Source: – Author: 1 In a rush to file your taxes? Watch out for cybercriminals preying on stressed taxpayers as Tax Day looms large on the...
Day: July 27, 2023
Decoy Dog: New Breed of Malware Posing Serious Threats to Enterprise Networks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 26, 2023THNMalware / Cyber Threat A deeper analysis of a recently discovered malware called Decoy Dog has revealed that it’s...
The Alarming Rise of Infostealers: How to Detect this Silent Threat – Source:thehackernews.com
Source: thehackernews.com – Author: . A new study conducted by Uptycs has uncovered a stark increase in the distribution of information stealing (a.k.a. infostealer or stealer)...
Fenix Cybercrime Group Poses as Tax Authorities to Target Latin American Users – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 26, 2023THNOnline Security / Malware Tax-paying individuals in Mexico and Chile have been targeted by a Mexico-based cybercrime group that...
New AI Tool ‘FraudGPT’ Emerges, Tailored for Sophisticated Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 26, 2023THNCyber Crime / Artificial Intelligence Following the footsteps of WormGPT, threat actors are advertising yet another cybercrime generative artificial...
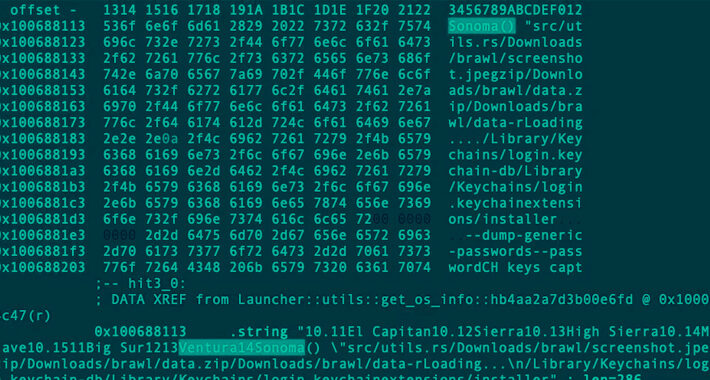
Rust-based Realst Infostealer Targeting Apple macOS Users’ Cryptocurrency Wallets – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 26, 2023THNCryptocurrency / Endpoint Security A new malware family called Realst has become the latest to target Apple macOS systems,...
Critical MikroTik RouterOS Vulnerability Exposes Over Half a Million Devices to Hacking – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 26, 2023THNNetwork Security / Vulnerability A severe privilege escalation issue impacting MikroTik RouterOS could be weaponized by remote malicious actors...
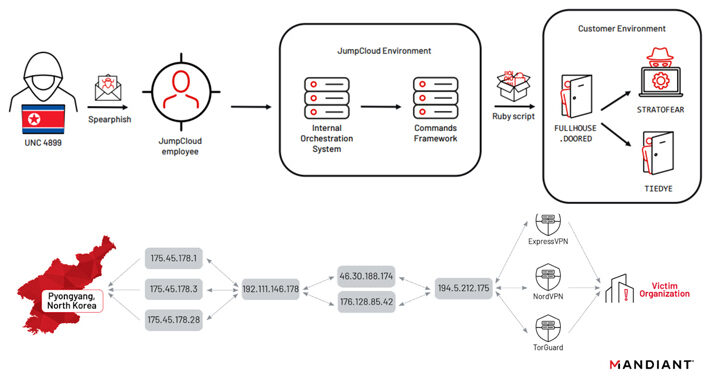
North Korean Nation-State Actors Exposed in JumpCloud Hack After OPSEC Blunder – Source:thehackernews.com
Source: thehackernews.com – Author: . North Korean nation-state actors affiliated with the Reconnaissance General Bureau (RGB) have been attributed to the JumpCloud hack following an operational...