Source: www.securityweek.com – Author: Kevin Townsend Ann Dunkin is CIO at the US Department of Energy (DOE). Among her responsibilities, she heads IT and oversees cybersecurity....
Day: June 30, 2023
Nokod Snags $8M to Secure Low Code/No-Code Custom Apps – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine An Israeli company called Nokod Security has raised $8 million in early stage capital to work on technology to secure...
New MIT Framework Evaluates Side-Channel Attack Mitigations – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire A group of researchers from the Massachusetts Institute of Technology (MIT) has devised a framework for evaluating the effectiveness of...
White House Outlines Cybersecurity Budget Priorities for Fiscal 2025 – Source: www.securityweek.com
Source: www.securityweek.com – Author: Eduard Kovacs The White House this week released a memorandum outlining the administration’s proposed cybersecurity budget priorities for government departments and agencies...
Pepper and Embedded Insurance Partner on Cyber Insurance For Consumers, SMBs – Source: www.darkreading.com
Source: www.darkreading.com – Author: Stephen Lawton, Contributing Writer Consumers and small-to-midsize businesses (SMBs) that use Internet of Things (IoT) devices to manage smart homes and businesses...
CISA Wants Exposed Government Devices Remediated In 14 Days – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Researchers have discovered hundreds of devices running on government networks that expose remote management interfaces on...
IEC Standardization Leaders Convene in Amsterdam to Review Utility Interworking of Key Standards – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 LONDON, June 29, 2023 /PRNewswire/ — IEC standards have long been considered de facto for the European power grid sector. But the cost and complexity...
Apple Objects to UK Bill That Would Break Encrypted Messaging – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Apple has joined more than 80 technology experts and organizations in an appeal to UK lawmakers to...
Researchers Detail 4 SAP Bugs, Including Flaw in ABAP Kernel – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Organizations running business-critical applications on SAP’s Application Server for ABAP platform technology may want to read...
Over 1500 gas stations disrupted in Canada, after energy giant hacked – Source: www.bitdefender.com
Source: www.bitdefender.com – Author: Graham Cluley Just a moment… Enable JavaScript and cookies to continue Original Post URL: https://www.bitdefender.com/blog/hotforsecurity/over-1500-gas-stations-disrupted-in-canada-after-energy-giant-hacked/ Category & Tags: Data loss,Guest blog,Canada,data breach,energy...
Center for Internet Security, CREST Join Forces to Secure Organizations Globally – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 EAST GREENBUSH, N.Y., June 28, 2023 — The Center for Internet Security, Inc. (CIS®) today announced the launch of a joint initiative with CREST,...
Smashing Security podcast #328: UPS smishing, ChatGPT 101, and storing secret files – Source: grahamcluley.com
Source: grahamcluley.com – Author: Graham Cluley UPS delivers some smishing advice (but have they kept something under wraps?), we ask ChatGPT to take a long hard...
TXOne Networks’ Stellar Solution Safeguards Operational Stability for Organizations in Various Industries – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 IRVING, Texas & TAIPEI, Taiwan — (BUSINESS WIRE) — TXOne Networks, a leader in industrial cybersecurity, announced its Stellar solution for...
WatchGuard Threat Lab Report Reveals New Browser-Based Social Engineering Trends – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 SEATTLE – June 28, 2023 – WatchGuard® Technologies, a global leader in unified cybersecurity, today announced the findings of its latest Internet Security...
Employer Demand for Technology Workers Across Europe Remains on Firm Footing – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 London, June 28, 2023 – While Europe continues to deal with regional economic issues including the effects of inflation and the ongoing...
Cybellum Unveils New Brand, Amplifying Commitment to Team-Centric Product Security – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 TEL AVIV, Israel, June 28, 2023 /PRNewswire/ — Cybellum, creator of the award-winning Product Security Platform for device manufacturers, unveiled today a new...
Different Methods to Secure Your Microsoft Word Documents – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Lance Whitney Image: IB Photography/Adobe Stock You’re creating a document in Microsoft Word with sensitive or important information, and you want to...
8Base Ransomware Attacks Show Spike in Activity – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Lance Whitney on June 29, 2023, 5:08 PM EDT 8Base Ransomware Attacks Show Spike in Activity Ransomware attacks from the 8Base group...
Kaspersky’s New Report Reveals the Top Cyber Threats for SMBs in 2023 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Cedric Pernet A new report from Kaspersky reveals the top cyber threats for SMBs in 2023. Read more about it and how...
How to View Your SSH Keys in Linux, macOS and Windows – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Ray Fernandez If you’re not sure how to view your SSH certificates, this article walks you through the steps on Linux, macOS...
Hiring Kit: IT Audit Director – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Security measures and other IT controls only work if they are implemented consistently, predictably and with integrity. The IT audit director develops...
Redacting Documents with a Black Sharpie Doesn’t Work – Source: www.schneier.com
Source: www.schneier.com – Author: Bruce Schneier We have learned this lesson again: As part of the FTC v. Microsoft hearing, Sony supplied a document from PlayStation...
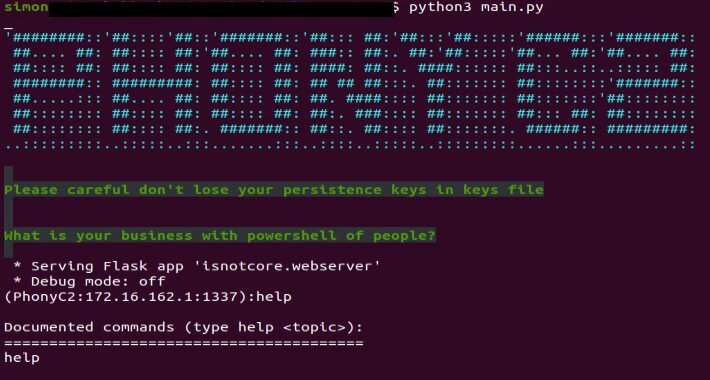
From MuddyC3 to PhonyC2: Iran’s MuddyWater Evolves with a New Cyber Weapon – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 29, 2023Ravie Lakshmanan The Iranian state-sponsored group dubbed MuddyWater has been attributed to a previously unseen command-and-control (C2) framework called...
Fluhorse: Flutter-Based Android Malware Targets Credit Cards and 2FA Codes – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 29, 2023Ravie LakshmananMobile Security / Malware Cybersecurity researchers have shared the inner workings of an Android malware family called Fluhorse....