Source: www.techrepublic.com – Author: Karl Greenberg Okta’s formula for multi-device identity authentication for a hybrid workforce: extract passwords, add ease of passkeys across devices. Amid an...
Day: June 20, 2023
Microsoft Repeatedly Burned in ‘Layer 7’ DDoS – Source: securityboulevard.com
Source: securityboulevard.com – Author: Richi Jennings Time and again this month, “Russian” hackers bring down Microsoft clouds. Microsoft confirms that a group pretending to be hacktivists...
SMS Toll Fraud Brace for the Bill – Source: securityboulevard.com
Source: securityboulevard.com – Author: Abhimanyu Maheswari SMS Fraud: Brace for the Bill Many businesses today underestimate the security risks associated with their telephone systems, even though...
A “cewl” way for API discovery – Source: securityboulevard.com
Source: securityboulevard.com – Author: Dana Epp Imagine this. You’ve been working on a target for some time now, investing to map out all the API endpoints....
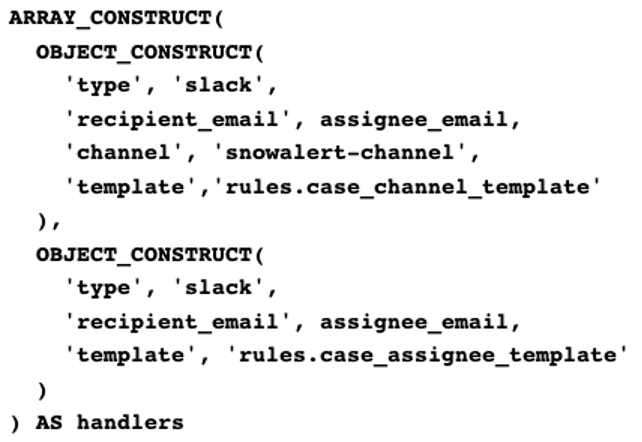
Building an Alert System Using Snowflake – Source: securityboulevard.com
Source: securityboulevard.com – Author: Yiftach Keshet During my time here at Silverfort, I was tasked with building an alert system to send messages from our Snowflake...
BSidesSF 2023 – Michael Bargury – Sure, Let Business Users Build Their Own. What Could Go Wrong? – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Community Chats Webinars Library Home Cybersecurity News Features Industry Spotlight News...
The Future of Email Security: Why Technology Alone Isn’t Enough – Source: securityboulevard.com
Source: securityboulevard.com – Author: Cofense Over the past year, the Cofense Intelligence team saw a whopping 569% increase in malicious phishing emails bypassing standard email security...
WCEU 2023: A Melapress recap – Source: securityboulevard.com
Source: securityboulevard.com – Author: Joel Barbara In early June, the team met in Athens, Greece, for WordCamp Europe. As an event sponsor and a fully remote...
The Comprehensive Guide to File Integrity Monitoring – Source: securityboulevard.com
Source: securityboulevard.com – Author: Mark Allers In order to understand Next-Gen File Integrity Monitoring (NGFIM), we must take a quick peek at the history and origin...
How to Securely Introduce Explicit AUTHORITY-CHECKS into Custom RFC-Enabled Function Modules – Source: securityboulevard.com
Source: securityboulevard.com – Author: ltabo How to Securely Introduce Explicit AUTHORITY-CHECKS into Custom RFC-Enabled Function Modules Compliance Aspects Every SAP application provides business-related authorization objects that...
Understanding Identity Access and Management (IAM) Security – Source: securityboulevard.com
Source: securityboulevard.com – Author: Grip Security Blog A crucial component of protecting your organization, identity access and management (IAM) security has become a trusted cybersecurity best...
#InfosecurityEurope: Certifications Are No Guarantee of Security – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Over reliance on security certifications can lead to a less diverse and less innovative workforce, and processes designed to satisfy auditors...
Smart Pet Feeders Expose Personal Data – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Two security flaws have been discovered in popular smart pet feeders that could lead to data theft and privacy invasion. According...
#InfosecurityEurope: Digital Dependence Means Government and Industry Must Bolster Collaboration – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Businesses need to and move away from the “impossible” goal of total security, and towards cyber resilience, UK government adviser Saj...
Majority of Users Neglect Best Password Practices: Keeper Security – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 The latest Password Management Report by Keeper Security has shed light on the concerning state of password security practices. In particular,...
Over 100,000 ChatGPT Accounts Found in Dark Web Marketplaces – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 More than 100,000 compromised accounts of the OpenAI language model ChatGPT have been found on illicit dark web marketplaces. The discovery...
#InfosecurityEurope: CISOs Must Be Better Marketers and Negotiators – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Enterprise cybersecurity leaders are still underselling themselves to the board and the value they can offer the business, making it harder...
#InfosecurityEurope: How to Weather the Coming Cybersecurity Storm – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Resilience, collaboration and engagement will become vital for organizations hoping to weather a catastrophic cybersecurity “storm” already encircling the world, experts...
#InfosecurityEurope: ThriveDX Launches Cyber Academy for Enterprise to Address Skills Shortages – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 ThriveDX has launched its new Cyber Academy for Enterprise as part of its Human Factor Security suite. The Academy looks to...
#InfosecurityEurope: Michael Johnson Reminds Security Pros Where Success Comes From – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Getting the basics right and understanding yourself are critical foundations to performing consistently well under pressure, Olympic champion Michael Johnson emphasised in...
#InfosecurityEurope: Ironscales Launches GPT-Powered Chat Assistant for Self-Service Threat Reporting – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Following the emergence of large language model-based (LLM) chatbots for the consumer market, organizations increasingly incorporate similar tools for business purposes....
#InfosecurityEurope: Netskope Sets Out to Help Enterprises Safely Use ChatGPT – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Cybersecurity experts are grappling with how to secure use of ChatGPT and other generative AI tools such as Google Bard and...
A bowl full of security problems: Examining the vulnerabilities of smart pet feeders – Source: securelist.com
Source: securelist.com – Author: Roland Sako Introduction In today’s interconnected world, more and more devices are being connected to the internet, including everyday household items like...
Asus Patches Highly Critical WiFi Router Flaws – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ryan Naraine Taiwanese computer hardware manufacturer Asus on Monday shipped urgent firmware updates to address vulnerabilities in its WiFi router product lines...
New Information Stealer ‘Mystic Stealer’ Rising to Fame – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire A new information stealer malware is quickly becoming popular among hackers on prominent underground forums, according to a warning from...
Western Digital Blocks Unpatched Devices From Cloud Services – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire Western Digital has blocked access to its cloud services for devices running firmware versions impacted by a known and critical...
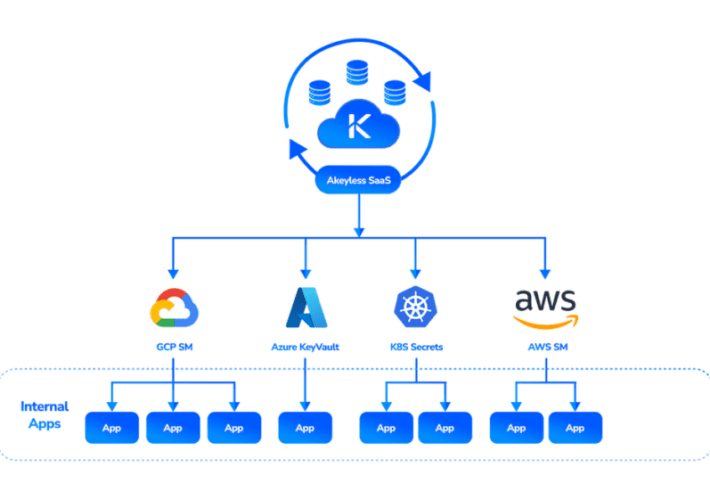
Akeyless Launches SaaS-based External Secrets Manager – Source: www.securityweek.com
Source: www.securityweek.com – Author: Kevin Townsend Secrets are fundamental to cybersecurity. They comprise the secret data that allows individual authorization and access to or between systems....
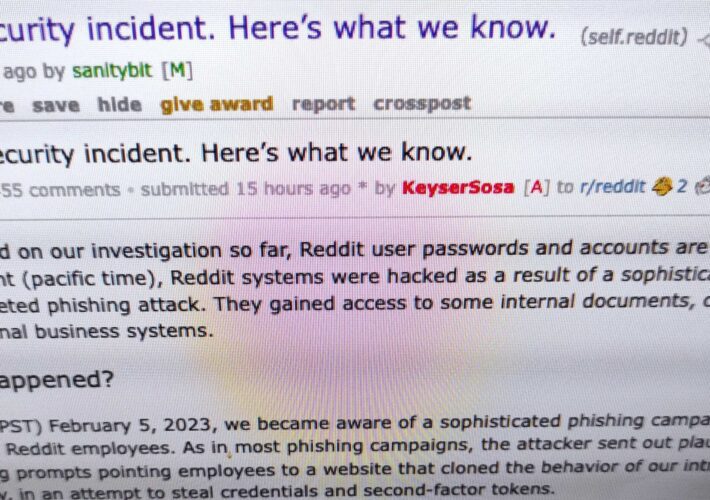
Ransomware Gang Takes Credit for February Reddit Hack – Source: www.securityweek.com
Source: www.securityweek.com – Author: Ionut Arghire The Alphv/BlackCat ransomware gang has taken credit for the February 2023 cyberattack against social media site Reddit, claiming to have...
UK National Crime Agency Head Calls For Hacking Law Updates – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Cybercrime , Fraud Management & Cybercrime , Legislation & Litigation Graeme Biggar Says Law Stymies Prosecutions of Foreign Hackers Akshaya Asokan...
BlackCat Claims Hit on Reddit, Threatens Sensitive Data Leak – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Fraud Management & Cybercrime , Ransomware Group Attempts to Insert Itself in Debate Between Reddit Leadership and Volunteers Mathew J. Schwartz...