Source: www.schneier.com – Author: Schneier.com Webmaster About Bruce Schneier I am a public-interest technologist, working at the intersection of security, technology, and people. I’ve been writing...
Day: May 14, 2023
The latest variant of the RapperBot botnet adds cryptojacking capabilities – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini FortiGuard Labs Researchers spotted new samples of the RapperBot botnet that support cryptojacking capabilities. FortiGuard Labs researchers have discovered new...
Capita warns customers to assume that their data was stolen – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini UK outsourcing giant Capita is informing customers that their data may have been stolen in the cyberattack that hit the...
Security Affairs newsletter Round 419 by Pierluigi Paganini – International edition – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Privacy Overview This website uses cookies to improve your experience while you navigate through the website. Out of these cookies,...
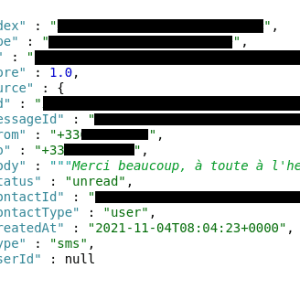
Personal info of 90k hikers leaked by French tourism company La Malle Postale – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini La Malle Postale, a transportation company serving hikers on popular hiking trails in France, leaked personal data and private messages...
Data of more than 2M Toyota customers exposed in ten years-long data breach – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini A data breach disclosed by Toyota Motor Corporation exposed info of more than 2 million customers for ten years Toyota...
USENIX Enigma 2023 – Kelly Shortridge – ‘The Very Hungry Defender: Metamorphosing Security Decision-Making By Incorporating Opportunity Cost’ – Source: securityboulevard.com
Source: securityboulevard.com – Author: Marc Handelman Security Boulevard The Home of the Security Bloggers Network Original Post URL: https://securityboulevard.com/2023/05/usenix-enigma-2023-kelly-shortridge-the-very-hungry-defender-metamorphosing-security-decision-making-by-incorporating-opportunity-cost/ Category & Tags: Security Bloggers Network,appsec education,cybersecurity...
The Ultimate Guide to Multi-Factor Authentication – Source: securityboulevard.com
Source: securityboulevard.com – Author: service The Ultimate Guide to Multi-Factor Authentication The Ultimate Guide to Multi-Factor Authentication The Importance of Multi-Factor Authentication The Importance of Multi-Factor...
Scam Intercepters – some thoughts – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Harley Despite no longer being paid to provide consultancy to the IT security industry, I couldn’t resist catching up with an...
Abusing Communities – Source: securityboulevard.com
Source: securityboulevard.com – Author: David Harley I may need to give up social media altogether. I can’t seem to avoid seeing scams in all directions, and...
New ransomware trends in 2023 – Source: securelist.com
Source: securelist.com – Author: GReAT Ransomware keeps making headlines. In a quest for profits, attackers target all types of organizations, from healthcare and educational institutions to...
Not quite an Easter egg: a new family of Trojan subscribers on Google Play – Source: securelist.com
Source: securelist.com – Author: Dmitry Kalinin Every once in a while, someone will come across malicious apps on Google Play that seem harmless at first. Some...
Managed Detection and Response in 2022 – Source: securelist.com
Source: securelist.com – Author: Kaspersky Security Services SOC, TI and IR posts SOC, TI and IR posts 02 May 2023 minute read Kaspersky Managed Detection and...
What does ChatGPT know about phishing? – Source: securelist.com
Source: securelist.com – Author: Vladislav Tushkanov Can ChatGPT detect phishing links? Hearing all the buzz about the amazing applications of ChatGPT and other language models, our...
APT trends report Q1 2023 – Source: securelist.com
Source: securelist.com – Author: GReAT For more than five years, the Global Research and Analysis Team (GReAT) at Kaspersky has been publishing quarterly summaries of advanced...
Tomiris called, they want their Turla malware back – Source: securelist.com
Source: securelist.com – Author: Pierre Delcher, Ivan Kwiatkowski Introduction We introduced Tomiris to the world in September 2021, following our investigation of a DNS-hijack against a...
QBot banker delivered through business correspondence – Source: securelist.com
Source: securelist.com – Author: Victoria Vlasova, Andrey Kovtun, Darya Ivanova In early April, we detected a significant increase in attacks that use banking Trojans of the...
Uncommon infection methods—part 2 – Source: securelist.com
Source: securelist.com – Author: GReAT Introduction Although ransomware is still a hot topic on which we will keep on publishing, we also investigate and publish about...
Following the Lazarus group by tracking DeathNote campaign – Source: securelist.com
Source: securelist.com – Author: Seongsu Park The Lazarus group is a high-profile Korean-speaking threat actor with multiple sub-campaigns. We have previously published information about the connections...
Nokoyawa ransomware attacks with Windows zero-day – Source: securelist.com
Source: securelist.com – Author: Boris Larin Updated April 20, 2023 In February 2023, Kaspersky technologies detected a number of attempts to execute similar elevation-of-privilege exploits on...