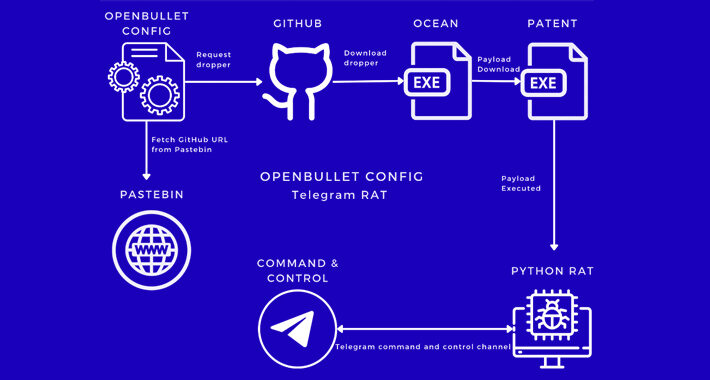
Source: thehackernews.com – Author: . Aug 07, 2023THNCyber Crime / Malware A new malware campaign has been observed making use of malicious OpenBullet configuration files to...
Day: August 7, 2023
North Korean Hackers Targets Russian Missile Engineering Firm – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 07, 2023THNCyber Attack Two different North Korean nation-state actors have been linked to a cyber intrusion against the major Russian...
Welcome to the New Have I Been Pwned Domain Search Subscription Service – Source: www.troyhunt.com
Source: www.troyhunt.com – Author: Troy Hunt This is a big one. A massive one. It’s the culmination of a solid 7 months of work that finally,...
Spanish Police Arrest 3 Behind Payment Card Fraud – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Card Not Present Fraud , Cybercrime , Fraud Management & Cybercrime Cybercrime Group Defrauded Nearly 200,000 Euros Akshaya Asokan (asokan_akshaya) •...
Colorado Warns Ransomware Attack Caused Massive Data Breach – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Breach Notification , Security Operations Information From 2004 to 2020 Exposed for High School Students, Teachers and Others Mathew J. Schwartz...
White House Pushes Cybersecurity Defense for K-12 Schools – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Endpoint Security , Fraud Management & Cybercrime , Government Educators Gird for Fresh Ransomware Attacks as Students Set to Return to...
New PaperCut Vulnerability Allows Remote Code Execution – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Organizations have been warned about a new potentially serious vulnerability affecting the PaperCut NG/MF print management software. The flaw, tracked...
CISA Unveils Cybersecurity Strategic Plan for Next 3 Years – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The US Cybersecurity and Infrastructure Security Agency (CISA) has unveiled its Cybersecurity Strategic Plan for the next three years, focusing...
Colorado Department of Higher Education Discloses Ransomware Attack, Data Breach – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The Colorado Department of Higher Education (CDHE) has been targeted in a ransomware attack that resulted in a data breach...
US Primary Care Services Shuttered After Cyber-Attack – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A widespread cyber-attack on hospital computer systems has caused significant disruptions across the United States, leading to the closure of emergency...
Invisible Ad Fraud Targets Korean Android Users – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Cybersecurity experts have discovered a new adware campaign specifically targeting Korean Android users. The discovery by McAfee’s Mobile Research Team shed...
FBI Warns Against Criminals Posing as NFT Developers – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The US Federal Bureau of Investigation (FBI) has issued a warning concerning a growing wave of financial fraud within the Non-Fungible...
GUEST ESSAY: Why any sudden influx of spam emails is an indicator of a likely security issue – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Zac Amos We all get spam emails, and while it’s annoying, it’s not usually anything to worry about. However, getting...
Black Hat Fireside Chat: Horizon3.ai makes a strong case for continuous, self-service pentesting – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Byron V. Acohido LAS VEGAS — Penetration testing, traditionally, gave businesses a nice, pretty picture of their network security posture...
Russian Hacktivists Overwhelm Spanish Sites With DDoS – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A leading Spanish research institute has become the latest organization in the country to come under cyber-attack from Russia, after a...
Colorado Education Department Suffers Ransomware Breach – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Former and current high school staff and students in Colorado have been put on notice that their personal information may have...
Clop Gang Offers Data Downloads Via Torrents – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The Clop ransomware group has begun offering access to data stolen in MOVEit attacks via torrents, it has emerged. Security researcher...
FBI warns of crooks posing as NFT developers in fraudulent schema – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The FBI is warning about cyber criminals masquerading as NFT developers to steal cryptocurrency and other digital assets. The U.S....
The number of ransomware attacks targeting Finland increased fourfold since it started the process to join NATO – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Senior official reports a quadruple increase in ransomware attacks against Finland since it started the process to join NATO. The...
Microsoft fixed a flaw in Power Platform after being criticized – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Microsoft announced it has addressed a critical flaw in its Power Platform after it was criticized for the delay in fixing...
Colorado Department of Higher Education (CDHE) discloses data breach after ransomware attack – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini The Colorado Department of Higher Education (CDHE) finally disclosed a data breach impacting students, past students, and teachers after the...
The Dark Web Is Expanding (As Is the Value of Monitoring It) – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 Many security professionals today associate the Dark Web with named leaks, which are leaked credentials from employee password reuse. This is...
Enhancing Security Operations Using Wazuh: Open Source XDR and SIEM – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 07, 2023The Hacker NewsSIEM and XDR Platform In today’s interconnected world, evolving security solutions to meet growing demand is more...
New ‘Deep Learning Attack’ Deciphers Laptop Keystrokes with 95% Accuracy – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 07, 2023THNDeep Learning / Endpoint Security A group of academics has devised a “deep learning-based acoustic side-channel attack” that can...
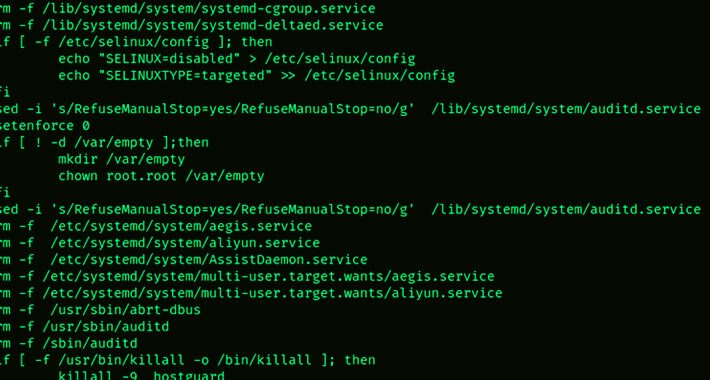
New SkidMap Redis Malware Variant Targeting Vulnerable Redis Servers – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 07, 2023THNData Security / Linux Vulnerable Redis services have been targeted by a “new, improved, dangerous” variant of a malware...
FBI Alert: Crypto Scammers are Masquerading as NFT Developers – Source:thehackernews.com
Source: thehackernews.com – Author: . Aug 07, 2023THNCyber Crime / Cryptocurrency The U.S. Federal Bureau of Investigation (FBI) is warning about cyber crooks masquerading as legitimate...
Check cybersecurity pre-invest – Week in security with Tony Anscombe – Source:
Source: – Author: 1 When you invest in a company, do you check its cybersecurity? The U.S. Securities and Exchange Commission has adopted new cybersecurity rules....
Fingerprints all over: Can browser fingerprinting increase website security? – Source:
Source: – Author: 1 Browser fingerprinting is supposedly a more privacy-conscious tracking method, replacing personal information with more general data. But is it a valid promise?...
The grand theft of Jake Moore’s voice: The concept of a virtual kidnap – Source:
Source: – Author: 1 With powerful AI, it doesn’t take much to fake a person virtually, and while there are some limitations, voice-cloning can have some...
Quantum computing: Will it break crypto security within a few years? – Source:
Source: – Author: 1 Current cryptographic security methods watch out – quantum computing is coming for your lunch. Original Post URL: Category & Tags: – Views:...