Source: www.securityweek.com – Author: Ionut Arghire. Category & Tags: Cloud Security,Malware & Threats,Kubernetes – Cloud Security,Malware & Threats,Kubernetes Threat actors have been observed abusing Kubernetes Role-Based...
Day: April 25, 2023
Incident response policy
PURPOSE Every enterprise needs to establish a plan of action to assess and then recover from unauthorized access to its network. This policy from TechRepublic Premium...
Google moves to keep public sector cybersecurity vulnerabilities leashed
Image: Sundry Photography/Adobe Stock Google and The Center for Internet Security, Inc., launched the Google Cloud Alliance this week with the goal of advancing digital security...
Beyond Anti-Virus ‘Shark Nets’: Why Current Approaches to Cybersecurity Need to Change
by Ms Camellia Chan, Founder and CEO of Flexxon Shark nets have a notorious reputation: for failing at doing its intended job, giving a false sense...
DNS Layer Security Explained. How It Stops Ransomware and Other Cyberattacks
DNS-Layer Security protects users from threats that arise from inbound and outbound traffic. It refers to monitoring communications between endpoints and the internet at a DNS-layer...
The Incidence of EvilExtractor Malware Rises Across Europe and the U.S.
The number of cyberattacks spreading EvilExtractor malware across Europe and the U.S. is raising. Researchers warn that threat actors used the data theft tool in a...
VirusTotal now has an AI-powered malware analysis feature
VirusTotal announced on Monday the launch of a new artificial intelligence-based code analysis feature named Code Insight. The new feature is powered by the Google Cloud...
Intel CPUs vulnerable to new transient execution side-channel attack
A new side-channel attack impacting multiple generations of Intel CPUs has been discovered, allowing data to be leaked through the EFLAGS register. The new attack was...
Exploit released for PaperCut flaw abused to hijack servers, patch now
Attackers are exploiting severe vulnerabilities in the widely-used PaperCut MF/NG print management software to install Atera remote management software to take over servers. The software’s developer...
KuCoin’s Twitter account hacked to promote crypto scam
KuCoin’s Twitter account was hacked, allowing attackers to promote a fake giveaway scam that led to the theft of over $22.6K in cryptocurrency. The cryptocurrency exchange...
APC warns of critical unauthenticated RCE flaws in UPS software
APC’s Easy UPS Online Monitoring Software is vulnerable to unauthenticated arbitrary remote code execution, allowing hackers to take over devices and, in a worst-case scenario, disabling...
Microsoft 365 search outage affects Outlook, Teams, and SharePoint
Microsoft is investigating an ongoing issue preventing some customers from using the search functionality across multiple Microsoft 365 services. The list of affected services includes but...
Millions of Artifacts, Misconfigured Enterprise Software Registries Are Ripe for Pwning
Many organizations, including some of the world’s largest companies, are at heightened risk of compromise and data theft from misconfigured and poorly secured software registries and...
Tangled Up: ‘Tomiris’ APT Uses Turla Malware, Confusing Researchers
Certain campaigns previously connected to the Russian advanced persistent threat (APT) Turla were actually conducted by what appears to be an entirely separate group researchers have...
Google Workspace Extends Enterprise-Grade Security and Device Management for Hybrid Work With Okta and VMware
SUNNYVALE, Calif., April 24, 2023 /PRNewswire/ — Google Cloud today announced a series of new security alliances to bring more choice, capability, and simplicity to enterprise and public...
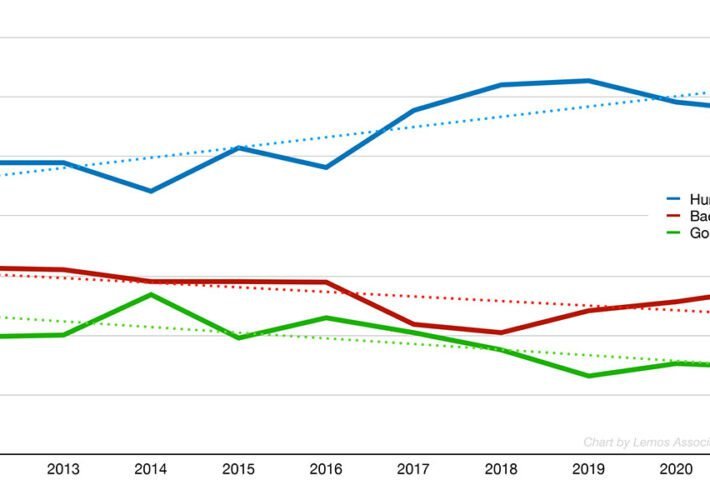
Bot Management Aims to Tame Attacker Automation
Attackers are increasingly automated, with credential stuffing and automated application attacks surging, making the ability to detect, manage and mitigate bot-based requests increasing important. The sector...
Critical Infrastructure Organizations Further Affected in 3CX Breach
Just a month after the North Korea-linked APT hacker group known as Lazarus targeted 3CX in a supply chain attack, Symantec’s researchers have found that two infrastructure...
North Korean Foreign Trade Bank Representative Charged in Crypto Laundering Conspiracies
Two federal indictments were unsealed today in the District of Columbia charging a North Korean Foreign Trade Bank (FTB) representative for his role in separate money...
Google Cloud Announces New Security AI Workbench and Ecosystem Expansion at RSAC 2023
SUNNYVALE, Calif., April 24, 2023 /PRNewswire/ — Announced today at RSA Conference, Google Cloud and Mandiant are combining their cybersecurity partner ecosystems to offer the industry’s most open,...
Qwiet AI Builds a Neural Net to Catch Coding Vulnerabilities
RSA CONFERENCE 2023 – San Francisco – Application security company Qwiet AI announced a new threat intelligence feed for its real-time code security analysis tool PreZero...
ZeroFox to Acquire LookingGlass, Broadening Global Attack Surface Intelligence Capabilities
WASHINGTON, April 17, 2023 (GLOBE NEWSWIRE) — Today, ZeroFox (Nasdaq: ZFOX), an enterprise software-as-a-service leader in external cybersecurity announced a definitive agreement to acquire LookingGlass Cyber...