Source: www.govinfosecurity.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Fraud Risk Management Cyber Police Raid More Than a Dozen Call Centers Staffed by...
Month: June 2023
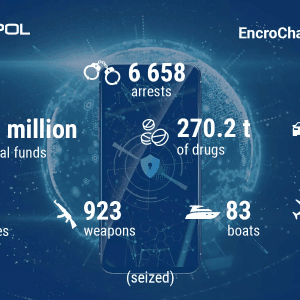
EncroChat Disruption Leads to Arrest of Over 6,000 Suspects – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Government European Authorities Also Confiscated 900 Million Euros Plus Drugs and Weapons Akshaya Asokan...
Hackers Use PindOS Javascript Dropper to Deploy Bumblebee, IcedID Malware – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Livia Gyongyoși Threat actors use a new strain of JavaScript dropper that deploys malware like Bumblebee and IcedID and has a low...
New Mockingjay Process Injection Method Enables Malware Evade EDR Tools – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Livia Gyongyoși Researchers found a new process injection technique dubbed Mockingjay that enables hackers to bypass EDR solutions. The method allows threat...
Saudi Arabia’s Cyber Capabilities Ranked Second Globally – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading The Kingdom of Saudi Arabia has secured second place in the Global Cybersecurity Index in the World...
Generative AI Projects Pose Major Cybersecurity Risk to Enterprises – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading Organizations’ rush to embrace generative AI may be ignoring the significant security threats that large language model...
3 Strategies for Bringing Rigor to Software Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Chris Eng, Chief Research Officer, Veracode We’re in the midst of a transformational shift in software security. Companies will soon bear responsibility...
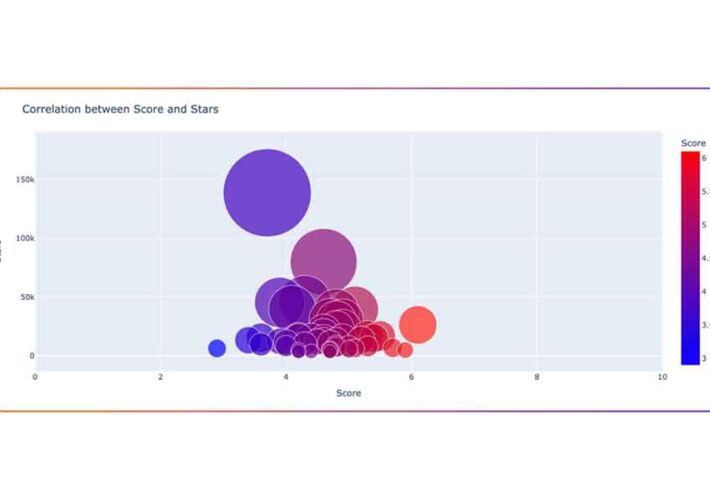
Open Source LLM Projects Likely Insecure, Risky to Use – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading There is a lot of interest in integrating generative AI and other artificial intelligence applications into existing...
Jscrambler Launches JavaScript Scanner for PCI DSS 4.0 Compliance – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading Jscrambler has released a free tool to help companies check the JavaScript code running on their e-commerce...
Protecting Small Businesses From Ransomware on a Budget – Source: www.darkreading.com
Source: www.darkreading.com – Author: Sue Poremba, Contributing Writer If your organization is hit with a ransomware attack, it’s going to cost you. According to Verizon’s 2023...
Cequence Security Adds Generative AI to API Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading API security company Cequence Security has updated its API protection platform with generative AI and no-code security automation...
Experts warn of a spike in May and June of 8Base ransomware attacks – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Researchers warn of a massive spike in May and June 2023 of the activity associated with the ransomware group named 8Base....
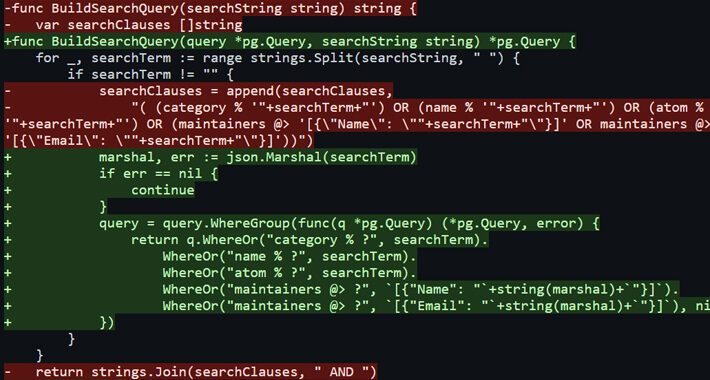
Critical SQL Injection flaws in Gentoo Soko can lead to Remote Code Execution – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini SQL injection vulnerabilities in Gentoo Soko could lead to remote code execution (RCE) on impacted systems. SonarSource researchers discovered two...
EncroChat dismantling led to 6,558 arrests and the seizure of $979M in criminal funds – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Europol announced that the takedown of the EncroChat encrypted chat network has led to the arrest of 6,558 people and...
Mockingjay process injection technique allows EDR bypass – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Mockingjay is a new process injection technique that can be exploited to bypass security solutions to execute malware on compromised...
Andariel’s silly mistakes and a new malware family – Source: securelist.com
Source: securelist.com – Author: GReAT Introduction Andariel, a part of the notorious Lazarus group, is known for its use of the DTrack malware and Maui ransomware...
U.K. Cyber Thug “PlugwalkJoe” Gets 5 Years in Prison – Source: krebsonsecurity.com
Source: krebsonsecurity.com – Author: BrianKrebs Joseph James “PlugwalkJoe” O’Connor, a 24-year-old from the United Kingdom who earned his 15 minutes of fame by participating in the...
EncroChat Disruption Leads to Arrest of Over 6,000 Suspects – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Government European Authorities Also Confiscated 900 Million Euros Plus Drugs and Weapons Akshaya Asokan...
Application Security Testing vs. API Security Testing – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 API Security How They Differ & How Noname Security Active Testing Helps Your Business Shift Left Shay Levi • June 27,...
Critical Vendor Risk Considerations for AI Use in Healthcare – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Artificial Intelligence & Machine Learning , Governance & Risk Management , Next-Generation Technologies & Secure Development Damian Chung of Netskope on...
Ukraine Cracks Down on Investment Scams, Raids Call Centers – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Fraud Risk Management Cyber Police Raid More Than a Dozen Call Centers Staffed by...
Extortion Group Clop’s MOVEit Attacks Hit Over 130 Victims – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 3rd Party Risk Management , Fraud Management & Cybercrime , Governance & Risk Management Known Victims Now Include New York City...
Cyera Raises $100M to Bring Data Protection to Hybrid Cloud – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Big Data Security Analytics , Data Loss Prevention (DLP) , Endpoint Security Accel-Led Series B Funding Will Help Defend Data in...
5 Things CISOs Need to Know About Securing OT Environments – Source:thehackernews.com
Source: thehackernews.com – Author: . For too long the cybersecurity world focused exclusively on information technology (IT), leaving operational technology (OT) to fend for itself. Traditionally,...
8Base Ransomware Spikes in Activity, Threatens U.S. and Brazilian Businesses – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 28, 2023Ravie LakshmananRansomware / Cyber Threat A ransomware threat called 8Base that has been operating under the radar for over...
Critical SQL Injection Flaws Expose Gentoo Soko to Remote Code Execution – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 28, 2023Ravie LakshmananEndpoint Security / RCE Multiple SQL injection vulnerabilities have been disclosed in Gentoo Soko that could lead to...
15 incredible AI tools that can supercharge your operations – Source: www.cybertalk.org
Source: www.cybertalk.org – Author: slandau EXECUTIVE SUMMARY: An overwhelming majority of business owners, roughly 97%, anticipate that ChatGPT will yield positive business outcomes. However, ChatGPT is...
Windows 10 KB5027293 update released with 3 new features, 14 changes – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Microsoft has released the optional KB5027293 Preview cumulative update for Windows 10 22H2 with three new features and 11 additional...
Windows 11 KB5027303 preview update enables new Moment 3 features – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft has released the June 2023 optional cumulative update for Windows 11, version 22H2, which enables the recently announced new...
Siemens Energy confirms data breach after MOVEit data-theft attack – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Siemens Energy has confirmed that data was stolen during the recent Clop ransomware data-theft attacks using a zero-day vulnerability in...