Source: www.troyhunt.com – Author: Troy Hunt I feel like a significant portion of this week’s video went to discussing “the Coinbase breach that wasn’t a Coinbase...
Day: April 24, 2023
ITRC: Lack of Details in Data Breach Notices on the Rise – Source: www.databreachtoday.com
Source: www.databreachtoday.com – Author: 1. Breach Notification , Security Operations , Video James E. Lee Shares 2023 Q1 Data Breach Report Highlights Anna Delaney (annamadeline) •...
Critical Flaw in Inea ICS Product Exposes Industrial Organizations to Remote Attacks – Source: www.securityweek.com – Author: Eduard Kovacs –
Source: www.securityweek.com – Author: Eduard Kovacs. Category & Tags: ICS/OT,Vulnerabilities,Featured,ICS,vulnerability – ICS/OT,Vulnerabilities,Featured,ICS,vulnerability A critical vulnerability found in a remote terminal unit (RTU) made by Slovenia-based industrial...
SolarWinds Platform Update Patches High-Severity Vulnerabilities – Source: www.securityweek.com – Author: Ionut Arghire –
Source: www.securityweek.com – Author: Ionut Arghire. Category & Tags: Vulnerabilities – Vulnerabilities Two high-severity vulnerabilities patched recently in SolarWinds Platform could lead to command execution and...
Guest essay: A roadmap for how — and why — all MSSPs should embrace live patching
By Jim Jackson Patch management has always been time-consuming and arduous. But it gets done, at least to some degree, simply because patching is so crucial...
External Signs of Narcissism – Raising Awareness to Avoid Collateral Damage – Source: www.securityweek.com – Author: Joshua Goldfarb –
Source: www.securityweek.com – Author: Joshua Goldfarb. Category & Tags: Management & Strategy – Management & Strategy Narcissism and narcissistic employees can be a big problem for...
38 Countries Take Part in NATO’s 2023 Locked Shields Cyber Exercise – Source: www.securityweek.com – Author: Eduard Kovacs –
Source: www.securityweek.com – Author: Eduard Kovacs. Category & Tags: Management & Strategy,Risk Management – Management & Strategy,Risk Management The NATO Cooperative Cyber Defence Centre of Excellence...
North Korea’s Kimsuky APT Keeps Growing, Despite Public Outing
Globally, interest has surged around North Korea’s Kimsuky advanced persistent threat group (a.k.a. APT43) and its hallmarks. Still, the group is showing no signs of slowing...
Yellow Pages Canada confirms cyber attack as Black Basta leaks data
Yellow Pages Group, a Canadian directory publisher has confirmed to BleepingComputer that it has been hit by a cyber attack. Black Basta ransomware and extortion gang claims...
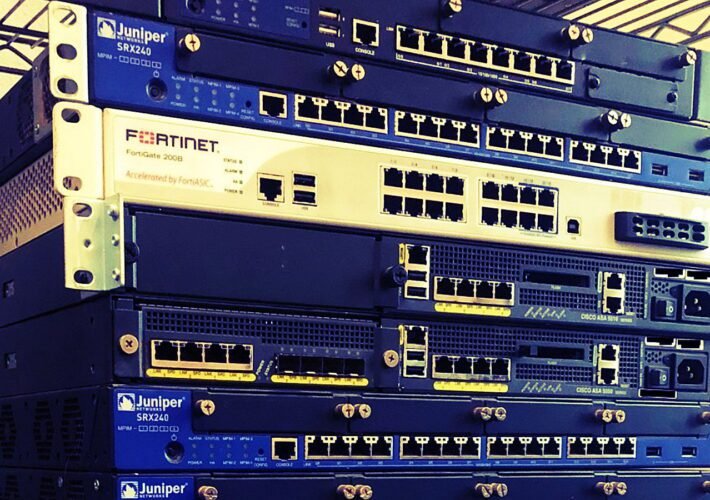
Hackers can breach networks using data on resold corporate routers
Enterprise-level network equipment on the secondary market hide sensitive data that hackers could use to breach corporate environments or to obtain customer information. Looking at several...
UK Threatens End-to-End Encryption
In an open letter, seven secure messaging apps—including Signal and WhatsApp—point out that the UK’s Online Safety Bill could destroy end-to-end encryption: As currently drafted, the...
Decoy Dog malware toolkit found after analyzing 70 billion DNS queries
A new enterprise-targeting malware toolkit called ‘Decoy Dog’ has been discovered after inspecting anomalous DNS traffic that is distinctive from regular internet activity. Decoy Dog helps...
Threat Actors Can Use Old Routers’ Data to Breach Corporate Networks
Discarded routers that are for sale on the secondary market are usually improperly wiped, an experiment shows. Threat actors can reboot sensitive data that haven’t been...
Hackers can hack organizations using data found on their discarded enterprise network equipment – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. ESET researchers explained that enterprise network equipment that was discarded, but not destroyed, could reveal corporate secrets. ESET researchers purchased...
Health insurer Point32Health suffered a ransomware attack – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. Non-profit health insurer Point32Health suffered a ransomware attack and has taken systems offline in response to the incident. Non-profit health...
Experts spotted first-ever crypto mining campaign leveraging Kubernetes RBAC – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. Experts warn of a large-scale cryptocurrency mining campaign exploiting Kubernetes (K8s) Role-Based Access Control (RBAC). Cloud security firm Aqua discovered...
Security Affairs newsletter Round 416 by Pierluigi Paganini – International edition – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. Privacy Overview This website uses cookies to improve your experience while you navigate through the website. Out of these cookies,...
Abandoned Eval PHP WordPress plugin abused to backdoor websites – Source: securityaffairs.com
Source: securityaffairs.com – Author: Pierluigi Paganini. Threat actors were observed installing the abandoned Eval PHP plugin on compromised WordPress sites for backdoor deployment. Researchers from Sucuri...