delivered Security Service Edge Solution Gives Efficient Hybrid Work Security Jeff Scheaffer, Vice President of Product Management (SSE, SASE and Security...
Day: August 17, 2023
AI in XDR: When Does It Make Sense? – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cisco’s AJ Shipley on When Generative AI Is Useful and When It’s Dangerous AJ Shipley, Vice President, Product – Threat Detection...
How Generative AI Will Improve Incident Response – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Generative AI will play a role in the future of incident response. It will be used in EDR tools and vulnerability...
RiskLens, Axio Lead Cyber Risk Quantification Forrester Wave – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , IT Risk Management , Risk Assessments ThreatConnect Earns High Marks as CRQ Helps CISOs Prove Return...
LIVE Webinar | Before & After AWS: Transforming Cloud’s Most Common Pitfalls into Progress – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Nate Kettlewell Principal, Application Security, Coalfire Nate Kettlewell is a specialist in information security, network engineering, and web application security. His...
Advocate Aurora to Settle Web Tracker Claims for $12.25M – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Healthcare , HIPAA/HITECH Attorneys to Get $4.3M and Class Reps to Get $3,500 Each Under Proposed...
Federal Judge Inclined To Grant Claims in Meta Pixel Case – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Privacy Tentative Order Issued in Consolidated Case Against Meta in Privacy Dispute Marianne Kolbasuk McGee (HealthInfoSec)...
The best AI security management (and the ultimate upgrades) – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: Artificial intelligence has transcended its status as a buzzword and has become a true catalyst for digital transformation. As...
Hacked electronic sign declares “Putin is a dickhead” as Russian ruble slumps – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley Someone clearly isn’t very impressed with Vladimir Putin, as the Russian economy continues to tank in the wake of sanctions....
LockBit’s dirty little secret: ransomware gang is failing to publish victims’ data – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley According to a fascinating report by Jon DiMaggio of Analyst1, who spent a year undercover gathering intelligence on the LockBit...
Clorox Operations Disrupted By Cyber-Attack – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Cleaning product manufacturer Clorox has confirmed significant operational disruption caused by a recent cyber-attack. According to a notice published on the company’s...
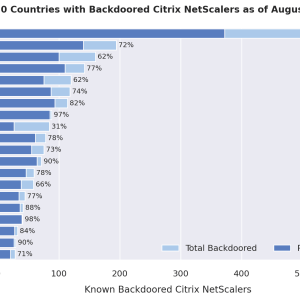
Mass-Exploitation Campaign Targets Citrix NetScalers With Backdoors – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A widespread cyber-attack targeting thousands of Citrix NetScalers has been unveiled by cybersecurity firm Fox-IT (part of NCC Group) in collaboration...
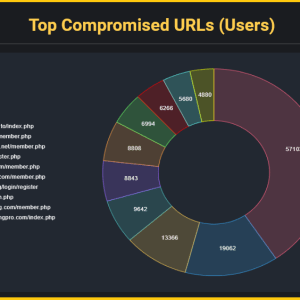
Scammers Exploit Hacked Websites For Phishing – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A recent study by cybersecurity firm Kaspersky has revealed the techniques utilized by phishers to evade detection and exploit compromised websites...
A Third of UK University Students Targeted By Fraud – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 One in three students at British universities encountered fraud attempts online last year, according to a new study from NatWest. The...
Major LinkedIn Account Takeover Campaign Underway – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Security researchers have warned of a significant global account takeover campaign targeting LinkedIn users over recent weeks. Cyberint claimed this week...
Digital Safety Advice is Not Getting Through to Women – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 New research from King’s College London (KCL) has revealed a major gender gap in the provision and effectiveness of online safety...
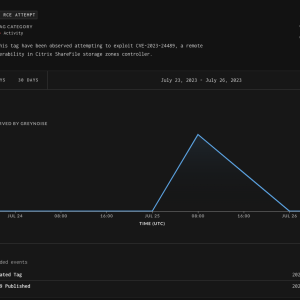
CISA adds flaw in Citrix ShareFile to its Known Exploited Vulnerabilities catalog – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini US CISA added critical vulnerability CVE-2023-24489 in Citrix ShareFile to its Known Exploited Vulnerabilities catalog. US Cybersecurity and Infrastructure Security...
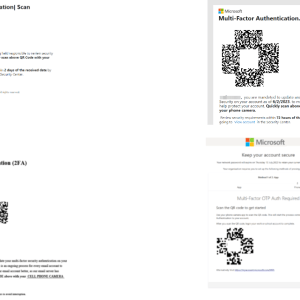
A massive phishing campaign using QR codes targets the energy sector – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A phishing campaign employing QR codes targeted a leading energy company in the US, cybersecurity firm Cofense reported. Starting from...
Two unauthenticated stack buffer overflows found in Ivanti Avalanche EMM – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Ivanti Avalanche EMM product is impacted by two buffer overflows collectively tracked as CVE-2023-32560. Tenable researchers discovered two stack-based buffer overflows,...
Approximately 2000 Citrix NetScaler servers were backdoored in a massive campaign – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A threat actor has compromised roughly 2,000 Citrix NetScaler servers exploiting a remote code execution tracked as CVE-2023-3519. In July...
Credentials for cybercrime forums found on roughly 120K computers infected with info stealers – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Researchers discovered credentials associated with cybercrime forums on roughly 120,000 computers infected with information stealers. Threat intelligence firm Hudson Rock...
MoustachedBouncer: Espionage against foreign diplomats in Belarus – Source:
Source: – Author: 1 Long-term espionage against diplomats, leveraging email-based C&C protocols, C++ modular backdoors, and adversary-in-the-middle (AitM) attacks… Sounds like the infamous Turla? Think again!...
Time is money, and online game scammers have lots of it – Source:
Source: – Author: 1 Gamers and cybersecurity professionals have something in common – the ever-terrible presence of hacking, scams, and data theft – but how and...
Check cybersecurity pre-invest – Week in security with Tony Anscombe – Source:
Source: – Author: 1 When you invest in a company, do you check its cybersecurity? The U.S. Securities and Exchange Commission has adopted new cybersecurity rules....
Fingerprints all over: Can browser fingerprinting increase website security? – Source:
Source: – Author: 1 Browser fingerprinting is supposedly a more privacy-conscious tracking method, replacing personal information with more general data. But is it a valid promise?...
The grand theft of Jake Moore’s voice: The concept of a virtual kidnap – Source:
Source: – Author: 1 With powerful AI, it doesn’t take much to fake a person virtually, and while there are some limitations, voice-cloning can have some...
Quantum computing: Will it break crypto security within a few years? – Source:
Source: – Author: 1 Current cryptographic security methods watch out – quantum computing is coming for your lunch. Original Post URL: Category & Tags: – Views:...
Is backdoor access oppressive? – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Bills granting access to end-to-end encrypted systems, opportunity for cybercriminals, abuse by authority, human rights, and tech companies leaving the UK? Original...
Gathering dust and data: How robotic vacuums can spy on you – Source:
Source: – Author: 1 Mitigate the risk of data leaks with a careful review of the product and the proper settings. Original Post URL: Category &...
Dear all, What are some common subject lines in phishing emails? – Source:
Source: – Author: 1 Scammers exploit current ongoing events, account notifications, corporate communication, and a sense of urgency. Original Post URL: Category & Tags: – Views:...