Source: heimdalsecurity.com – Author: Vladimir Unterfingher Privileged Account and Session Management (PASM) is a new PAM (Privileged Access Management) that focuses on privileged account monitoring and...
Day: April 25, 2023
SLP flaw allows DDoS attacks with an amplification factor as high as 2200 times – Source: securityaffairs.com
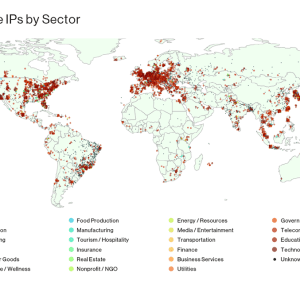
Source: securityaffairs.com – Author: Pierluigi Paganini A flaw in the Service Location Protocol (SLP), tracked as CVE-2023-29552, can allow to carry out powerful DDoS attacks. A...
VMware addressed two zero-day flaws demonstrated at Pwn2Own Vancouver 2023 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini VMware addressed zero-day flaws that can be chained to achieve arbitrary code execution on Workstation and Fusion software hypervisors. VMware...
A new Mirai botnet variant targets TP-Link Archer A21 – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Mirai botnet started exploiting the CVE-2023-1389 vulnerability (aka ZDI-CAN-19557/ZDI-23-451) in TP-Link Archer A21 in recent attacks. Last week, the Zero...
Google researchers found multiple security issues in Intel TDX – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini Google Cloud Security and Project Zero researchers, working with Intel experts, discovered multiple vulnerabilities in the Intel Trust Domain Extensions...
Browser Makers and EU Face Off Over QWACs – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1 Encryption & Key Management , Security Operations , Standards, Regulations & Compliance EU Set to Approve Revised ID Framework to Digitize...
US Deputy AG: Aiding Victims Takes Precedence Over Arrests – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1. Cybercrime , Fraud Management & Cybercrime Lisa Monaco Says Justice Department Values Stopping Cybercrime Over Court Victories Michael Novinson (MichaelNovinson) •...
Webinar | Putting Privileged Access Management, Just-in-Time Access, and Identity Security Together – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1. Thank you for registering with ISMG Complete your profile and stay up to date Need help registering? Contact Support Original Post...
ISMG Editors: Opening Day Overview of RSA Conference 2023 – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1. Events , RSA Conference , Video Emerging AI Tech, Identity Concerns and Latest Threats Are Among the Hot Topics Anna Delaney...
US Indicts Chinese National for Laundering DPRK Crypto – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1. Cryptocurrency Fraud , Cyberwarfare / Nation-State Attacks , Fraud Management & Cybercrime OFAC Adds Men to List of Specially Designated Nationals...
Most Common Connected Devices That Pose Risk to Hospitals – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1. Endpoint Security , Healthcare , Industry Specific Study: Unpatched Nurse Call Systems, Printers and IP Cameras Top the List Marianne Kolbasuk...
Cyberweapons Manufacturer QuaDream Shuts Down
Following a report on its activities, the Israeli spyware company QuaDream has shut down. This was QuadDream: Key Findings Based on an analysis of samples shared...
Cyber security technology integration, intrapreneurship & beyond
In this edited interview excerpt from The Women in Technology Podcast, Check Point Global Cyber Security Warrior and Evangelist Micki Boland speaks with Becky Schneider about...
RSAC Fireside Chat: Turning full attention to locking down the security of ‘open source’
By Byron V. Acohido Software composition analysis — SCA – is a layer of the security stack that, more so than ever, plays a prominent role...
The ESG Manager role & the importance of Environmental, Social & Governance strategy
In this exclusive CyberTalk.org interview, Idan Eden, the ESG Manager for Check Point, shares her expertise on the rapidly growing importance of ESG in corporate decision-making....
#RSAC: US DoJ Prioritizes Victim Support in Cybercrime Crackdown
The US Department of Justice’s (DoJ) approach to disrupting and preventing cybercrime was laid bare by Lisa Monaco, Deputy Attorney General of the United States, during...
Google Authenticator App now supports Google Account synchronization – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. Google announced that its Authenticator app for Android and iOS now supports Google Account synchronization. Google announced that its Google...
Peugeot leaks access to user information in South America – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. Peugeot, a French brand of automobiles owned by Stellantis, exposed its users in Peru, a South American country with a...
North Korea-linked BlueNoroff APT is behind the new RustBucket Mac Malware – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. North Korea-linked APT group BlueNoroff (aka Lazarus) was spotted targeting Mac users with new RustBucket malware. Researchers from security firm...
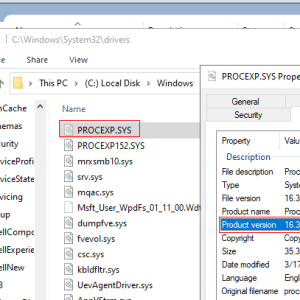
AuKill tool uses BYOVD attack to disable EDR software – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. Ransomware operators use the AuKill tool to disable EDR software through Bring Your Own Vulnerable Driver (BYOVD) attack. Sophos researchers...
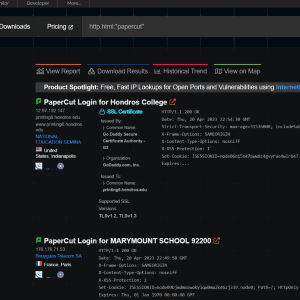
Experts released PoC Exploit code for actively exploited PaperCut flaw – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. Threat actors are exploiting PaperCut MF/NG print management software flaws in attacks in the wild, while researchers released PoC exploit...
EvilExtractor, a new All-in-One info stealer appeared on the Dark Web – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. EvilExtractor is a new “all-in-one” info stealer for Windows that is being advertised for sale on dark web cybercrime forums....
Russian cybercrime group likely behind ongoing exploitation of PaperCut flaws – Source: securityaffairs.com
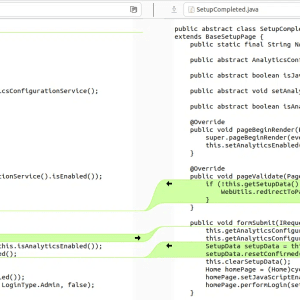
Source: securityaffairs.com – Author: Pierluigi Paganini. Print management software provider PaperCut confirmed ongoing active exploitation of CVE-2023-27350 vulnerability. On April 19th, Print management software provider PaperCut confirmed...
Insider Q&A: OpenAI CTO Mira Murati on Shepherding ChatGPT – Source: www.securityweek.com – Author: Associated Press –
Source: www.securityweek.com – Author: Associated Press. Category & Tags: Artificial Intelligence,AI,ChatGPT,OpenAI,Regulations – Artificial Intelligence,AI,ChatGPT,OpenAI,Regulations OpenAI was building a reputation in the artificial intelligence field but wasn’t...
Google Audit Finds Vulnerabilities in Intel TDX – Source: www.securityweek.com – Author: Ionut Arghire –
Source: www.securityweek.com – Author: Ionut Arghire. Category & Tags: Endpoint Security,Vulnerabilities,Intel – Endpoint Security,Vulnerabilities,Intel Google this week published the results of a nine-month audit of Intel...
Investors Place Early $4 Million Bet on Stack Identity – Source: www.securityweek.com – Author: Ryan Naraine –
Source: www.securityweek.com – Author: Ryan Naraine. Category & Tags: Cloud Security,Funding/M&A – Cloud Security,Funding/M&A Silicon Valley startup Stack Identity on Monday emerged from stealth-mode with $4...
Adrian Stone Joins Moderna as CISO – Source: www.securityweek.com – Author: Ryan Naraine –
Source: www.securityweek.com – Author: Ryan Naraine. Category & Tags: CISO Strategy,Nation-State,CISO,healthcare – CISO Strategy,Nation-State,CISO,healthcare Veteran cybersecurity executive Adrian Stone has been tapped to steer the security...
Huntress: Most PaperCut Installations Not Patched Against Already-Exploited Security Flaw – Source: www.securityweek.com – Author: Ionut Arghire –
Source: www.securityweek.com – Author: Ionut Arghire. Category & Tags: Malware & Threats,Vulnerabilities – Malware & Threats,Vulnerabilities Most Windows and macOS PaperCut installations have not been patched...
New Data Sharing Platform Serves as Early Warning System for OT Security Threats – Source: www.securityweek.com – Author: Eduard Kovacs –
Source: www.securityweek.com – Author: Eduard Kovacs. Category & Tags: ICS/OT,ICS – ICS/OT,ICS Several cybersecurity companies specializing in industrial control systems (ICS) and other operational technology (OT)...
North Korean Hackers Target Mac Users With New ‘RustBucket’ Malware – Source: www.securityweek.com – Author: Ionut Arghire –
Source: www.securityweek.com – Author: Ionut Arghire. Category & Tags: Malware & Threats,Mac malware – Malware & Threats,Mac malware North Korea-linked BlueNoroff hackers have been observed using...