Source: www.csoonline.com – Author: Effective CISOs need to clearly articulate risk and mitigation strategies in business. They must be clear, precise, and, above all, speak truth...
Month: June 2023
BrandPost: Cisco Secure Access: secure connectivity from anything to anywhere from everywhere – Source: www.csoonline.com
Source: www.csoonline.com – Author: About | Security resilience for the unpredictable to connect and protect every part of your business. Withstand the unforeseen and emerge stronger...
Victim Count in Maryland Ransomware Breach Jumps Fivefold – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Breach Notification , HIPAA/HITECH , Security Operations Atlantic General Hospital Now Says Attack Compromised PHI of Nearly 137,000 Marianne Kolbasuk McGee...
24-Year-Old British Man Sentenced to 5 Years in Twitter Hack – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Cryptocurrency Fraud , Fraud Management & Cybercrime , Social Media US Prosecutors Say He Ran SIM Swap Attack to Steal $794,000...
Generative AI, Cybersecurity Friend or Foe? – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 Shawn Surber Senior Director, Technical Account Management, Tanium Shawn Surber is Senior Director of Technical Account Management at Tanium. Over his...
Monopoly Darknet Market: Suspected Operator Extradited to US – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 FBI: Market Facilitated $18 Million in Illegal Drug Transactions via Cryptocurrency Mathew J. Schwartz (euroinfosec) • June 26, 2023 ...
Irish Government Accused of Trying to Muzzle Privacy Critics – Source: www.govinfosecurity.com
Source: www.govinfosecurity.com – Author: 1 General Data Protection Regulation (GDPR) , Governance & Risk Management , Privacy New Bill Set to Penalize Disclosure of Data Protection...
Windows 11 is getting a built-in passkey manager for Windows Hello – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft is expanding support for passkeys in Windows 11 to make it more secure to log into websites and apps...
Anatsa Android trojan now steals banking info from users in US, UK – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A new mobile malware campaign since March 2023 pushes the Android banking trojan ‘Anatsa’ to online banking customers in the...
New PindOS JavaScript dropper deploys Bumblebee, IcedID malware – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Ionut Ilascu Security researchers discovered a new malicious tool they named PindOS that delivers the Bumblebee and IcedID malware typically associated with...
Hackers steal data of 45,000 New York City students in MOVEit breach – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan The New York City Department of Education (NYC DOE) says hackers stole documents containing the sensitive personal information of up...
Inside Threat Actors: Dark Web Forums vs. Illicit Telegram Communities – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sponsored by Flare The proliferation of cybercrime on the internet has given rise to thousands of criminal communities. These corners of the...
Man charged in US for running ‘Monopoly’ darknet drug market – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A 33-year-old man from Serbia has been extradited from Austria to the United States to face charges of running a...
Suncor Energy cyberattack impacts Petro-Canada gas stations – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Petro-Canada gas stations across Canada are impacted by technical problems preventing customers from paying with credit card or rewards points...
Trojanized Super Mario game used to install Windows malware – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A trojanized installer for the popular Super Mario 3: Mario Forever game for Windows has been infecting unsuspecting players with multiple malware...
Grafana warns of critical auth bypass due to Azure AD integration – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Grafana has released security fixes for multiple versions of its application, addressing a vulnerability that enables attackers to bypass authentication...
GDPR FAIL: US Firm ‘Profiles Half the World’ — it’s Max Schrems Again – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings NYOB accuses TeleSign, Proximus and BICS of misusing phone users’ private data. A web of U.S. and Belgian companies secretly...
How to Measure the Maturity of Your Software Supply Chain – Source: securityboulevard.com
Source: securityboulevard.com – Author: Aaron Linskens In today’s fast-paced software development landscape, organizations face rising challenges to ensure the security, quality, and reliability of the software...
Randall Munroe’s XKCD ‘Garden Path Sentence’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
Is data masking the same as data encryption? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Sushant Rao, SVP of Marketing Data masking and data encryption are two important data security techniques that can help you protect sensitive...
BSidesSF 2023 – Terry O’Daniel – Go Far Together: Building Your Squad – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
Tines Adds Tool to Customize Automated Cybersecurity Workflows – Source: securityboulevard.com
Source: securityboulevard.com – Author: Michael Vizard Tines has added a case management tool to its no-code automation platform that makes it simpler for cybersecurity teams to...
RIP Passwords: Why the Future Is Passwordless – Source: securityboulevard.com
Source: securityboulevard.com – Author: Guest Post Almost every website, app, and user platform now requires usernames and passwords. And for user data to remain secure, passwords...
Adventures in Audits, Part Two: How Business Context Affects the Bottom Line – Source: securityboulevard.com
Source: securityboulevard.com – Author: John Gary Maynard III In a typical software piracy case, a software vendor identifies and then pursues a nefarious stranger who has...
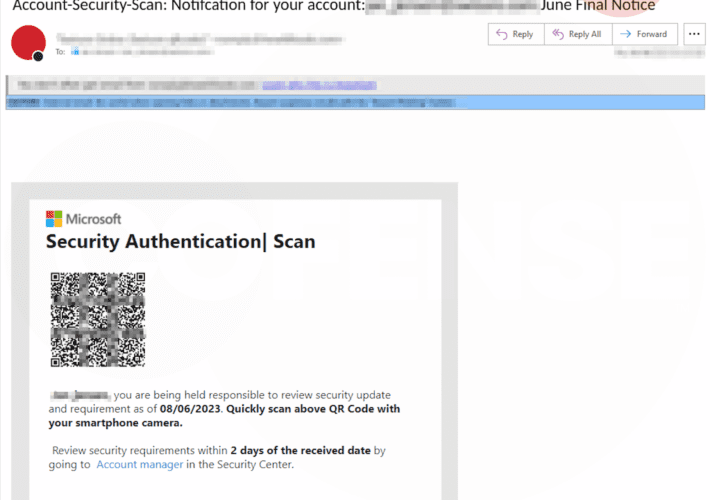
Malicious Actors Utilizing QR Codes to Deploy Phishing Pages to Mobile Devices – Source: securityboulevard.com
Source: securityboulevard.com – Author: Cofense Author: Kian Buckley Maher SEG Bypassed: Microsoft The Cofense Phishing Defense Center (PDC) has noted an increase in the number of malicious emails...
Top 5 Industries Most Vulnerable to Data Breaches in 2023 – Source: securityboulevard.com
Source: securityboulevard.com – Author: ZeroFox Team Today’s interconnected digital landscape has enabled organizations to unlock new levels of efficiency via automation, cloud storage, modernization of legacy...
China-linked APT group VANGUARD PANDA uses a new tradecraft in recent attacks – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini China-linked APT group VANGUARD PANDA, aka Volt Typhoon, was spotted observing a novel tradecraft to gain initial access to target...
Trojanized Super Mario Bros game spreads malware – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Researchers observed threat actors spreading a trojanized Super Mario Bros game installer to deliver multiple malware. Researchers from Cyble Research...
Twitter hacker sentenced to five years in prison for cybercrime offenses – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A U.K. citizen, who was involved in the attack on Twitter in 2020, was sentenced to five years in prison...
Security Affairs newsletter Round 425 by Pierluigi Paganini – International edition – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Privacy Overview This website uses cookies to improve your experience while you navigate through the website. Out of these cookies,...