Source: www.csoonline.com – Author: About | See why Zscaler’s proxy-based architecture is built on an industry-leading SSE framework to deliver superior security to secure today’s modern...
Day: June 9, 2023
Stealth Soldier: A New Custom Backdoor Targets North Africa with Espionage Attacks – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 09, 2023Ravie LakshmananCyber Espionage / APT A new custom backdoor dubbed Stealth Soldier has been deployed as part of a...
What Is the Principle of Least Privilege (POLP)? – Source: heimdalsecurity.com
Source: heimdalsecurity.com – Author: Andra Andrioaie The principle of least privilege (POLP), also named the “principle of least authority” (POLA) or “the principle of minimal privilege”...
Clop ransomware likely testing MOVEit zero-day since 2021 – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan The Clop ransomware gang has been looking for ways to exploit a now-patched zero-day in the MOVEit Transfer managed file...
Vivaldi is spoofing Edge Browser to bypass Bing Chat restrictions – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Lawrence Abrams The Vivaldi Browser is now spoofing Microsoft Edge on Android devices starting today to bypass browser restrictions Microsoft placed in...
PoC released for Windows Win32k bug exploited in attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Researchers have released a proof-of-concept (PoC) exploit for an actively exploited Windows local privilege escalation vulnerability fixed as part of...
Asylum Ambuscade hackers mix cybercrime with espionage – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas A hacking group tracked as ‘Asylum Ambuscade’ was observed in recent attacks targeting small to medium-sized companies worldwide, combining cyber...
Microsoft OneDrive down worldwide following claims of DDoS attacks – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Sergiu Gatlan Microsoft is investigating an ongoing outage that is preventing OneDrive customers from accessing the cloud file hosting service worldwide, just...
Google Chrome password manager gets new safeguards for your credentials – Source: www.bleepingcomputer.com
Source: www.bleepingcomputer.com – Author: Bill Toulas Google Chrome is getting new security-enhancing features for the built-in Password Manager, making it easier for users to manage their...
City of Dallas Still Clawing Back Weeks After Cyber Incident – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading A month after the city of Dallas experienced a ransomware attack that took down major city services,...
QuSecure Awarded US Army Contract for Post-Quantum Cybersecurity Solutions – Source: www.darkreading.com
Source: www.darkreading.com – Author: 1 SAN MATEO, Calif. — June 8, 2023 — QuSecure™, Inc., a leader in post-quantum cybersecurity (PQC), today announced the United States Army has awarded...
Cybercrooks Scrape OpenAI API Keys to Pirate GPT-4 – Source: www.darkreading.com
Source: www.darkreading.com – Author: Nate Nelson, Contributing Writer, Dark Reading Yesterday, moderators of the r/ChatGPT Discord channel banned a script kiddie who was freely sharing stolen...
Cybersecurity Institute to Open in Saudi Arabia – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dark Reading Staff, Dark Reading An institute branch of the Global Cybersecurity Forum is to be established in Saudi Arabia. As part...
Barracuda Warns All ESG Appliances Need Urgent Rip & Replace – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Despite pushing out patches addressing vulnerabilities in its Email Security Gateway (ESG) appliances in May, today Barracuda...
The Growing Cyber Threats of Generative AI: Who’s Accountable? – Source: www.darkreading.com
Source: www.darkreading.com – Author: Zia Muhammad, Ph.D. Scholar, North Dakota State University Consider a sudden increase in sophisticated malware attacks, advanced persistent threats (APTs), and organizational...
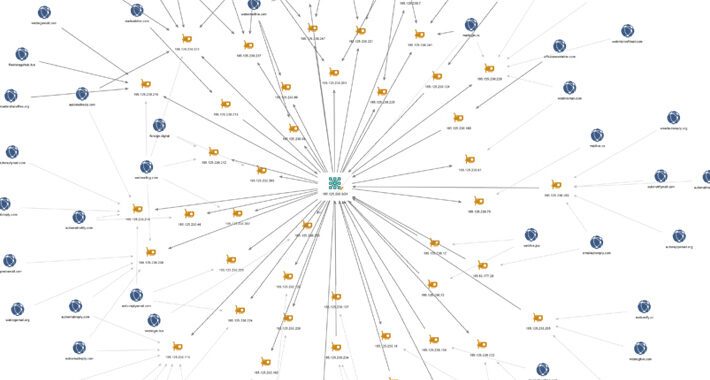
Sophisticated ‘Impulse Project’ Crypto Scam Sprawls With 1,000 Affiliate Sites – Source: www.darkreading.com
Source: www.darkreading.com – Author: Becky Bracken, Editor, Dark Reading Researchers have unraveled a web of more than a thousand scam websites that lead back to Russian-language...
Fighting AI-Powered Fraud: Let the Battle of the Machines Begin – Source: www.darkreading.com
Source: www.darkreading.com – Author: Dr. Ananth Gundabattula, Co-Founder, Darwinium In 2022, US banks processed more than $448 billion in peer-to-peer (P2P) transactions, making these platforms a prime target...
Easily Exploitable Microsoft Visual Studio Bug Opens Developers to Takeover – Source: www.darkreading.com
Source: www.darkreading.com – Author: Jai Vijayan, Contributing Writer, Dark Reading Security researchers are warning about a bug in Microsoft Visual Studio installer that gives cyberattackers a...
60K+ Android Apps Have Delivered Adware Undetected for Months – Source: www.darkreading.com
Source: www.darkreading.com – Author: Elizabeth Montalbano, Contributor, Dark Reading More than 60,000 malicious Android apps targeted global users worldwide for more than six months with adware...
Espionage Attacks in North Africa Linked to “Stealth Soldier” Backdoor – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 A series of highly-targeted espionage attacks in North Africa has been linked to a previously undisclosed modular backdoor called “Stealth Soldier.”...
Pharmaceutical Giant Eisai Hit By Ransomware Incident – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Japanese pharmaceutical company Eisai announced on Tuesday that the Eisai Group has fallen victim to a ransomware incident which occurred on Saturday,...
Microsoft Brings OpenAI Tech to US Agencies – Source: www.infosecurity-magazine.com
Source: www.infosecurity-magazine.com – Author: 1 Microsoft has announced a new integration of OpenAI technology into its services, aimed at empowering US government agencies with enhanced insights...
Experts Unveil Exploit for Recent Windows Vulnerability Under Active Exploitation – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 08, 2023Ravie LakshmananEndpoint Security / Zero-Day Details have emerged about a now-patched actively exploited security flaw in Microsoft Windows that...
Clop Ransomware Gang Likely Aware of MOVEit Transfer Vulnerability Since 2021 – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 08, 2023Ravie LakshmananRansomware / Zero-Day The U.S. Cybersecurity and Infrastructure Security Agency (CISA) and Federal Bureau of Investigation (FBI) have...
How to Improve Your API Security Posture – Source:thehackernews.com
Source: thehackernews.com – Author: . Jun 08, 2023The Hacker NewsAPI Security / DevSecOps APIs, more formally known as application programming interfaces, empower apps and microservices to...
Best VPNs for small business in 2023 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Cedric Pernet on June 8, 2023, 4:00 PM EDT Best VPNs for small business in 2023 Looking for the best VPN services...
Cisco LIVE 2023: AI and security platforms innovations take center stage – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Karl Greenberg Image: Cisco Organizations worldwide are dealing with short-staffed security operations, and a security parasol that stitches together numerous single-point solutions...
This 18-course ethical hacking bundle is under $50 – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: TechRepublic Academy on June 8, 2023, 8:41 AM EDT This 18-course ethical hacking bundle is under $50 Ethical hacking is a great...
Google Chrome: Security and UI tips you need to know – Source: www.techrepublic.com
Source: www.techrepublic.com – Author: Google’s Chrome web browser held a 64.92% command of the global browser market share in April 2023. That means more users are...