Source: thehackernews.com – Author: . Jul 24, 2023THNMobile Security / Privacy Google has announced that it intends to add support for Message Layer Security (MLS) to...
Day: July 24, 2023
How to Protect Patients and Their Privacy in Your SaaS Apps – Source:thehackernews.com
Source: thehackernews.com – Author: . The healthcare industry is under a constant barrage of cyberattacks. It has traditionally been one of the most frequently targeted industries,...
New OpenSSH Vulnerability Exposes Linux Systems to Remote Command Injection – Source:thehackernews.com
Source: thehackernews.com – Author: . Jul 24, 2023THNLinux / Network Security Details have emerged about a now-patched flaw in OpenSSH that could be potentially exploited to...
Banking Sector Targeted in Open-Source Software Supply Chain Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Cybersecurity researchers said they have discovered what they say is the first open-source software supply chain attacks specifically targeting the banking...
What happens if AI is wrong? – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Responses generated by ChatGPT about individual people could be misleading or harmful or spill their personal information. What are the takeaways for...
Avoiding data backup failures – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Today is World Backup Day, but maybe we also need a “did you test your backups” day? Original Post URL: Category &...
Banking turmoil opens opportunities for fraud – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Scammers are looking to cash in on the chaos that has set in following the startling meltdowns of Silicon Valley Bank and...
Twitter ends free SMS 2FA: Here’s how you can protect your account now – Source:
Source: – Author: 1 Twitter’s ditching of free text-message authentication doesn’t mean that you should forgo using 2FA. Instead, switch to another – and, indeed, better...
Understanding Managed Detection and Response – and what to look for in an MDR solution – Source:
Source: – Author: 1 Why your organization should consider an MDR solution and five key things to look for in a service offering Original Post URL:...
What TikTok knows about you – and what you should know about TikTok – Source:
Source: – Author: 1 As TikTok CEO attempts to placate U.S. lawmakers, it’s time for us all to think about the wealth of personal information that...
Highlights from TikTok CEO’s Congress grilling – Week in security with Tony Anscombe – Source:
Source: – Author: 1 Here are some of the key moments from the five hours of Shou Zi Chew’s testimony and other interesting news on the...
Staying safe on OnlyFans: The naked truth – Source:
Source: – Author: 1 How content creators and subscribers can embrace the social media platform without (overly) exposing themselves to the potentially toxic brew of NSFW...
Pig butchering scams: The anatomy of a fast-growing threat – Source:
Source: – Author: 1 How fraudsters groom their marks and move in for the kill using tricks from the playbooks of romance and investment scammers Original...
ESET Research Podcast: A year of fighting rockets, soldiers, and wipers in Ukraine – Source:
Source: – Author: 1 ESET experts share their insights on the cyber-elements of the first year of the war in Ukraine and how a growing number...
World Backup Day: Avoiding a data disaster is a forever topic – Source:
Source: – Author: 1 By failing to prepare you are preparing to fail. Make sure you’re able to bounce back if, or when, a data disaster...
Spring into action and tidy up your digital life like a pro – Source:
Source: – Author: 1 Spring is in the air and as the leaves start growing again, why not breathe some new life into the devices you...
Not-so-private messaging: Trojanized WhatsApp and Telegram apps go after cryptocurrency wallets – Source:
Source: – Author: 1 ESET researchers analyzed Android and Windows clippers that can tamper with instant messages and use OCR to steal cryptocurrency funds Original Post...
Why you should spring clean your home network and audit your backups – Source:
Source: – Author: 1 Do you know how many devices are connected to your home network? You don’t? This is precisely why it’s time for a...
Cleaning up your social media and passwords: What to trash and what to treasure – Source:
Source: – Author: 1 Give your social media presence a good spring scrubbing, audit your passwords and other easy ways to bring order to your digital...
How to Put the Sec in DevSecOps – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 In today’s interconnected digital landscape, cyberattacks have become a constant threat to businesses of all sizes. Companies that neglect cybersecurity measures...
What C-Suite Leaders Need to Know About XDR – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 Extended detection and response (XDR) was coined by Nir Zuk at Palo Alto Networks in 2018 to address challenges in siloed...
Black Hat Announces Sustainability Pledge – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 SAN FRANCISCO, July 13, 2023 — Black Hat, the producer of the cybersecurity industry’s most established and in-depth security events, today announced the...
Secure Code Warrior Ushers in Next Era in Developer Driven Security With $50M Series C Funding Round – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 Boston, London, Sydney – July 13, 2023 — Secure Code Warrior, the leading agile learning platform for developer-driven security leaders, today announced...
Introducing EncryptionSafe: A Free and Easy-to-Use Encryption App for Windows PC – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 ALEXANDRIA, Va., July 13, 2023 /PRNewswire/ — SmartPC Tools, a leading provider of innovative software solutions, released EncryptionSafe, a free, easy to use encryption application...
Facebook and Microsoft are the Most Impersonated Brands in Phishing Attacks – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 SAN FRANCISCO, July 13, 2023 /PRNewswire/ — Vade, a global cybersecurity company that secures human collaboration with a combination of AI and human-powered detection...
Safe Security Acquires RiskLens – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 Safe Security, the AI-Driven Cyber Risk Management company, has acquired RiskLens, the pioneer of the Cyber Risk Quantification standard – FAIR....
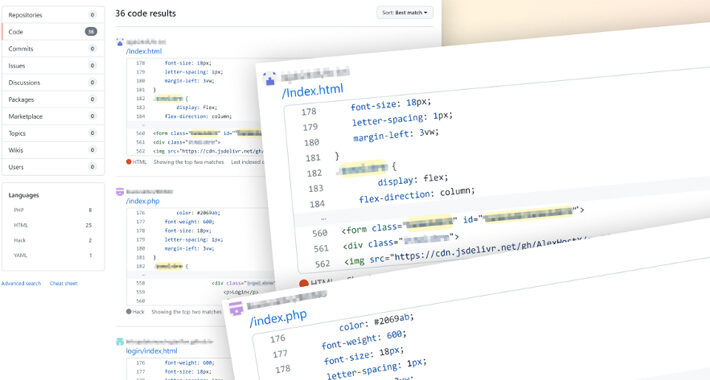
Linux Hacker Exploits Researchers With Fake PoCs Posted to GitHub – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading A GitHub user managed to dupe security researchers by publishing fake proofs-of-concept (PoCs) containing Linux backdoors....
Cybersecurity Leaders Report Reduction in Disruptive Cyber Incidents With MSS/MDR Solutions – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 DENVER — July 12, 2023 — Optiv, the cyber advisory and solutions leader, has published a report based on a recent survey...
GUEST ESSAY: Why it’s high time for us to rely primarily on passwordless authentication – Source: www.lastwatchdog.com
Source: www.lastwatchdog.com – Author: bacohido By Thierry Gagnon Accessing vital information to complete day-to-day tasks at our jobs still requires using a password-based system at most...
Security Affairs newsletter Round 429 by Pierluigi Paganini – International edition – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Privacy Overview This website uses cookies to improve your experience while you navigate through the website. Out of these cookies,...