Malware that can steal data and commit click fraud has hitched a ride into 60 mobile apps, via an infected third-party library. The infected apps have logged more...
Month: April 2023
Beyond CVEs: The Key to Mitigating High-Risk Security Exposures
In 2022, the National Institute of Standards and Technology reported more than 23,000 new vulnerabilities, the largest spike ever recorded within one calendar year. Alarmingly, this...
Recycled Core Routers Expose Sensitive Corporate Network Info
Cameron Camp had purchased a Juniper SRX240H router last year on eBay, to use in a honeypot network he was building to study remote desktop protocol...
As Consumer Privacy Evolves, Here’s How You Can Stay Ahead of Regulations
Proposition 24, also known as the California Privacy Rights Act (CPRA), went into effect in January. Passed by California voters in November 2020, the CPRA increases...
ZeroFox Acquires LookingGlass
On Monday, ZeroFox announced plans to acquire LookingGlass, a threat intelligence and attack surface management company, for roughly $26 million. ZeroFox provides protection against phishing and...
Global Automotive Cybersecurity Report 2022 – Automotive Cyber Threat Landscape in Light of New Regulations by Upstream
The content you are trying to access is private only to member users of the site. You must have a free membership at CISO2CISO.COM to access...
CISA adds bugs in Chrome and macOS to its Known Exploited Vulnerabilities catalog – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. US Cybersecurity and Infrastructure Security Agency (CISA) added Chrome and macOS vulnerabilities to its Known Exploited Vulnerabilities catalog. U.S. Cybersecurity...
The intricate relationships between the FIN7 group and members of the Conti ransomware gang – Source: securityaffairs.com
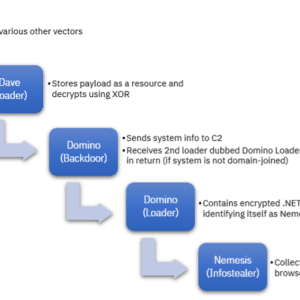
Source: securityaffairs.com – Author: Pierluigi Paganini. A new malware, dubbed Domino, developed by the FIN7 cybercrime group has been used by the now-defunct Conti ransomware gang....
Israeli surveillance firm QuaDream is shutting down amidst spyware accusations – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. The Israeli surveillance firm QuaDream is allegedly shutting down its operations after Citizen Lab and Microsoft uncovered their spyware. Last week...
New QBot campaign delivered hijacking business correspondence – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. Kaspersky researchers warn of a new QBot campaign leveraging hijacked business emails to deliver malware. In early April, Kaspersky experts...
CISA: Why Healthcare Is No Longer Off-Limits for Attackers – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1. Healthcare entities of all types and sizes could be the next targets of major cybersecurity attacks, said Nitin Natarajan, deputy director...
How New Federal Cyber Resources Can Help Healthcare Entities – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1. Healthcare , Industry Specific , Information Sharing CISO Erik Decker Shares New HHS Advisory Group Resources at HIMSS Conference Marianne Kolbasuk...
APAC Panel | Level Up Your Security Stack: EDR vs Endpoint Privilege Management – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1. Sean Boulter Solution Architect, Salt Security Sean Boulter is a technical leader with Salt Security where he helps his customers protect...
US Charges Chinese Officials With Running Troll Farm – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1. Fraud Management & Cybercrime , Social Media Also: Conspiracy to Transmit Interstate Threats and Commit Interstate Harassment David Perera (@daveperera) •...
7 tips for tackling cyber security technical debt
EXECUTIVE SUMMARY: The cyber risk landscape is evolving. Novel attack types are appearing at an unprecedented rate. Cyber criminals are constantly seeking new ways to infiltrate...
Twitter no longer exists, it’s just X Corp. now
EXECUTIVE SUMMARY: In a move sparking intense speculation, Twitter technically “no longer exists” after a merge with X Corp., according to a document submitted to a...
RSAC Fireside Chat: Extending ‘shift left’ to achieve SSCS — ‘software supply chain security’
By Byron V. Acohido One of the nascent security disciplines already getting a lot of buzz as RSA Conference 2023 gets ready to open next week...
It’s 2023 – You MUST Know The SaaS Applications Your Employees Are Using
Organizations should have free access to their SaaS attack layer By Galit Lubetzky Sharon, Co-Founder & CTO, Wing Security While security budgets were not the first...
How to create Portainer teams for restricted development access
on April 17, 2023, 7:03 PM EDT How to create Portainer teams for restricted development access Jack Wallen shows you how to create a team and...
Credential harvesting malware appears on deep web
Image: Adobe Stock/WunderBild Cloud-focused credential harvester and spam utilities, used to illicitly extract an organization’s database of usernames, passwords and emails, are on the rise. By...
Creative Software Maker Affinity Informs Customers of Forum Breach – Source: www.securityweek.com – Author: Eduard Kovacs –
Source: www.securityweek.com – Author: Eduard Kovacs. Category & Tags: Data Breaches,data breach – Data Breaches,data breach UK-based photo editing, graphic design and publishing software developer Affinity...
The Security and Productivity Implications of Low Code/No Code Development – Source: www.securityweek.com – Author: Kevin Townsend –
Source: www.securityweek.com – Author: Kevin Townsend. Category & Tags: Vulnerabilities,Featured,Software,vulnerability – Vulnerabilities,Featured,Software,vulnerability The low code/no code movement provides simplified app generation – but it needs to...
ZeroFox to Acquire Threat Intelligence Firm LookingGlass for $26 Million – Source: www.securityweek.com – Author: Eduard Kovacs –
Source: www.securityweek.com – Author: Eduard Kovacs. Category & Tags: Funding/M&A,Threat Intelligence,M&A,threat intelligence – Funding/M&A,Threat Intelligence,M&A,threat intelligence ZeroFox (ZFOX), which advertises itself as an external cybersecurity solutions...
Swatting as a Service
Swatting as a Service Motherboard is reporting on AI-generated voices being used for “swatting”: In fact, Motherboard has found, this synthesized call and another against Hempstead...
LockBit Ransomware Group Developing Malware to Encrypt Files on macOS – Source: www.securityweek.com – Author: Eduard Kovacs –
Source: www.securityweek.com – Author: Eduard Kovacs. Category & Tags: Ransomware,ransomware – Ransomware,ransomware The notorious LockBit ransomware group is apparently developing a piece of malware that can...
FIN7, Former Conti Gang Members Collaborate on ‘Domino’ Malware
Former members of the Conti ransomware group are compromising systems for follow-up exploits using malware that the financially motivated FIN7 group developed; FIN7 has used the “Domino” tool in...
lockr Raises $2.5M
NEW YORK, April 17, 2023 /PRNewswire/ — lockr, the first consumer-focused platform for digital identity, consent and data, has raised $2.5M in pre-seed funding. Mozilla Ventures, Junction Venture Partners, and...
Google Issues Emergency Chrome Update for Zero-Day Bug
A Google Chrome zero-day vulnerability is under active exploit in the wild, and while details are scarce, users are urged to update their Windows, Mac, and...
NSA’s National Centers for Academic Excellent (NCAE) Cyber Games to Hold National Finals on April 22
Cyber Florida at the University of South Florida – Tampa will host the national championship round of the NCAE Cyber Games on April 22 on the...
Pen Testers Need to Hack AI, but Also Question Its Existence
Samsung has banned some uses of ChatGPT, Ford Motor and Volkswagen shuttered their self-driving car firm, and a letter calling for a pause in training more...