Researchers discovered a new malware that fakes legitimate Google Drive extensions to inject malicious scripts and steal cryptocurrency. The new Rilide malware targets Chromium-based browsers like...
Month: April 2023
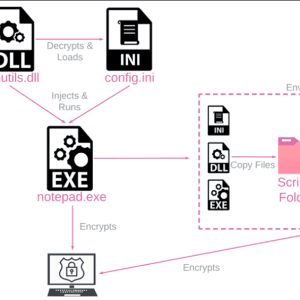
New Threat Uncovered: Rorschach Ransomware – The Fastest Encryptor
Researchers have unveiled a sophisticated and fast ransomware strain called Rorschach, previously undocumented. Malware experts discovered the new ransomware strain after a cyberattack on a U.S.-based company...
HP to patch critical bug in LaserJet printers within 90 days
HP announced in a security bulletin this week that it would take up to 90 days to patch a critical-severity vulnerability that impacts the firmware of...
FBI seizes stolen credentials market Genesis in Operation Cookie Monster
The domains for Genesis Market, one of the most popular marketplaces for stolen credentials of all types, were seized by law enforcement earlier this week as...
Rockstar fixes Red Dead Redemption 2 game broken by Windows update
Microsoft says Rockstar Games has addressed a known issue affecting its launcher, causing the Red Dead Redemption 2 (RRD2) game to no longer launch on some...
ALPHV ransomware exploits Veritas Backup Exec bugs for initial access
An ALPHV/BlackCat ransomware affiliate was observed exploiting three vulnerabilities impacting the Veritas Backup product for initial access to the target network. The ALPHV ransomware operation emerged in December...
Cloud Visibility and Port Spoofing: the “Known Unknown”
By Stephen Goudreault, Cloud Security Evangelist, Gigamon As with all technology, new tools are iterations built on what came before and classic network logging and metrics...
Industrial Defender Launches Phoenix: OT Visibility & Security Solution for Small to Midsized Operations
FOXBOROUGH, Mass., April 4, 2023 /PRNewswire/ — Industrial Defender, the leading provider of OT asset data and cybersecurity solutions for industrial organizations is excited to announce the launch of Phoenix, an...
CardinalOps Launches MITRE ATT&CK Security Layers for Measuring Detection Posture
TEL-AVIV, Israel and BOSTON, April 4, 2023 /PRNewswire/ — CardinalOps, the detection posture management company, today announced a new approach for measuring detection posture and identifying gaps using the MITRE ATT&CK...
F5 Safeguards Digital Services With New AI-Powered App and API Security Capabilities
SEATTLE – F5 (NASDAQ: FFIV) today announced new security capabilities to give customers comprehensive protection and control in managing apps and APIs across on-premises, cloud, and edge...
Law Firm for Uber Loses Drivers’ Data to Hackers in Yet Another Breach
A law firm representing Uber Technologies has notified an unknown number of its drivers that sensitive data, including their names and Social Security numbers, has been...
eFile Tax Return Software Found Serving Up Malware
An IRS-approved software service for filing taxes electronically, eFile.com, was found to be delivering JavaScript malware just at the height of tax-return season. eFile.com, which was...
Akamai Launches Managed Security Service Updates and New Premium Offering
CAMBRIDGE, Mass., April 4, 2023 /PRNewswire/ — Akamai Technologies, Inc. (NASDAQ: AKAM), the cloud company that powers and protects life online, today introduced an updated managed security service program and premium...
Mysterious ‘Rorschach’ Ransomware Doubles Known Encryption Speeds
What might be the fastest-ever ransomware encryption binary has been spotted in the wild, locking up systems at nearly twice the speed of the notorious LockBit...
15M+ Services & Apps Remain Sitting Ducks for Known Exploits
More than 15 million instances of Internet-connected applications, services, and devices are vulnerable to software flaws that the US government has confirmed are being exploited by...
ALPHV/BlackCat ransomware affiliate targets Veritas Backup solution bugs
An ALPHV/BlackCat ransomware affiliate was spotted exploiting vulnerabilities in the Veritas Backup solution. An affiliate of the ALPHV/BlackCat ransomware gang, tracked as UNC4466, was observed exploiting three vulnerabilities...
Rorschach ransomware has the fastest file-encrypting routine to date
A new ransomware strain named Rorschach ransomware supports the fastest file-encrypting routine observed to date. Check Point Research (CPR) and Check Point Incident Response Team (CPIRT)...
CISA adds Zimbra bug exploited in attacks against NATO countries to its Known Exploited Vulnerabilities catalog
US CISA has added a Zimbra flaw, which was exploited in attacks targeting NATO countries, to its Known Exploited Vulnerabilities catalog U.S. Cybersecurity and Infrastructure Security...
3CX Supply chain attack allowed targeting cryptocurrency companies
Threat actors behind the 3CX supply chain attack have targeted a limited number of cryptocurrency companies with a second-state implant. As of Mar 22, 2023, SentinelOne...
Spring into action and tidy up your digital life like a pro
Spring is in the air and as the leaves start growing again, why not breathe some new life into the devices you depend on so badly?...
Ensuring safe AI: Policy conundrums for a responsible future
Check Point Software’s cyber security evangelist Ashwin Ram shares insights into artificial intelligence, policy development and cyber security. It is clear that the utilization of Generative...
6G for executives: What will the business impact look like?
EXECUTIVE SUMMARY: The next generation of connectivity is on the horizon. It’s expected to be 100X faster than 5G. Possibly 1,000X faster. But it’s not just...
Endpoint security: Challenges, solutions and best practices
By Anas Baig, product manager and cyber security expert with Securiti. Doing business in the public sphere leaves entities open to malicious attacks. A study conducted...
FBI Seizes Bot Shop ‘Genesis Market’ Amid Arrests Targeting Operators, Suppliers
Several domain names tied to Genesis Market, a bustling cybercrime store that sold access to passwords and other data stolen from millions of computers infected with...
North Korea Hacking Cryptocurrency Sites with 3CX Exploit
News: Researchers at Russian cybersecurity firm Kaspersky today revealed that they identified a small number of cryptocurrency-focused firms as at least some of the victims of...
That ticking noise is your end users’ laptops
Graham Cluley Security News is sponsored this week by the folks at Kolide. Thanks to the great team there for their support! Here’s an uncomfortable fact:...
Learn how to provide your company with maximum security for $79
on April 4, 2023, 5:44 AM EDT Learn how to provide your company with maximum security for $79 This bundle’s 26 courses cover ethical hacking, certification...
15 Million Systems Are Vulnerable to CISA KEV Flaws
Using the Shodan database, IT security researchers were able to track down 15 million vulnerable systems with vulnerabilities from the US cyber security authority CISA’s Known-Exploited-Vulnerabilities-Catalog...
My Cloud Goes Down While Data Storage Giant Announces Network Breach
Western Digital announced that they discovered a network breach had affected their systems, starting March 26th. Threat actors managed to obtain unauthorized access to several of...
New Rorschach ransomware is the fastest encryptor seen so far
Following a cyberattack on a U.S.-based company, malware researchers discovered what appears to be a new ransomware strain with “technically unique features,” which they named Rorschach. Among the capabilities...