Source: www.techrepublic.com – Author: Lance Whitney Image: nicescene/Adobe Stock 2022 marked another year in which ransomware proved to be one of the most pernicious cyberthreats around...
Day: July 27, 2023
Get 8 Months of Live Cyber Security Training for Under $500 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: TechRepublic Academy on July 25, 2023, 1:33 PM EDT Get 8 Months of Live Cyber Security Training for Under $500 If you’re...
Checklist: Securing Digital Information – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Digital information is generally the lifeblood of any given organization, containing essential company data needed to run the business. Paperless offices have...
BreachForums database and private chats for sale in hacker data breach – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams While consumers are usually the ones worried about their information being exposed in data breaches, it’s now the hacker’s turn,...
Zimbra patches zero-day vulnerability exploited in XSS attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Two weeks after the initial disclosure, Zimbra has released security updates that patch a zero-day vulnerability exploited in attacks targeting...
SSNDOB cybercrime market admin faces 15 years after pleading guilty – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A Ukrainian man, Vitalii Chychasov, has pleaded guilty in the United States to conspiracy to commit access device fraud and...
WordPress Ninja Forms plugin flaw lets hackers steal submitted data – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Popular WordPress form-building plugin Ninja Forms contains three vulnerabilities that could allow attackers to achieve privilege escalation and steal user...
8 million people hit by data breach at US govt contractor Maximus – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas U.S. government services contractor Maximus has disclosed a data breach warning that hackers stole the personal data of 8 to...
Swiss visa appointments cancelled in UK due to ‘IT incident’ – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ax Sharma All appointments for Swiss (Schengen) tourist and transit visas have been cancelled across the UK. TLScontact, the Swiss government’s chosen IT...
Cyberattack Investigation Shuts Down Ambulance Patient Records System – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Madalina Popovici A cyber attack on health software company Ortivus has led to the shutdown of the ambulance patient records system, affecting...
TSA Updates Pipeline Cybersecurity Requirements – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading A year after the Transportation Security Administration (TSA) updated requirements for pipeline owners and operators to improve their defenses...
Group-IB Co-Founder Sentenced to 14 Years in Russian Penal Colony – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Ilya Sachkov, co-founder and former CEO of Group-IB, a computer software company and cybersecurity firm that specializes...
Israeli-Trained Azerbaijan Cyber Students Mark Inaugural Graduation – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The first class from the Azerbaijan Cyber Security Center has graduated. Trained by Israeli staff from the...
What Will CISA’s Secure Software Development Attestation Form Mean? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Curtis Yanko, Principal Solutions Architect, GrammaTech When the White House issued the Cybersecurity Executive Order for National Cybersecurity in May 2021, observers...
Ubuntu Linux Cloud Workloads Face Rampant Root Take Takeovers – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Two vulnerabilities in the Ubuntu implementation of a popular container-based file system allow attackers to execute code...
Why Today’s CISOs Must Embrace Change – Source: www.darkreading.com
Source: www.darkreading.com – Author: Chip Stewart, Former CISO for the State of Maryland After recently serving as the chief information security officer (CISO) for the state...
Kyndryl Expands Managed Security Services With More SOC Options – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jeffrey Schwartz, Contributing Writer, Dark Reading Kyndryl, the managed IT services business that spun out of IBM nearly two years ago, announced...
Kubernetes and the Software Supply Chain – Source: www.darkreading.com
Source: www.darkreading.com – Author: Kirsten Newcomer, Director, Cloud and DevSecOps Strategy, Red Hat The ability of organizations to gain value from Kubernetes — and, more broadly,...
Threat Intelligence Is Growing — Here’s How SOCs Can Keep Up – Source: www.darkreading.com
Source: www.darkreading.com – Author: Microsoft Security, Microsoft Timely, comprehensive threat intelligence is a significant component of any good cybersecurity strategy. It helps organizations understand what their...
Thales Agrees to Buy App Security Vendor Imperva in $3.6B Deal – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading French multinational company Thales will acquire cybersecurity firm Imperva from Thoma Bravo for $3.6 billion, giving...
APT trends report Q2 2023 – Source: securelist.com
Source: securelist.com – Author: GReAT For more than six years, the Global Research and Analysis Team (GReAT) at Kaspersky has been publishing quarterly summaries of advanced...
The 4 Keys to Building Cloud Security Programs That Can Actually Shift Left – Source:thehackernews.com
Source: thehackernews.com – Author: . As cloud applications are built, tested and updated, they wind their way through an ever-complex series of different tools and teams....
Hackers Target Apache Tomcat Servers for Mirai Botnet and Crypto Mining – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 27, 2023THNServer Security / Cryptocurrency Misconfigured and poorly secured Apache Tomcat servers are being targeted as part of a new...
Group-IB Co-Founder Sentenced to 14 Years in Russian Prison for Alleged High Treason – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 27, 2023THNCybersecurity / Infosec A city court in Moscow on Wednesday convicted Group-IB co-founder and CEO Ilya Sachkov of “high...
New SEC Rules Require U.S. Companies to Reveal Cyber Attacks Within 4 Days – Source:thehackernews.com
Source: thehackernews.com – Author: . The U.S. Securities and Exchange Commission (SEC) on Wednesday approved new rules that require publicly traded companies to publicize details of...
ChatGPT’s Web3 Bug Reports Are ‘Nonsensical,’ Immunefi Says – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Artificial Intelligence & Machine Learning , Next-Generation Technologies & Secure Development The Generative AI Tool Can Write Bug Reports – Just...
Why CrowdStrike Is Eyeing Cyber Vendor Bionic at Up to $300M – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Application Security , Cloud Security , Next-Generation Technologies & Secure Development Bionic Is in Line for a 9-Figure Deal Just 31...
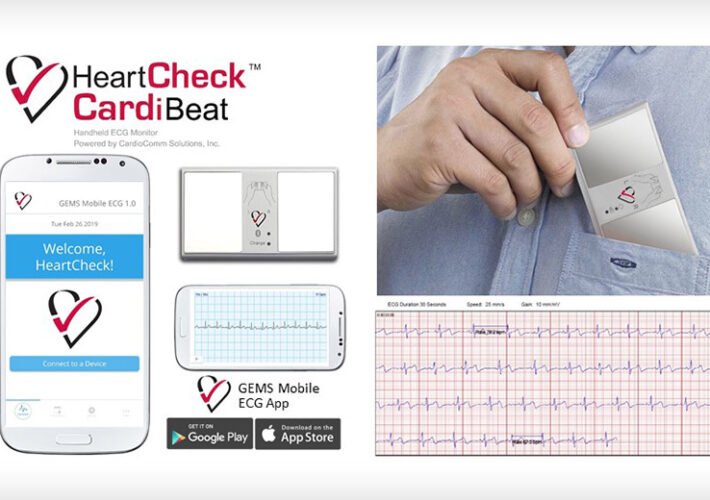
Cardiac Monitoring Software Firm Hit With Cyberattack – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Fraud Management & Cybercrime , Healthcare , Industry Specific CardioComm Says Business Operations Will Be Affected for Days or ‘Longer’ Marianne...
OnDemand | Graduating into a New Era: Cloud Security’s Biggest Challenges – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
Live Webinar | A Proactive Approach to Incident Response for OT – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Paul Shaver Global Practice Leader, Mandiant Mr. Shaver is the Global Practice Leader for Mandiant’s Industrial Control Systems/Operational Technology Security Consulting...