Source: securityboulevard.com – Author: RiskLens Powerful combination of SAFE Platform’s industry defining AI capabilities coupled with the industry standard FAIR model for cyber risk quantification, that...
Month: July 2023
Concerns About Infostealer Malware on the Rise – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard A survey of 320 IT security professionals in the U.S. and the United Kingdom found more than half (53%) are...
Cybersecurity Needs to Mitigate Complexity – Source: securityboulevard.com
Source: securityboulevard.com – Author: Steve Winterfeld Bruce Schneier’s quote, “Complexity is the enemy of security,” is one of my favorite sayings. It sums up one of...
Have You Been Pwned? – What is it and how to prevent it – Source: securityboulevard.com
Source: securityboulevard.com – Author: Ahona Rudra Email addressed can be compromised to initiate major data breaches that can lead to the loss of your assets and...
What we told the CFTC about crypto threats – Source: securityboulevard.com
Source: securityboulevard.com – Author: Trail of Bits Dan Guido, CEO In March, I joined the Commodity Futures Trading Commission’s Technology Advisory Committee (TAC), helping the regulatory...
CycloneDX 1.5: The next big step for SBOMs and software transparency – Source: securityboulevard.com
Source: securityboulevard.com – Author: John P. Mello Jr. CycloneDX is one of the most popular standards for describing the components of an application, including source code,...
Hardcoded Accounts Allow Full Takeover of Technicolor Routers – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Multiple hardcoded credentials found on the Technicolor TG670 DSL gateway router allow attackers to completely take over devices, the CERT...
Inside the Mind of the Hacker: Report Shows Speed and Efficiency of Hackers in Adopting New Technologies – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend The application of artificial intelligence is still in its infancy, but we are already seeing one major effect: the democratization...
Chinese Cyberspies Used Forged Authentication Tokens to Hack Government Emails – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs Microsoft reported on Tuesday that a Chinese cyberespionage group it tracks as Storm-0558 was recently spotted using forged authentication tokens...
CISO Conversations: CISOs of Identity Giants IDEMIA and Ping – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend SecurityWeek talks to Dennis Kallelis (CSO at Idemia) and Jason Kees (CISO at Ping), two of industry’s identity giants. The...
Citrix Patches Critical Vulnerability in Secure Access Client for Ubuntu – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Citrix on Tuesday announced the release of patches for a critical-severity vulnerability in the Secure Access client for Ubuntu that...
Fortinet Patches Critical FortiOS Vulnerability Leading to Remote Code Execution – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Fortinet on Tuesday announced security updates that address a critical-severity vulnerability in FortiOS and FortiProxy that could be exploited for...
Microsoft Revokes Many Signed Drivers Used by Chinese Cybercriminals – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs After being notified by several security firms, Microsoft has revoked many signed drivers that had been leveraged by threat actors,...
MOVEit: Testing the Limits of Supply Chain Security – Source: www.securityweek.com
Source: www.securityweek.com – Author: Torsten George Since late last month, a Russian cyber-extortion gang has been exploiting a flaw in a widely used software known as...
SAP Patches Critical Vulnerability in ECC and S/4HANA Products – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire German enterprise software maker SAP on Tuesday announced the release of 16 new security notes as part of its July...
Former Security Engineer Arrested for $9 Million Crypto Exchange Hack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The US today announced the arrest of Shakeeb Ahmed on charges related to the defrauding of a decentralized cryptocurrency exchange...
Fortinet warns of critical RCE flaw in FortiOS, FortiProxy devices – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Fortinet has disclosed a critical severity flaw impacting FortiOS and FortiProxy, allowing a remote attacker to perform arbitrary code execution...
Ransomware payments on record-breaking trajectory for 2023 – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Image: Bing Create Data from the first half of the year indicates that ransomware activity is on track to break...
Microsoft: Chinese hackers breached US govt Exchange email accounts – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan A Chinese hacking group has breached the email accounts of more than two dozen organizations worldwide, including U.S. and Western...
What’s new in the Windows 11 22H2 Moment 3 update, now available – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Mayank Parmar Microsoft has begun the forced rollout of its Windows 11 22H2 ‘Moment 3’ update, which introduces several new features and...
Apple & Microsoft Patch Tuesday, July 2023 Edition – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs Microsoft Corp. today released software updates to quash 130 security bugs in its Windows operating systems and related software, including at...
Clop Crime Group Adds 62 Ernst & Young Clients to Leak Sites – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 3rd Party Risk Management , Fraud Management & Cybercrime , Governance & Risk Management Victims Include Airline, Banks, Hospitals, Retailers in...
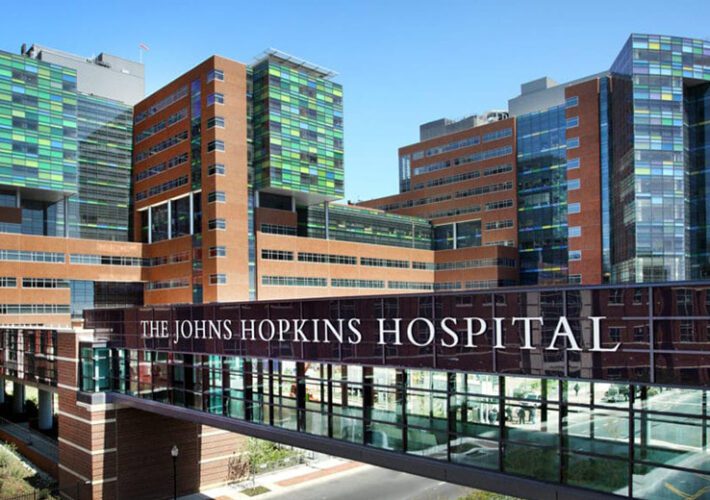
Lawsuits Filed Against Johns Hopkins in MOVEit Hack Mess – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Governance & Risk Management , Privacy University, Healthcare System Facing Proposed Class Actions Suits for Data...
Custom Trojan Attacking Latin American Organizations – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Social Engineering Toitoin Trojan Campaign Uses Six-Staged Infection Chain to Steal Data Prajeet Nair...
Web-Browsing Glitch Prompts Apple to Withdraw Zero-Day Fix – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Governance & Risk Management , Patch Management , Vulnerability Assessment & Penetration Testing (VA/PT) The Latest Rapid Security Response Might Prevent...
The Risks and Preventions of AI in Business: Safeguarding Against Potential Pitfalls – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 12, 2023The Hacker NewsDNS Filtering / Network Security Artificial intelligence (AI) holds immense potential for optimizing internal processes within businesses....
Microsoft Thwarts Chinese Cyber Attack Targeting Western European Governments – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 12, 2023THNThreat Intel / Cyber Espionage Microsoft on Tuesday revealed that it repelled a cyber attack staged by a Chinese...
Chinese Hackers Deploy Microsoft-Signed Rootkit to Target Gaming Sector – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 12, 2023THNCyber Threat / Gaming Cybersecurity researchers have unearthed a novel rootkit signed by Microsoft that’s engineered to communicate with...
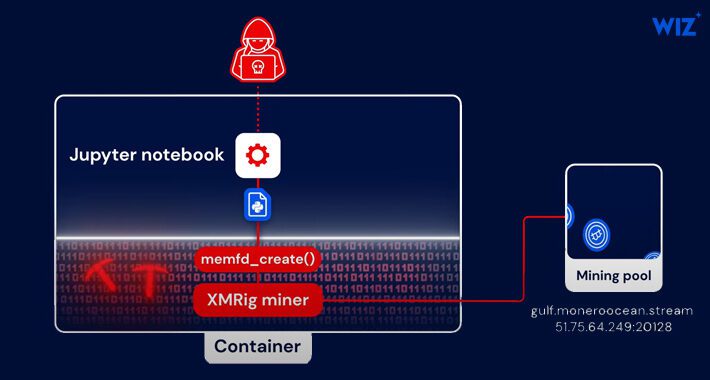
Python-Based PyLoose Fileless Attack Targets Cloud Workloads for Cryptocurrency Mining – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 12, 2023The Hacker NewsCloud Security / Cryptocurrency A new fileless attack dubbed PyLoose has been observed striking cloud workloads with...
Microsoft Releases Patches for 132 Vulnerabilities, Including 6 Under Active Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 12, 2023The Hacker NewsVulnerability / Software Security Microsoft on Tuesday released updates to address a total of 132 new security...