Cloud Security , Incident & Breach Response , Next-Generation Technologies & Secure Development Skyhigh Security’s Rodman Ramezanian on Securing Data from Devices to the Cloud Cal...
Month: April 2023
Overcoming Federal Sector Compliance Regulation Challenges
The sheer volume of federal regulations in place makes it almost impossible for agencies to monitor and comply with all of them, much less understand the...
ISMG Editors: RSA Conference 2023 Preview
Events , RSA Conference , RSA Conference Videos Special Guests Join Editors to Share RSA Predictions, Themes, Coverage Anna Delaney (annamadeline) • April 14, 2023 ...
APT36 Running Espionage Ops Against India’s Education Sector
Fraud Management & Cybercrime , Social Engineering Pakistan-Linked APT Group Using Spear-Phishing to Plant Info Stealer Malware Jayant Chakravarti (@JayJay_Tech) • April 14, 2023 ...
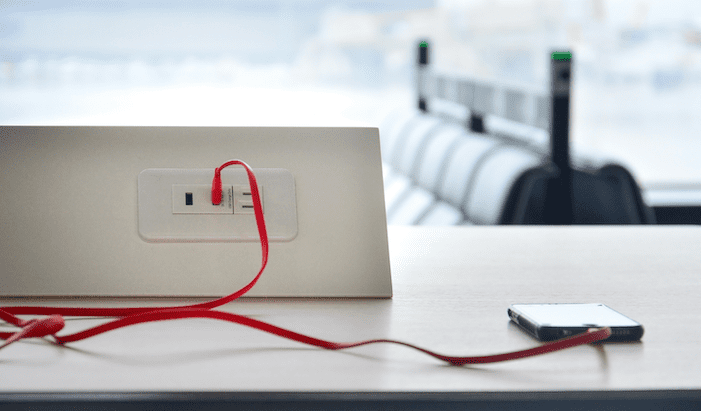
Why is ‘Juice Jacking’ Suddenly Back in the News?
KrebsOnSecurity received a nice bump in traffic this week thanks to tweets from the Federal Bureau of Investigation (FBI) and the Federal Communications Commission (FCC) about...
Russian SolarWinds Culprits Launch Fresh Barrage of Espionage Cyberattacks
As part of its ongoing invasion of Ukraine, Russian intelligence has once again enlisted the services of hacker group Nobelium/APT29, this time to spy on foreign...
Why xIoT Devices Are Cyberattackers’ Gateway Drug for Lateral Movement
Extended IoT devices (xIoT) stand as a perennial favorite for cyberattackers seeking to move laterally and establish persistence within enterprise networks. They’ve got everything the bad...
Software-Dependency Data Delivers Security to Developers
Developers interested in gauging the security of the open source components have an abundant number of choices, but still have to choose to use the information...
Security Is a Revenue Booster, Not a Cost Center
Security has historically been seen as a cost center, which has led to it being given as little money as possible. Many CISOs, CSOs, and CROs...
Bugs in Manarium Play-to-Earn Platform Showcase Crypto-Gaming Insecurity
A proof-of-concept (PoC) hack of the Manarium play-to-earn (P2E) gaming platform allowed researchers to arbitrarily change their scores to win daily tournaments and collect crypto tokens,...
Western Digital Hackers Demand 8-Figure Ransom Payment for Data
After stealing around 10TB of data from Western Digital Corp., the computer drive manufacturer behind digital storage brand SanDisk, hackers are now negotiating a ransom payment...
SASE Market Worth $5.9B by 2028 — Report by MarketsandMarkets™
CHICAGO, April 14, 2023 /PRNewswire/ — The global SASE Market size is projected to grow from USD 1.9 billion in 2023 to USD 5.9 billion by 2028, at a Compound Annual Growth Rate (CAGR) of...
What the Recent Collapse of SVB Means for Privacy
With the recent collapse of Silicon Valley Bank (SVB), we’re seeing a culmination of events leading to a perfect storm for digital bad actors. As businesses...
Friday Squid Blogging: Colossal Squid
Interesting article on the colossal squid, which is larger than the giant squid. The article answers a vexing question: So why do we always hear about...
Upcoming Speaking Engagements
About Bruce Schneier I am a public-interest technologist, working at the intersection of security, technology, and people. I’ve been writing about security issues on my blog...
Hacking Suicide
Hacking Suicide Here’s a religious hack: You want to commit suicide, but it’s a mortal sin: your soul goes straight to hell, forever. So what you...
Gaining an Advantage in Roulette
You can beat the game without a computer: On a perfect [roulette] wheel, the ball would always fall in a random way. But over time, wheels...
Bypassing a Theft Threat Model
Thieves cut through the wall of a coffee shop to get to an Apple store, bypassing the alarms in the process. I wrote about this kind...
Hunting down BlackLotus – Week in security with Tony Anscombe
Microsoft releases guidance on how organizations can check their systems for the presence of BlackLotus, a powerful threat first analyzed by ESET researchers Microsoft has released...
Safety first: 5 cybersecurity tips for freelance bloggers
The much-dreaded writer’s block isn’t the only threat that may derail your progress. Are you doing enough to keep your blog (and your livelihood) safe from...
Shifting the Balance of Cybersecurity Risk – Principles and Approaches for Secure-by-Design – Secure-by-Default – CISA
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
Vice Society ransomware uses new PowerShell data theft tool in attacks
The Vice Society ransomware gang is deploying a new, rather sophisticated PowerShell script to automate data theft from compromised networks. Stealing corporate and customer data is...
Microsoft expands Start menu ads test with new ‘treatments’
Microsoft is testing new ads in the Windows Start menu, or what it describes as “new treatments,” for users logged into local accounts as part of...
Google Chrome emergency update fixes first zero-day of 2023
Google has released an emergency Chrome security update to address the first zero-day vulnerability exploited in attacks since the start of the year. “Google is aware that an exploit for...
Darktrace: Investigation found no evidence of LockBit breach
Cybersecurity firm Darktrace says it found no evidence that the LockBit ransomware gang breached its network after the group added an entry to their dark web...
Russia accuses NATO of launching 5,000 cyberattacks since 2022
The Federal Security Service of the Russian Federation (FSB) has accused the United States and other NATO countries of launching over 5,000 cyberattacks against critical infrastructure...
Police disrupts $98M online fraud ring with 33,000 victims
Europol and Eurojust announced today the arrest of five individuals believed to be part of a massive online investment fraud ring with at least 33,000 victims who...
For cybercriminal mischief, it’s dark web vs deep web
Image: oz/Adobe Stock Threat actors are consolidating their use of encrypted messaging platforms, initial access brokers and generative AI models, according to security firm Cybersixgill’s new...
As Tax Day approaches, Microsoft warns accounting firms of targeted attacks
Accountants are being warned to be on their guard from malicious hackers, as cybercriminals exploit the rush to prepare tax returns for clients before the deadline...
Pentagon leak suspect Jack Teixeira arrested at gunpoint
The US Department of Justice says a member of the US Air Force National Guard has been arrested in connection with a high profile leak of...