Source: – Author: 1 Browser fingerprinting is supposedly a more privacy-conscious tracking method, replacing personal information with more general data. But is it a valid promise?...
Day: August 14, 2023
The grand theft of Jake Moore’s voice: The concept of a virtual kidnap – Source:
Source: – Author: 1 With powerful AI, it doesn’t take much to fake a person virtually, and while there are some limitations, voice-cloning can have some...
Quantum computing: Will it break crypto security within a few years? – Source:
Source: – Author: 1 Current cryptographic security methods watch out – quantum computing is coming for your lunch. Original Post URL: Category & Tags: – Views:...
Is backdoor access oppressive? – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Bills granting access to end-to-end encrypted systems, opportunity for cybercriminals, abuse by authority, human rights, and tech companies leaving the UK? Original...
Gathering dust and data: How robotic vacuums can spy on you – Source:
Source: – Author: 1 Mitigate the risk of data leaks with a careful review of the product and the proper settings. Original Post URL: Category &...
Dear all, What are some common subject lines in phishing emails? – Source:
Source: – Author: 1 Scammers exploit current ongoing events, account notifications, corporate communication, and a sense of urgency. Original Post URL: Category & Tags: – Views:...
What happens if AI is wrong? – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Responses generated by ChatGPT about individual people could be misleading or harmful or spill their personal information. What are the takeaways for...
8 common work-from-home scams to avoid – Source:
Source: – Author: 1 That ‘employer’ you’re speaking to may in reality be after your personal information, your money or your help with their illegal activities...
Child identity theft: how do I keep my kids’ personal data safe? – Source:
Source: – Author: 1 Why is kids’ personal information in high demand, how do criminals steal it, and what can parents do to help prevent child...
Protect yourself from ticketing scams ahead of the Premier League Summer Series USA Tour – Source:
Source: – Author: 1 There is a significant secondary marketplace where tickets can sell for several times their original value, opening the opportunity for scammers and...
Key findings from ESET Threat Report H1 2023 – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Here’s how cybercriminals have adjusted their tactics in response to Microsoft’s stricter security policies, plus other interesting findings from ESET’s new Threat...
The danger within: 5 steps you can take to combat insider threats – Source:
Source: – Author: 1 Some threats may be closer than you think. Are security risks that originate from your own trusted employees on your radar? Original...
Phishing with hacked sites – Source: securelist.com
Source: securelist.com – Author: Tatyana Machneva, Olga Svistunova Phishers want their fake pages to cost minimum effort but generate as much income as possible, so they...
Fake Tripadvisor Emails to Distribute Knight Ransomware – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Andreea Chebac An ongoing spam campaign spreads Knight ransomware among users. The fake emails imitate Tripadvisor complaint messages. Knight ransomware is the...
India Passes New Digital Personal Data Protection Bill (DPDPB), Putting Users’ Privacy First – Source:thehackernews.com
Source: thehackernews.com – Author: . The Indian President Droupadi Murmu on Friday granted assent to the Digital Personal Data Protection Bill (DPDPB) after it was unanimously...
Don’t Expect Quick Fixes in ‘Red-Teaming’ of AI Models. Security Was an Afterthought – Source: www.securityweek.com
Source: www.securityweek.com – Author: Associated Press White House officials concerned by AI chatbots’ potential for societal harm and the Silicon Valley powerhouses rushing them to market...
Microsoft: Critical CODESYS Flaws Could Shut Down Power Plants – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Microsoft researchers have identified multiple high-severity vulnerabilities that could enable threat actors to shut down power plants. The flaws were discovered...
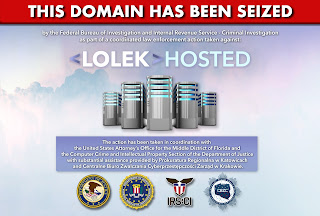
Authorities Take Down Lolek Bulletproof Hosting Provider – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Police have taken down a Lolek bulletproof hosting service used by criminals to launch cyber-attacks across the world. The takedown was...
BSides Leeds 2023 – Gerald Benischke – Precision Munitions For Denial Of Service – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
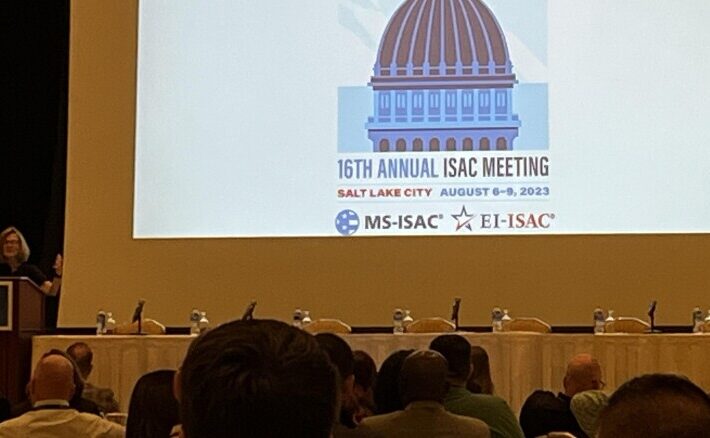
Highlights from the 16th Annual MS-ISAC Meeting – Source: securityboulevard.com
Source: securityboulevard.com – Author: Lohrmann on Cybersecurity The 2023 MS-ISAC and EI-ISAC meeting just wrapped up in Salt Lake City. Here’s a roundup of what happened...
A Compilation of Bulletproof Hosting Provider Domains – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dancho Danchev In need of a fresh and relevant bulletproof hosting provider domain list for research purposes? Check out the following list...